Digital Development
Test Cases in Software Testing: Structure, Types, and AI Tooling
Test cases are the foundation of any successful software testing effort. They define the inputs, execution steps, and expected results that help verify whether a software application behaves as intended. A well-structured set of test cases in software testing not only ensures higher quality but also enables repeatable, reliable test execution across development cycles.
Understanding how to create, manage, and optimize test cases is essential for developers, QA engineers, and anyone involved in delivering dependable software.
What Are Test Cases in Software Testing?
In software testing, a test case is a documented set of conditions, actions, and expected outcomes used to determine whether a specific feature or functionality works correctly. Each test case includes:
- A clear description of what is being tested
- Preconditions or setup requirements
- Steps to execute the test
- The expected result for comparison
Test cases give structure to the testing process, making it easier to validate application behavior and track defects.
Why Test Cases Matter
Effective test cases serve multiple practical purposes:
Improved Clarity
They provide a clear and repeatable plan for testing specific behaviors and features.
Consistent Validation
With documented steps and expected results, different testers can execute the same tests consistently.
Audit and Traceability
Test cases help track which scenarios were tested and which bugs were identified, aiding quality audits.
Automation Support
Well-defined test cases can be used as the basis for automated testing, reducing manual effort.
Key Elements of Good Test Cases
A good test case should contain the following:
Test Case ID
A unique identifier for easy reference.
Test Description
A clear explanation of the test objective.
Preconditions
Any setup required before running the test.
Execution Steps
Ordered actions to perform the test.
Inputs
Data or parameters needed for the test.
Expected Result
The anticipated outcome to validate correctness.
Postconditions
Any cleanup or conditions after test execution.
Types of Test Cases
Different project needs require different kinds of test cases:
Functional Test Cases
Verify that specific functions of the software work correctly.
Regression Test Cases
Make certain that the new modifications do not disrupt current operations.
Integration Test Cases
Check interactions between multiple components or systems.
Boundary and Negative Test Cases
Test edge conditions and unexpected inputs to verify system robustness.
Usability Test Cases
Evaluate user experience and intuitive behavior.
Ways to Create Impactful Test Cases in Software Testing
Understanding how to write good test cases is a core skill for QA professionals. Follow these steps:
Analyze Requirements
Understand the feature or behavior being tested.
Define Clear Objectives
Each test should focus on a specific expected outcome.
Use Simple Language
Write steps and descriptions in clear, actionable language.
Avoid Duplication
Ensure test cases are unique and do not repeat existing tests unnecessarily.
Review and Update
Continuously review test cases with the team and update them based on application changes.
Common Challenges with Test Cases
Test cases can sometimes become outdated or ineffective if not properly maintained. Common issues include:
- Redundant or duplicate test cases
- Incomplete documentation
- Lack of clarity in steps or expected results
- Poor traceability to requirements
Regular review and maintenance help ensure that test cases remain relevant and useful.
The Role of Automation
Once test cases are well documented, they can serve as a foundation for automated testing. Automation tools can execute predefined test cases repeatedly, providing faster feedback and freeing developers and testers to focus on exploratory and advanced testing tasks.
Conclusion
Test cases form the backbone of any robust software testing strategy. They bring clarity, consistency, and accountability to the testing process while paving the way for automation and higher-quality releases. Well-structured test cases leave little room for ambiguity, enabling both new and experienced team members to execute tests with precision and confidence.
By mastering how to write and manage test cases, teams can improve software reliability, detect defects earlier, and streamline their delivery workflows. This disciplined approach also helps organizations capture critical business requirements and translate them into verifiable conditions that software must meet before release.
AI Testing Tools
AI testing tools are transforming the way modern software teams approach quality assurance. Instead of relying solely on manual scripts and repetitive test execution, AI-driven solutions analyze application behavior, detect patterns, and automatically generate optimized test cases. This significantly reduces testing time while improving overall accuracy and coverage. By leveraging machine learning algorithms, these tools can identify high-risk areas in the codebase, prioritize test scenarios, and even predict potential failures before they impact end users.
Another major advantage of AI in testing is self-healing automation. Traditional automated tests often fail when minor UI or structural changes occur. AI-powered tools adapt to such changes intelligently, minimizing maintenance efforts and reducing flaky tests. They also provide smart insights through analytics dashboards, helping teams make data-driven decisions about release readiness and performance bottlenecks.
As organizations adopt agile and DevOps practices, they increasingly rely on continuous testing. AI testing tools integrate seamlessly into CI/CD pipelines, enabling faster feedback loops and boosting deployment confidence. Ultimately, these tools empower development teams to release reliable, high-quality applications at speed, optimize resources, and lower long-term testing costs.
Digital Development
Digital Marketing: Trends, Benefits, and Why Businesses Need It

Digital marketing is no longer limited to just social media posts or running ads. In 2026, it has become more advanced and data-driven. Businesses now use a combination of search engine optimization (SEO), content marketing, paid advertising, email campaigns, and AI-based analytics to reach their target audience.
With increasing internet users and smartphone usage in India, especially in metro cities like Delhi, digital platforms have become the main source of customer engagement. This makes it important for businesses to stay updated with the latest trends and tools.
Why Businesses in Delhi Are Going Digital
Delhi is one of the biggest business hubs in India. From local markets to global companies, everyone is trying to attract customers online. The shift to digital platforms is happening because:
- Customers search online before making a purchase
- Social media influences buying decisions
- Online ads provide faster results
- Digital marketing is more measurable than traditional methods
Because of these reasons, many businesses prefer hiring a digital marketing agency in Delhi to stay competitive and grow faster.
What Does a Digital Marketing Agency Do?
A professional agency offers complete digital marketing solutions. These services usually include:
- Search Engine Optimization (SEO)
- Pay-Per-Click (PPC) Advertising
- Social Media Marketing
- Content Creation and Blogging
- Website Optimization
- Email Marketing Campaigns
Instead of handling everything on your own, an agency manages all these activities efficiently. This helps businesses focus more on their core operations.
Benefits of Hiring a Digital Marketing Agency
Hiring experts can provide several advantages. First, you get access to skilled professionals who understand the latest tools and strategies. Second, it saves your time and effort, allowing you to focus on business growth.
Another important benefit is cost-effectiveness. Building an in-house team can be expensive, while an agency offers multiple services under one plan. This is why many companies choose a digital marketing agency in Delhi instead of hiring separate specialists.
Do Small Businesses Really Need It?
For example, local SEO helps small shops appear in nearby searches, while social media helps them connect directly with customers. With the right strategy, even a small business can grow quickly using digital platforms.
Challenges of Doing Digital Marketing Alone
Managing digital marketing without professional help can be difficult. Some common challenges include:
- Lack of technical knowledge
- Difficulty in understanding analytics
- Time-consuming processes
- Constant algorithm changes
Without proper expertise, businesses may waste money on ineffective campaigns. That’s why hiring a digital marketing agency in delhi can be a smart decision for better results.
Latest Trends in Digital Marketing for 2026
To stay ahead, businesses must follow the latest trends. Some important trends include:
- AI-powered marketing tools
- Voice search optimization
- Video content dominance
- Personalized marketing campaigns
- Data-driven decision making
Agencies are already using these advanced techniques to improve campaign performance. This makes them more reliable for handling modern marketing needs.
How to Choose the Right Agency
Choosing the right agency is very important. You should look for:
- Experience in your industry
- Transparent work process
- Proven results and case studies
- Clear communication
- Customized strategies
Before making a decision, it is always good to review their website, services, and approach. This helps you understand whether they match your business goals.
When You Might Not Need an Agency
Although agencies offer many benefits, not every business needs one immediately. If you have a very small operation and basic marketing needs, you can start with simple strategies like social media posting or basic SEO. However, as your business grows, managing everything alone becomes difficult. At that stage, hiring a digital marketing agency in Delhi becomes more useful and practical.
How Digital Marketing Platforms Can Help Your Business Grow
If you want to understand complete digital marketing solutions in one place, exploring detailed service pages can be helpful, as they explain various aspects of online marketing in a simple and structured way. Platforms like Your Digital Promoter can help businesses learn about strategies such as SEO, social media marketing, content creation, and paid advertising, making it easier to choose the right approach. By offering clear insights and practical guidance, these platforms support businesses in building a strong online presence, connecting with the right audience, and achieving steady growth in the digital world.
Conclusion
In 2026, digital marketing is not optional—it is essential for business growth. Due to rising competition and shifting customer habits, a robust online presence is essential. While some businesses can manage basic marketing tasks, most companies benefit from expert guidance. A professional digital marketing agency in Delhi can help you create effective strategies, save time, and achieve better results. The key is to understand your business needs and choose the right approach accordingly.
Development
Custom OTT App Development Services: Streaming Platforms
Digital Development
Fast Checkout in eCommerce: Boosting Conversions
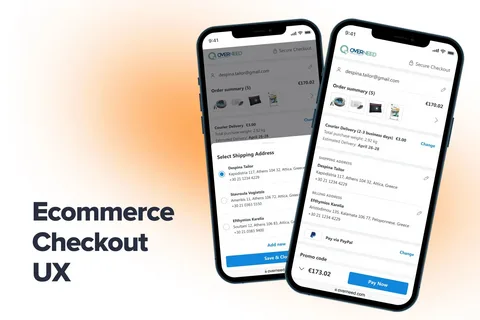
Every second counts in online shopping. Studies consistently show that the longer a customer spends at the checkout stage, the higher the chances they abandon their cart and never return. For businesses investing in mobile commerce, this is not just a UX problem — it is a revenue problem. If you are planning to build or upgrade your shopping platform, partnering with an experienced ecommerce app development company that prioritizes fast checkout is one of the most impactful decisions you can make.
The Cart Abandonment Crisis
Cart abandonment is one of the most expensive challenges in eCommerce. On average, nearly 70% of online shopping carts are abandoned before the purchase is completed. Among the leading reasons? A long, complicated checkout process. This is a core problem that every reputable ecommerce app development company focuses on solving from the very first stage of product design.
When users have to fill out multiple form fields, navigate through five or six pages, create an account before buying, or wait for slow page loads — they leave. And in a world where Amazon has conditioned customers to expect one-click purchases, anything that feels “too many steps” becomes a deal breaker.
Fast checkout directly attacks this problem. The less friction between “I want this” and “I bought this,” the more conversions your app will generate.
Why Speed Is a Competitive Advantage
Speed at checkout is no longer just a nice-to-have feature — it is a business differentiator. Here is why:
1. Mobile Users Have Zero Patience
Mobile commerce accounts for more than half of all eCommerce traffic globally. Smartphone users are often shopping on the go, in fragmented attention spans. A checkout flow that takes two minutes on desktop might feel like an eternity on mobile. Fast, thumb-friendly checkout with minimal input required is essential for capturing mobile conversions.
2. First Impressions Shape Brand Loyalty
The checkout experience is often the final touchpoint before a customer decides whether to return. A smooth, checkout creates a positive emotional association with your brand. A frustrating one does the opposite — and the customer may not give you a second chance.
3. Higher Average Order Values
When customers trust the checkout process and find it easy, they are more likely to add items, accept upsell suggestions, and purchase again. Friction, on the other hand, makes customers second-guess even their original choices.
Key Features That Make Checkout Faster
A skilled ecommerce app development company will build several features into your app to reduce checkout time and improve the conversion rate:
Guest Checkout
Making customers create an account before making a purchase is a conversion killer. The largest obstacle for first-time customers is eliminated by providing a guest checkout option. Once the purchase is over, you can always ask them to register for an account.
Saved Payment & Shipping Information
Returning customers should never have to re-enter their credit card number or shipping address. Secure data storage with tokenization allows users to complete repeat purchases in seconds, not minutes.
One-Page Checkout
Instead of walking users through a multi-step wizard, a single-page checkout layout consolidates all fields — address, payment, order summary — in one scrollable view. This reduces perceived complexity and keeps users focused.
Autofill and Smart Defaults
Intelligent forms that auto-detect city and state from PIN codes, auto-format phone numbers, and prefill known data reduce the number of keystrokes dramatically. These small improvements add up to significant time savings.
Multiple Payment Options
Offering UPI, digital wallets (PhonePe, Google Pay, Paytm), net banking, and cards ensures that customers can pay using whatever method they prefer without switching apps or searching for their card.
Progress Indicators
When multi-step checkout is unavoidable, a clear progress indicator helps users understand how close they are to completing the purchase — reducing drop-off from perceived length.
The Role of Backend Performance
Front-end UX is only half the equation. A fast checkout also depends on backend performance — API response times, payment gateway integration, inventory checks, and order confirmation speed. An unreliable backend can make even a beautifully designed checkout feel slow and untrustworthy.
This is why choosing the right ecommerce app development company matters so much. Skilled developers design checkout processes with performance in mind, using load testing to manage traffic surges during sales events, streamlined API calls, caching techniques, and dependable payment gateway interfaces.
Fast Checkout = Higher ROI
Ultimately, every improvement to checkout speed translates directly to measurable business outcomes:
- Lower cart abandonment rates
- Higher conversion percentages
- Better customer retention
- Improved app store ratings
When you invest in a fast, friction-free checkout experience, you are not spending money on aesthetics — you are investing in revenue generation.
Final Thoughts
eCommerce success is built on trust and convenience. A checkout process that is fast, simple, and secure sends a powerful signal to your customers: we respect your time. Whether you are launching a new shopping app or revamping an existing platform, make checkout speed a non-negotiable priority from day one.
Working with a professional ecommerce app development company that understands both the technical and behavioral dimensions of checkout design will give your app the competitive edge it needs to convert browsers into loyal buyers — consistently.
-
Business3 years ago
Cybersecurity Consulting Company SequelNet Provides Critical IT Support Services to Medical Billing Firm, Medical Optimum
-
Business3 years ago
Team Communication Software Transforms Operations at Finance Innovate
-
Business3 years ago
Project Management Tool Transforms Long Island Business
-
Business3 years ago
How Alleviate Poverty Utilized IPPBX’s All-in-One Solution to Transform Lives in New York City
-
health3 years ago
Breast Cancer: The Imperative Role of Mammograms in Screening and Early Detection
-
Sports3 years ago
Unstoppable Collaboration: D.C.’s Citi Open and Silicon Valley Classic Unite to Propel Women’s Tennis to New Heights
-
Art /Entertainment3 years ago
Embracing Renewal: Sizdabedar Celebrations Unite Iranians in New York’s Eisenhower Park
-
Finance3 years ago
The Benefits of Starting a Side Hustle for Financial Freedom


































