Technology
Inside The Google Secure AI Framework (SAIF)

Introduction
Artificial intelligence is transforming industries faster than any previous technology wave, driving automation, decision-making, and innovation across every sector. Yet as AI systems become more powerful, they also become more vulnerable to exploitation. From model poisoning and data leaks to deepfake manipulation and biased decision engines, AI presents a new category of risk that traditional cybersecurity controls were never designed to handle.
Recognizing this growing challenge, Google introduced the Secure AI Framework (SAIF). A comprehensive blueprint for safeguarding artificial intelligence across its entire lifecycle. SAIF redefines what “responsible AI security” means by combining decades of security expertise with modern risk governance, ensuring that innovation does not come at the expense of safety or ethics.
In this article, Dr. Ondrej Krehel explores how Google’s Secure AI Framework sets a new global benchmark for trust, transparency, and resilience in the age of intelligent systems.
Why AI Security Has Become a Global Priority
AI adoption is accelerating at record speed. Gartner predicts that by 2026, more than 80% of enterprises will have integrated generative AI into their business processes, up from less than 5% in 2023. However, the same speed that fuels innovation also expands the attack surface.
The World Economic Forum lists “malicious AI use” among the top five global risks in the next two years, and according to IBM’s 2024 Cost of a Data Breach Report, the average breach involving AI or automation now costs $5.36 million, nearly 20% higher than non-AI incidents.
These numbers highlight a crucial reality: while AI enables progress, it also magnifies existing vulnerabilities. Without structured governance, machine learning systems can be manipulated, data integrity can be compromised, and automated decisions can propagate systemic bias.
That’s why Google’s Secure AI Framework is more than just another policy. It’s a fundamental shift toward secure-by-design artificial intelligence.
What Is the Google Secure AI Framework (SAIF)?
The Google Secure AI Framework (SAIF) is a layered security and governance model designed to protect AI systems from data ingestion to model deployment. It integrates six guiding principles aimed at reducing vulnerabilities while ensuring ethical and transparent AI usage.
In Google’s words, SAIF is built to “secure the AI ecosystem through shared responsibility.” It draws from decades of Google’s security architecture experience and aligns closely with existing global frameworks such as NIST’s AI Risk Management Framework and ISO/IEC 42001 (AI management system standard).
The framework applies not only to Google’s internal models but also to organizations developing or integrating AI across industries. By providing open guidance, SAIF enables businesses to replicate Google’s defensive posture and adapt it to their own infrastructures.
The Six Core Principles of the Secure AI Framework
1. Secure the AI Supply Chain
AI systems rely heavily on open-source libraries, third-party datasets, and pre-trained models, all of which can be targeted for tampering. SAIF emphasizes end-to-end supply chain security, including code provenance, model validation, and dependency monitoring.
A recent MITRE study revealed that 43% of AI incidents in the last three years stemmed from unverified datasets or compromised libraries, an issue SAIF directly addresses through continuous integrity verification.
2. Implement Strong Identity and Access Controls
AI pipelines often involve multiple users, APIs, and automated agents. SAIF enforces strict identity and access management (IAM) measures to ensure that only authorized entities can train, modify, or deploy AI models.
By adopting zero-trust principles, organizations can prevent unauthorized access to sensitive datasets and model architectures, a vital step in reducing insider threats.
3. Ensure Data Privacy and Protection
Since AI systems learn from massive datasets, ensuring data privacy is critical. SAIF promotes privacy-preserving techniques such as differential privacy, encrypted computation, and anonymization.
According to McKinsey’s 2025 Tech Report, 64% of enterprises plan to increase investment in privacy-enhancing AI technologies, aligning perfectly with SAIF’s approach.
This principle guarantees that AI learns responsibly without compromising user confidentiality.
4. Monitor and Detect AI-Specific Threats
Traditional monitoring tools are insufficient for AI-driven systems. SAIF recommends building specialized detection pipelines that identify adversarial inputs, model drift, and prompt injection attacks in real time.
For example, Google’s own AI Red Team regularly stress-tests its large models using synthetic attacks to uncover vulnerabilities before adversaries do.
This proactive testing culture embodies the SAIF vision, treating AI like a living system that requires continuous security validation.
5. Adopt Secure Deployment and Continuous Testing
Once models go live, continuous verification becomes essential. SAIF urges the adoption of runtime monitoring and secure deployment pipelines, ensuring that updates don’t introduce new vulnerabilities.
Research from Stanford’s AI Index 2024 shows that over 56% of production AI failures occur during deployment or retraining not during initial development. SAIF’s emphasis on runtime safety directly reduces these risks.
6. Promote Transparency and Responsible Governance
Finally, SAIF encourages responsibility, documentation, and explainability in AI systems. Every decision made by a model should be traceable and auditable.
By integrating explainability frameworks and ethics oversight, organizations can align with global mandates like the EU AI Act, which requires transparency across automated decision-making systems.
Google’s framework turns these regulatory expectations into operational standards — ensuring AI remains accountable to both users and society.
Why the Secure AI Framework Matters in 2025
The need for structured AI governance has never been greater. As machine learning penetrates finance, healthcare, marketing, and national security, each misused or unsecured system carries the potential for societal harm.
In 2025, more than 60% of businesses report using AI to handle customer data or strategic decision-making. Without a consistent security baseline, these implementations risk exposing intellectual property or amplifying misinformation.
Google’s Secure AI Framework stands out because it merges technical rigor with ethical design, allowing developers and regulators to speak a common language of responsibility. It’s not merely about preventing attacks; it’s about maintaining public trust in an AI-driven world.
How Organizations Can Implement the Secure AI Framework
For most companies, implementing SAIF begins with evaluating their current AI maturity and identifying areas of risk.
A cybersecurity consultant typically guides this process through structured assessments, mapping existing controls against SAIF’s six principles. The roadmap often includes:
- Inventorying AI assets cataloging datasets, models, and APIs.
- Evaluating data hygiene removing unverified or sensitive information from training pipelines.
- Integrating IAM protocols applying least-privilege access and encryption controls.
- Embedding model monitoring tools detecting bias, drift, and anomalies.
- Establishing governance boards ensuring ethical oversight and compliance documentation.
Organizations that take these steps can align with not just Google’s SAIF but also with broader compliance frameworks such as NIST, GDPR, and ISO AI risk standards.
Benefits of Adopting the Google Secure AI Framework
Implementing the Secure AI Framework delivers multi-dimensional benefits:
- Enhanced trust and transparency: Users and stakeholders gain confidence in the fairness and accountability of AI systems.
- Reduced risk of attacks: Early detection and zero-trust architecture lower exposure to model manipulation and data breaches.
- Regulatory compliance: Organizations can demonstrate adherence to emerging AI legislation.
- Operational efficiency: Standardized processes streamline AI development, testing, and deployment cycles.
- Ethical alignment: Integrating responsibility into every AI stage strengthens brand reputation and user trust.
As Dr. Krehel emphasizes, “Security is not a single control but a mindset. The Secure AI Framework doesn’t just protect technology, it protects credibility.”
Challenges in Implementation
While SAIF offers a robust blueprint, practical challenges remain. Smaller organizations may lack the resources or expertise to deploy AI-specific security infrastructure. Moreover, the evolving nature of AI threats, such as generative model abuse or automated misinformation, means the framework must be continuously updated.
According to Accenture’s 2025 AI Resilience Report, nearly 48% of businesses cite “lack of AI security skills” as their primary obstacle to safe deployment. Engaging experts and adopting modular frameworks like SAIF can bridge this gap.
For this reason, an information security consultant often plays a key role in translating high-level frameworks into actionable, scalable practices.
The Future of Responsible AI Security
The launch of the Google Secure AI Framework represents a milestone in AI governance, but it’s only the beginning.
Future iterations will likely integrate with machine learning security operations (MLSecOps), automating risk management throughout the AI lifecycle.
In parallel, governments and global organizations are developing complementary standards:
- The EU AI Act focuses on risk categorization and transparency.
- The U.S. NIST AI Risk Management Framework emphasizes accountability and resilience.
- OECD AI Principles promote fairness, explainability, and privacy.
As these efforts converge, frameworks like SAIF will form the backbone of a global responsible AI ecosystem, shaping how industries innovate safely.
Conclusion
The Google Secure AI Framework (SAIF) is an important step toward making AI safe, fair, and trustworthy. By focusing on privacy, security, ethics, and accountability, SAIF helps protect users and businesses from the risks that come with AI technology. It ensures that AI systems are built with care and responsibility, so they can be used with confidence.
As AI becomes more a part of our daily lives, frameworks like SAIF will be essential for guiding its growth. Choosing secure and ethical AI is no longer optional—it is necessary for a better and safer future.
Read More: Cybersecurity in a Hyper-Connected World: Protecting Your Digital Life in 2025
Technology
Onion Networking: Rotating Digital Addresses Enhance Privacy
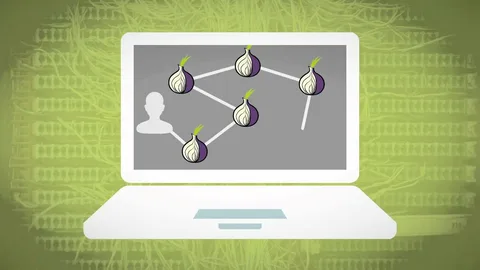
Did you know that some digital addresses are designed to vanish and reappear in a different form just to keep your data safe? In the standard world of the internet, we expect a website name to stay the same forever. The specialized world of Onion Networking uses a different logic. Change is often a sign that a system is working correctly to protect its users and its servers from unwanted attention.
You might notice that a site you visited yesterday is no longer reachable at the same link to this day – this is not always a mistake or a technical failure. It is a core part of how certain anonymous services operate. By shifting their digital location, these services make it much harder for anyone to track where the traffic is going or who is running the hardware behind the scenes.
Basics of Onion Networking
Onion Networking addresses are the long strings of random letters and numbers that end in onion. They do not work like normal websites because they are not part of the central registry that governs the rest of the web – these addresses are actually keys. When you type one into a compatible browser, the software uses that key to build a secret path through multiple different computers across the globe. Each layer of this path is encrypted, which is why people call it an “onion”
The primary goal here is to hide your identity and the identity of the service provider. Because the connection bounces around so much, no single point in the chain knows both where the data starts and where it ends – this setup is perfect for people who live in places with heavy censorship or for those who simply believe that their browsing habits are nobody else’s business. This system operates as a community-driven way to maintain a level of digital privacy that is almost impossible to find on the open web.
Some Addresses Change Frequently
Administrators use rotation as a strategy to avoid attacks. If a link stays static for years, it becomes a permanent target for hackers who want to overwhelm the server with traffic. By changing the address periodically, the site owner can “shake off” these attacks. It is like moving a secret club to a new building every few weeks so that the neighbors never have enough time to complain or figure out what is happening inside.
Another reason for this behavior is to prevent long term mapping of a network. Sophisticated organizations sometimes try to catalog every corner of the private web. Frequent changes make the catalogs become obsolete very quickly. If you find yourself unable to reach a specific forum, you might need a deeper explanation of anonymous browsing platforms to understand where the community has migrated.
Key reasons for address rotation include
- Mitigating large scale denial-of-service attacks.
- Protecting the physical location of the server hosting the site.
- Ensuring that old, cached data in search engines does not lead to dead ends.
- Updating security certificates that are tied to the address itself.
Improving Your Privacy & Safety
Safety is also about where you get your information – Since addresses change, scammers often create fake versions of popular sites to steal login details. You should always verify that the link you are using comes from a trusted source. As an example, many individuals rely on an overview of Tor network systems to find verified directories that keep track of these rotations in real time.
Overcoming Common Connection Hurdles
One common solution involves using specialized relays that hide the fact that you are using a privacy tool at all – these act as secret bridges. If you are struggling with a secure internet navigation setup that won’t load, you may need to look into background on privacy tools like bridges – these help you bypass the initial blocks that prevent your software from reaching the wider network.
Common troubleshooting steps
-
- Restart the browser to generate a fresh identity.
- Request a new set of bridges if your current ones are slow.
- Verify the onion link hasn’t been replaced by a newer version.
Finding Reliable Entry Points
You can also find directories that list various services, from libraries to technical forums. You must be careful. Not every directory is honest. Some might list malicious sites. It is always a good idea to read a review of secure network design or community feedback before you trust a new link.
Technology
SAP Consulting: Drive ERP Success and Digital Transformation

In today’s competitive business environment, organizations are under constant pressure to improve efficiency, reduce operational costs, and make faster decisions. As businesses expand, managing multiple processes through disconnected systems becomes increasingly difficult. This is one of the primary reasons companies are investing in ERP technologies that centralize operations and provide greater visibility across departments. A reliable SAP Consulting Firm in Noida can substantially assist businesses in managing this change.
Whether an organization operates in manufacturing, retail, healthcare, logistics, or professional services, modern ERP solutions provide the foundation needed to support evolving business requirements.
Business Challenges Driving ERP Modernization
Many organizations continue to rely on outdated systems that were designed years ago to support limited business processes. As operations become more complex, these systems often create challenges that affect overall performance.
Common issues include:
- Data scattered across multiple applications
- Manual reporting and approval processes
- Limited visibility into business performance
- Inconsistent information across departments
- Difficulties scaling operations
- Higher maintenance and operational costs
When these challenges persist, decision-making becomes slower and less accurate. Businesses may struggle to identify opportunities, respond to market changes, or maintain operational efficiency. Modern ERP platforms address these concerns by integrating business functions into a centralized environment where information can flow seamlessly between departments.
ERP Success Depends on Consulting Partner
Technology alone does not guarantee successful business transformation. Organizations must ensure that ERP solutions align with their workflows, operational goals, and long-term strategy. This is where experienced consulting professionals provide value. Rather than focusing solely on software configuration, consultants evaluate how processes operate across the organization and identify areas for improvement.
A successful ERP project typically includes:
- Business process assessment
- Requirement gathering
- System architecture planning
- Data migration preparation
- User training and adoption support
- Post-implementation optimization
These activities help organizations avoid common implementation pitfalls while improving the overall return on investment.
Importance of Business Process Alignment
One of the biggest mistakes companies make during ERP projects is attempting to replicate inefficient processes within a new system. While technology can automate workflows, it cannot automatically fix operational inefficiencies.
Before implementation begins, businesses should examine existing workflows and identify opportunities to improve them. Areas that often benefit from optimization include:
Procurement Processes
Inventory Management
Financial Reporting
Automated reporting enables finance teams to generate accurate insights faster while reducing manual effort.
Customer Service Operations
Integrated systems improve access to customer information and support faster issue resolution. By addressing these areas early, businesses create a stronger foundation for ERP success.
Growing Need for SAP Consulting in Delhi
As organizations across the Delhi NCR region continue investing in digital transformation, demand for specialized consulting expertise has grown significantly. Professional SAP Consultancy in Delhi supports businesses that need guidance throughout the ERP lifecycle, from planning and implementation to optimization and ongoing support. Consultants help organizations evaluate their current systems, assess operational requirements, and develop strategies that align technology investments with business goals.
This approach is particularly valuable for companies managing rapid growth or transitioning from legacy systems. Instead of adopting generic implementation models, businesses can benefit from solutions tailored to their specific operational challenges. A structured consulting approach also improves project governance, helping organizations maintain timelines, budgets, and performance expectations throughout implementation.
Workforce Transformation in the Digital Era
Digital transformation is not limited to operational systems. Human resource management has become an increasingly important focus area as businesses seek to improve employee experiences and workforce productivity.
Traditional HR processes often rely on manual administration, disconnected records, and limited reporting capabilities. These challenges can affect employee engagement and make workforce planning more difficult. To address these issues, many organizations are adopting SAP Success Factors Services in India as part of broader digital transformation initiatives.
Modern HR platforms help businesses:
- Simplify recruitment processes
- Improve employee onboarding experiences
- Manage performance evaluations more effectively
- Support learning and development programs
- Enhance workforce planning capabilities
These improvements enable organizations to build stronger teams while creating a more agile and responsive workplace environment.
Preparing for Future Business Growth
The pace of technological change continues to accelerate. Businesses that invest in scalable systems today are better prepared to respond to future market opportunities and operational challenges. ERP modernization should therefore be viewed as a strategic business initiative rather than a standalone technology project.
Successful organizations focus on:
- Continuous process improvement
- Data-driven decision-making
- Employee enablement
- Operational agility
- Scalable infrastructure
These priorities help businesses create sustainable competitive advantages while improving organizational resilience.
Building a Strong Digital Foundation
Modern enterprises require technology environments that support efficiency, transparency, and innovation. ERP systems provide the infrastructure needed to connect departments, streamline workflows, and improve business visibility.
Working with an experienced SAP Consulting Company in Noida allows organizations to approach ERP transformation with greater confidence. From strategic planning and implementation guidance to long-term optimization, the right consulting partner helps businesses maximize the value of their technology investments.
As organizations continue their digital transformation journeys, those that prioritize operational alignment and structured implementation strategies will be better positioned for long-term success in an increasingly competitive marketplace.
Accounting
QuickBooks Running Slow: Causes, Fixes & Improvement

If your QuickBooks Desktop running slow issue is affecting daily accounting tasks, you’re not alone. Many businesses using QuickBooks experience performance problems such as delayed loading, freezing screens, sluggish reports, or slow company file access.
A slow accounting system can reduce productivity, delay payroll processing, interrupt invoicing, and create workflow disruptions. The good news is that most QuickBooks performance issues can be diagnosed and fixed with the right troubleshooting steps.
This guide explains why QuickBooks Running Slow, common causes behind the problem, and practical solutions to improve software performance.
Why Is QuickBooks Desktop Running Slow?
QuickBooks Desktop performance can decline for several reasons. In some cases, the issue comes from large company files. In other situations, outdated software, network problems, or insufficient system resources may be responsible.
You may notice:
- QuickBooks takes a long time to open
- Reports load slowly
- Transactions save with delays
- Company files freeze during use
- Multi-user mode responds slowly
- Screen switching becomes sluggish
These symptoms usually indicate a system configuration, file, or connectivity issue. Understanding the root cause is the first step toward resolving QB running slow problems.
Causes of QuickBooks Desktop Running Slow
Several technical factors can contribute to QuickBooks performance issues.
1. Large Company File Size
One of the most common reasons for QuickBooks Desktop Running Slow is a large company file.
Over time, company files accumulate:
- Customer transactions
- Payroll records
- Inventory history
- Audit logs
- Vendor payments
- Historical accounting data
Large files require more processing power and memory. Businesses with long operational histories or high transaction volume may experience slower performance as file sizes increase.
2. Outdated QuickBooks Version
Running an outdated QuickBooks release can create performance bottlenecks.
Software updates often include:
- Bug fixes
- Speed improvements
- Database optimizations
- Security enhancements
- Compatibility updates
Skipping updates can cause software inefficiencies that affect speed and stability.
3. Insufficient System Resources
QuickBooks Desktop depends on available system memory, processor power, and storage performance.
If your computer has:
- Low RAM
- Limited storage space
- Older processor hardware
- High background application usage
QuickBooks may respond slowly. Accounting software typically performs better on systems meeting or exceeding recommended hardware specifications.
4. Damaged Company Files
Corrupted or damaged company files can significantly impact performance.
Signs of file damage may include:
- Unexpected crashes
- Missing transactions
- Slow loading forms
- Verification errors
- Data integrity warnings
File damage can occur due to sudden shutdowns, hardware issues, or interrupted network access.
5. Multi-User Network Problems
Many businesses use QuickBooks Desktop in multi-user mode.
Network-related issues can contribute to QuickBooks Running Slow performance problems, especially when:
- Server connections are unstable
- Firewalls restrict communication
- Database services malfunction
- Shared folders are misconfigured
Poor network performance often leads to slow file access and delayed synchronization.
Fix QuickBooks Desktop Running Slow
Once you identify possible causes, you can begin troubleshooting.
Update QuickBooks Desktop
Start by ensuring QuickBooks is running the latest release.
Updating the software may resolve:
- Performance bugs
- Compatibility issues
- Known software defects
- Database optimization problems
Keeping accounting software updated is an important maintenance practice.
Verify and Rebuild Company Data
QuickBooks includes built-in utilities to detect and repair file problems. The Verify Data tool checks company file integrity. The Rebuild Data tool attempts to correct detected issues. These utilities may improve speed if performance problems stem from damaged accounting data.
Check System Requirements
Verify that your computer meets QuickBooks Desktop requirements.
Areas to review include:
- Processor capability
- RAM availability
- Hard drive space
- Operating system compatibility
Insufficient hardware resources frequently contribute to QB running slow complaints.
Restart Database Services
Businesses using hosted or multi-user setups should review database server services. Restarting QuickBooks database services may help restore performance.
Check:
- Database Manager status
- Shared folder permissions
- Network connectivity
- Server resource usage
Server optimization often improves multi-user responsiveness.
QB Online Running Slow
Although this article focuses on desktop performance, some users report QB Online Running Slow issues as well. QuickBooks Online performance challenges differ from Desktop because the platform depends on browser and internet conditions.
Common causes of QB Online Running Slow include:
- Browser cache problems
- Slow internet connection
- Excessive browser extensions
- Outdated browsers
- Temporary server latency
Unlike Desktop software, QuickBooks Online relies heavily on web performance factors.
Basic troubleshooting may include:
- Clearing browser cache
- Trying a private browsing window
- Switching browsers
- Updating browser software
- Testing internet speed
Understanding whether the issue involves Desktop or Online versions helps narrow troubleshooting efforts.
Performance Tips to Prevent Issues
Preventive maintenance can reduce the likelihood of future performance problems.
Install Software Updates Regularly
Routine updates improve software efficiency and stability. Maintaining current releases helps minimize compatibility issues.
Monitor Company File Growth
Review company file size periodically. Large files may require optimization strategies before performance noticeably declines.
Maintain System Health
Keep your operating system and hardware environment healthy.
Best practices include:
- Regular disk cleanup
- Adequate free storage
- Driver updates
- Malware scanning
- Hardware monitoring
Use Stable Network Infrastructure
For multi-user environments, reliable networking matters.
Businesses should review:
- Router performance
- Server stability
- Wireless strength
- Firewall configurations
Network consistency can significantly improve QuickBooks responsiveness.
Final Thoughts
Experiencing QuickBooks Desktop Running Slow problems can interrupt accounting workflows, reporting, payroll tasks, and financial management activities. Performance issues often stem from large company files, outdated software, network challenges, insufficient system resources, or file damage.
By understanding the causes and applying appropriate troubleshooting methods, businesses can improve software responsiveness and maintain smoother accounting operations.
Whether you’re dealing with QuickBooks Running Slow, QB running slow, or even QB Online Running Slow, identifying the underlying issue is the most effective path toward restoring performance and improving user experience.
-
Business3 years ago
Cybersecurity Consulting Company SequelNet Provides Critical IT Support Services to Medical Billing Firm, Medical Optimum
-
Business3 years ago
Team Communication Software Transforms Operations at Finance Innovate
-
Business3 years ago
Project Management Tool Transforms Long Island Business
-
Business3 years ago
How Alleviate Poverty Utilized IPPBX’s All-in-One Solution to Transform Lives in New York City
-
health3 years ago
Breast Cancer: The Imperative Role of Mammograms in Screening and Early Detection
-
Sports3 years ago
Unstoppable Collaboration: D.C.’s Citi Open and Silicon Valley Classic Unite to Propel Women’s Tennis to New Heights
-
Art /Entertainment3 years ago
Embracing Renewal: Sizdabedar Celebrations Unite Iranians in New York’s Eisenhower Park
-
Finance3 years ago
The Benefits of Starting a Side Hustle for Financial Freedom

































