Technology
How Zero-Knowledge Proofs Redefine Data Privacy on Blockchain
Introduction
In a world where data is the new oil, privacy has become the rarest commodity. Every online transaction, message, and click generates digital footprints that can be tracked, analyzed, and exploited. While blockchain technology was created to provide transparency and trust, it also inadvertently exposed a critical weakness the loss of confidentiality. As the need for privacy intensifies, one innovation stands out as the ultimate guardian of digital secrecy: the zero-knowledge proof (ZKP).
A zero-knowledge proof is not just a mathematical concept. It’s a revolutionary cryptographic mechanism that redefines how we prove truth in a trustless world. It allows verification without exposure, proof without disclosure, and transparency without vulnerability. Together with blockchain, ZKPs are creating an unbreakable vault for digital data where transactions remain verifiable yet completely private.
What Are Zero-Knowledge Proofs?
Zero-knowledge proofs are cryptographic techniques that let one party (called the prover) show another party (called the verifier) that they know something or did something, without revealing what that “something” is.
For example, let’s say you want to prove you are over 18 without showing your actual age or ID. With a zero-knowledge proof, this is possible. You simply prove the fact (you are over 18) without revealing any personal information.
This idea may sound magical, but it’s based on complex math and algorithms. ZKPs were first introduced in the 1980s, but they are now gaining popularity because of their powerful use in blockchain systems.
Why Does Blockchain Need Zero-Knowledge Proofs?
Blockchain is built on transparency. Every transaction is recorded on a public ledger, which anyone can see. While this brings trust and security, it also creates a privacy problem.
If you make a payment or store personal data on a public blockchain, anyone can see the details unless some form of privacy is added. This is where zero-knowledge proofs become important.
ZKPs allow users to prove that a transaction is valid without showing the amount, the sender, or the receiver. This keeps blockchain systems secure and private at the same time.
The Transparency Paradox of Blockchain
Blockchain’s greatest promise is its transparency. Every transaction is recorded on a public ledger, accessible to anyone, creating a tamper-proof system of trust. However, this same transparency can become a double-edged sword. When sensitive information such as personal identities, financial transactions, or business contracts is recorded on a public blockchain, privacy disappears.
Imagine a future bank built entirely on blockchain. Every deposit, withdrawal, or loan approval is visible to the network. The system may be honest, but it’s also fully exposed. This transparency paradox highlights a fundamental question: how can we maintain trust without sacrificing privacy?
The answer lies in zero-knowledge proofs cryptographic protocols that allow one party to prove a statement’s truth without revealing the underlying data. They make it possible for blockchains to be verifiable yet private, transparent yet secure.
The Essence of Zero-Knowledge Proofs
At its core, a ZKP involves two participants: a prover and a verifier. The prover wants to demonstrate knowledge of a secret (for instance, a password, transaction, or computation) without revealing the secret itself. The verifier can confirm the truth of the claim without needing access to that secret.
This might sound abstract, but it can be understood through a simple analogy. Imagine two doors leading into a cave, connected by a hidden passage. The prover claims to know the code that opens the door, while the verifier waits outside. The prover enters through one door and, if the code is known, exits through the other. After several repetitions, the verifier becomes confident that the prover knows the code — without ever learning what the code actually is.
In blockchain systems, this concept translates into mathematical proofs. Using complex cryptographic techniques, a transaction or computation can be verified as correct without exposing any sensitive inputs. This is what makes the zero-knowledge proof one of the most powerful privacy tools ever developed.
Turning Blockchain into a Secure Vault
Traditional blockchain networks record all transactions publicly. With ZKPs integrated, these records can remain verifiable without revealing their contents. This effectively turns blockchain into an unbreakable vault — open for validation but closed to intrusion.
For example:
- A user can prove they have enough funds for a transaction without showing their total balance.
- A company can prove compliance with a regulation without revealing its internal data.
- A voter can prove participation in a digital election without exposing their identity.
These capabilities transform the blockchain from a system of open transparency to one of selective visibility, where data ownership and control are returned to the user.
Moreover, ZKP-enabled smart contracts can operate privately while maintaining public verifiability. A contract can execute automatically based on private conditions for instance, temperature data, insurance parameters, or financial metrics — without exposing any of those variables to the public.
This fusion of automation, privacy, and accountability makes ZKP a cornerstone of the next-generation blockchain ecosystem.
ZKP and AI: The Privacy-Intelligence Nexus
The story doesn’t end with blockchain. As artificial intelligence (AI) becomes an integral part of decentralized systems, privacy challenges multiply. AI models rely on large datasets often personal, proprietary, or sensitive. Training or running these models on public blockchains could expose private data, model weights, or even intellectual property.
Integrating ZKP with AI provides an elegant solution. With zero-knowledge proofs, an AI model can verify that it performed a computation or reached a prediction correctly without revealing the data it used or the logic it followed. This concept, known as verifiable AI, allows machine learning models to operate transparently in decentralized environments without sacrificing privacy or security.
Imagine an AI system that can prove it made a loan decision fairly, or a model that can verify the authenticity of medical diagnoses without exposing patient data. These are not distant dreams they are real possibilities made achievable by zero-knowledge proof technology.
When combined with blockchain, AI and ZKPs create a triad of digital trust intelligence, transparency, and privacy working together. AI brings adaptability, blockchain provides integrity, and ZKP ensures confidentiality.
Beyond Privacy: ZKP as a Foundation for Digital Trust
While privacy is the most visible advantage, ZKP also bring scalability and efficiency benefits. Techniques like zero-knowledge rollups compress hundreds of blockchain transactions into a single proof, drastically reducing computation and gas costs. This makes networks faster, cheaper, and more accessible — all while preserving privacy.
ZKPs also strengthen the philosophical foundation of decentralized systems. They replace blind trust in intermediaries with mathematical proof — creating a world where trust is computed, not assumed.
In this way, zero-knowledge proofs are not merely a privacy tool; they are a trust engine for the decentralized future. They ensure that digital systems remain accountable, secure, and self-verifiable the very traits that define the promise of Web3.
Types of Zero-Knowledge Proofs
There are two main types of zero-knowledge proofs used in blockchain systems today:
1. zk-SNARKs (Zero-Knowledge Succinct Non-Interactive Arguments of Knowledge)
These are short and fast proofs. They do not require back-and-forth communication between the prover and verifier. zk-SNARKs are already used in many blockchain projects.
2. zk-STARKs (Zero-Knowledge Scalable Transparent Arguments of Knowledge)
These are newer and offer more transparency and security. They don’t require a trusted setup like zk-SNARKs and can handle larger amounts of data.
Both types have their pros and cons, and developers choose the one that fits their project best.
Challenges and Limitations
Even though zero-knowledge proofs offer amazing benefits, they also come with a few challenges:
- Complexity: The math behind ZKPs is very advanced, which makes them harder to build and understand.
- Computing Power: Generating and verifying proofs can take a lot of computer power, especially for large systems.
- Cost: Running ZKPs can be expensive for blockchain networks, though newer methods are reducing these costs over time.
Still, many researchers and companies are working on solving these problems to make ZKPs easier and cheaper to use.
The Future of Data Privacy with Zero-Knowledge Proofs
As digital systems continue to grow, privacy will become even more important. Governments, businesses, and everyday users will want tools that protect their data while still allowing them to use powerful online platforms.
Zero-knowledge proofs offer a new way forward. They can bring privacy to areas like digital payments, online voting, healthcare records, supply chains, and much more.
In fact, many experts believe ZKPs will be a key part of the next generation of the internet — one that is safer, more private, and more trusted.
Conclusion: Privacy as a Right, Not a Luxury
The digital world has reached a tipping point. As we connect more deeply and transact more data, the line between transparency and surveillance becomes dangerously thin. Blockchain alone can’t solve this — it needs the cryptographic shield of ZKP.
The integration of zero-knowledge proofs into blockchain marks the dawn of an unbreakable vault — a new paradigm where users can interact, transact, and compute without ever giving up control of their data.
In this vision of the future, privacy is not an afterthought; it’s the foundation. Trust does not come from exposure, but from verifiable mathematics. And in the heart of this transformation stands the ZKP — silent, invisible, yet unshakably powerful — redefining what it means to be private in a transparent world.
Visit contrank for more Articles
Finance
New IPO Guide: Trends, Risks and Investment Insights India

The Indian primary market continues to be an attractive opportunity for many investors. Many businesses across multiple sectors are seeking to access public markets in order to gain exposure from new capital sources.
For many investors tracking new IPOs has become a key component of participating in capital markets because the overall market’s performance often serves as an indicator of economic confidence, investor sentiment, and anticipated future growth by industry sector.
Additionally, IPO investors today are comprised of more than just large institutions and institutional investors. Retail investors are now tracking subscription trends, listing dates, company fundamentals and industry outlook prior to applying for a public offering. Retail investors also use the information to compare businesses within the same industry as well as investigate long-term trends in equity markets for specific industries when making their own investment decisions regarding IPOs.
This guide discusses trends related to IPOs; key pieces of information that all investors need to watch for; and various factors that influence investor participation in new issues in India at this time.
What is a new IPO?
A new IPO, or Initial Public Offering, refers to a company offering its shares to the public for the first time before becoming listed on recognised stock exchanges.
Once listed, the company’s shares begin trading publicly within the secondary market.
Companies usually launch IPOs to raise funds for purposes such as:
- Business expansion
- Debt reduction
- Infrastructure development
- Operational growth
- Technology investment
- Working capital requirements
For investors, IPO participation provides an opportunity to invest in businesses before regular public market trading begins.

Why investors closely track IPO updates
IPO activity often reflects overall market confidence and business growth expectations.
Investors usually monitor IPO updates because:
- Public issues may indicate sector growth opportunities
- Strong IPO pipelines often reflect healthy market sentiment
- New listings create additional investment choices
- Institutional participation may influence investor confidence
- Listing performance sometimes affects broader market psychology
During active IPO periods, market discussions generally increase across financial platforms, brokerage firms, and investor communities.
Current trends in the indian IPO market
The Indian IPO market continues witnessing strong activity across multiple sectors and business categories.
Several important trends currently influence public market participation.
Increased Retail Participation
Retail investors continue participating actively in IPO subscriptions through online investment platforms and digital applications.
Growth in SME Listings
Small and medium enterprise IPO activity has increased significantly as smaller businesses increasingly access public markets for expansion capital.
Greater Focus on Profitability
Investors now pay closer attention to financial stability, profitability, and realistic business valuations instead of depending only on growth projections.
Technology and Startup Listings
Technology-driven businesses and startup companies continue preparing for public listings across India’s evolving digital economy.
Sector-Based Investor Interest
Sector trends often influence IPO demand, especially during periods of strong economic growth or rising industry-specific optimism.
Key IPO details investors should track
IPO investing involves much more than simply following listing discussions or subscription headlines.
Investors usually benefit from evaluating several important factors before participating in public issues.
Company Financial Performance
Reviewing revenue growth, profitability, debt levels, and cash flow stability may help investors understand business strength more realistically.
Business Model and Industry Position
Understanding how the company generates revenue and competes within its industry helps investors evaluate long-term sustainability.
IPO Valuation
Aggressive pricing may increase investment risk if the valuation appears significantly higher than industry peers or broader market expectations.
Promoter and Management Background
Management quality and promoter credibility often influence investor confidence regarding operational discipline and future business direction.
Purpose of IPO Proceeds
Companies generally explain how they plan to use IPO funds, including expansion projects, debt reduction, or operational investment plans.
Subscription Trends
Strong institutional participation sometimes improves market confidence during the IPO subscription period.
Importance of reading the prospectus
Many first-time investors focus mainly on listing expectations while ignoring the company prospectus.
However, the prospectus contains important operational and financial information including:
- Revenue details
- Business risks
- Industry outlook
- Debt obligations
- Litigation matters
- Promoter information
- Future growth plans
Reading these disclosures carefully may help investors understand whether the business aligns with their financial expectations and risk tolerance.
Role of market sentiment in IPO performance
IPO performance often depends partly on broader market conditions and investor confidence.
Positive market sentiment sometimes improves:
- Subscription demand
- Listing activity
- Institutional participation
- Retail investor confidence
On the other hand, weak market conditions may affect listing performance even when the company demonstrates stable business fundamentals.
This is why investors usually monitor overall market direction before participating actively in public issues.
Connection between sector trends and IPO demand
Sector performance frequently influences investor interest during IPO cycles.
For example, industries experiencing strong growth or favorable economic conditions often attract higher subscription demand.
Similarly, sectors linked with automobile passenger car stocks sometimes receive increased investor attention during periods of rising consumer demand, economic recovery, or manufacturing expansion.
Sector sentiment may influence:
- IPO subscription levels
- Valuation expectations
- Institutional participation
- Long-term investor confidence
Understanding industry cycles may therefore help investors evaluate IPO opportunities more carefully.
Risks associated with IPO investments
Although IPOs attract strong investor interest, they also involve financial and market-related risks.
- Listing Volatility:
Newly listed shares sometimes experience sharp price movement during early trading sessions because of changing investor demand and market sentiment. - Limited Public Trading History:
Unlike established listed companies, IPO-bound businesses may have limited public market history available for long-term performance evaluation. - Valuation Risk:
Certain IPOs may enter markets at aggressive valuations during periods of heightened investor enthusiasm or sector popularity. - Market Condition Risk:
Weak broader market conditions may affect listing performance even if company fundamentals remain stable. - Emotional Investment Decisions:
Fear of missing out often influences first-time investors during highly discussed IPO launches and subscription periods.
Common mistakes investors should avoid
Many investors make avoidable mistakes during active IPO periods.
Applying Without Proper Research
Depending entirely on subscription discussions without reviewing business fundamentals may create unrealistic expectations regarding future performance.
Ignoring Valuation Concerns
Depending Entirely on Grey Market Discussions
Unofficial market speculation does not guarantee actual listing performance or future business stability.
Overlooking Business Risks
Every company faces operational, financial, industry-specific, and competitive risks that investors should understand carefully before applying.
Focusing Only on Short-Term Listing Movement
Many investors concentrate entirely on listing expectations instead of evaluating long-term business quality and operational performance.
Technology has simplified IPO participation
Technology has transformed IPO participation significantly for Indian retail investors.
Today, investors can:
- Apply through mobile applications
- Access IPO calendars online
- Track allotment status digitally
- Read prospectus documents instantly
- Monitor subscription updates in real time
Online investment platforms have simplified access to India’s primary market ecosystem for retail participants.
Importance of long-term perspective in IPO investing
Some investors participate in IPOs mainly for short-term listing activity, while others evaluate businesses from a longer-term perspective.
Strong companies generally sustain growth through:
- Financial discipline
- Operational expansion
- Industry competitiveness
- Business adaptability
- Consistent profitability
This is why evaluating business quality usually matters more than reacting emotionally to short-term market excitement.
How IPO activity reflects economic trends
IPO activity often increases during periods of economic growth, rising market liquidity, and stronger investor participation.
Businesses generally prefer entering public markets when:
- Investor sentiment remains positive
- Capital markets remain active
- Industry conditions appear favorable
- Economic growth expectations improve
Because of this, IPO trends sometimes provide insight into broader economic confidence and business expansion activity within the country.
Conclusion
The Indian IPO market continues attracting strong investor participation as companies across different sectors prepare to enter public markets. Increasing digital accessibility, growing retail participation, and expanding sector opportunities continue supporting IPO activity across India.
However, investors should evaluate financial performance, valuation, business fundamentals, and sector conditions carefully before participating in any new IPO. Whether analyzing technology companies or sectors connected with automobile passenger car stocks, disciplined research and informed decision-making usually remain important for navigating the primary market responsibly.
Management
Secure Software Lifecycle: Shift-Left & Cyber Defense
n today’s digital world, even a minor software vulnerability can expose an entire organization to serious cyber threats. A single insecure line of code can put millions of users and critical data at risk. Because of this growing threat landscape, cybersecurity is no longer just about protecting networks and systems from the outside; it has become a fundamental part of how software itself is built.
The old practice of developing software first and adding Security later is no longer effective. In fact, it often creates more risks than solutions. With major cyber incidents such as the SolarWinds supply chain attack and vulnerabilities like Log4j, organizations have realized that Security must be embedded throughout the entire development process. This is where Secure Software Lifecycle Management (SSLM) plays a crucial role in modern cyber defense.
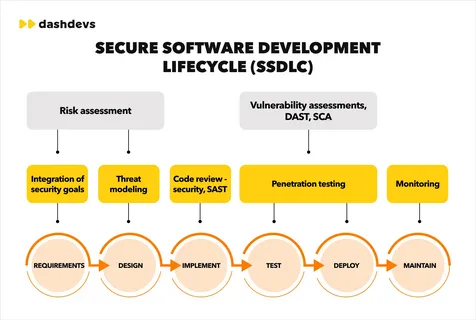
The Shift-Left Approach
Traditionally, security checks were performed only after software development was complete. This resulted in vulnerabilities being identified late in the process, leading to costly and challenging repairs.
Today, organizations are adopting the Shift-Left security approach, integrating security practices into the earliest stages of the Software Development Life Cycle (SDLC). By incorporating security considerations into the planning, design, and coding phases, teams can identify potential weaknesses before they become real problems.
This proactive approach not only reduces costs but also ensures that Security becomes a core part of the software rather than an added feature.
Connecting Development Teams
One of the biggest challenges in modern IT environments is the communication gap between developers and security teams. Developers often prioritize performance, functionality, and speed, while security professionals focus on minimizing risks and vulnerabilities.
Secure Software Lifecycle Management helps bridge this gap by creating a structured framework that enables both teams to collaborate effectively. Certifications such as the Certified Secure Software Lifecycle Professional (CSSLP) equip professionals with the knowledge and methodology to manage Security throughout the software lifecycle—from planning and development to deployment and eventual retirement. Rather than focusing solely on writing secure code, the approach emphasizes managing the entire ecosystem that produces and maintains software.
Securing the Software Supply Chain
Most modern applications are not built entirely from scratch. Developers rely heavily on open-source libraries, third-party frameworks, and external APIs. While these resources accelerate development, they can also introduce hidden security risks.
Secure Software Lifecycle Management ensures that every component used in software development is carefully reviewed, tracked, and monitored for vulnerabilities. Without proper oversight, a single compromised dependency can weaken the Security of the entire application. By implementing structured processes, organizations can maintain greater visibility and control over their software supply chain.
Developing the Next Generation of Security Professionals
As organizations place greater emphasis on secure software development, the demand for skilled cybersecurity professionals continues to grow. Certifications like CSSLP are becoming increasingly valuable for professionals who want to demonstrate expertise in secure software lifecycle practices.
However, mastering the multiple domains covered in the certification requires both theoretical knowledge and practical preparation. Many candidates enhance their preparation through simulation tools that replicate the structure and pressure of the real exam environment. Practice platforms, whether desktop or web-based, allow candidates to test their understanding, identify knowledge gaps, and build confidence before taking the actual certification exam.
Building Skills
As organizations place greater emphasis on secure development practices, the demand for professionals with specialized knowledge continues to grow. Preparing for certifications like CSSLP requires both conceptual understanding and practical exam readiness.
Many candidates improve their preparation by practicing with tools designed to simulate real exam scenarios. For example, using CSSLP Desktop Practice Software allows learners to practice offline in an environment that closely resembles the actual certification exam. This helps them understand the exam structure, manage time effectively, and strengthen their confidence.
At the same time, professionals who prefer flexibility often rely on a CSSLP Web-Based Practice Test, which enables them to practice from any device and continue learning wherever they are. Combining these preparation methods often helps candidates develop a stronger understanding of secure software lifecycle principles.
Security, Compliance, and Business Trust
Secure Software Lifecycle Management is not only important for protecting applications but also for meeting regulatory requirements. Laws and regulations around data protection continue to evolve, and organizations are expected to demonstrate responsible security practices.
Companies that implement secure development processes show customers and partners that they take cybersecurity seriously. In the digital economy, trust plays a major role in long-term business success, and strong security practices help organizations maintain that trust.
Final Thoughts
Cyber defense today starts long before software is deployed. It begins during design discussions, development planning, and coding itself. Organizations that integrate security throughout the entire software lifecycle are better equipped to prevent vulnerabilities and protect their systems from evolving threats.
For developers, security engineers, and project managers, understanding secure software lifecycle management is becoming an essential skill. By prioritizing security from the beginning and continuously improving development practices, organizations can build software that is both innovative and resilient.
Development
Partnership Accounting: Trust, Track Equity, and Maximize Profit

When James and Aamir founded their consultancy firm, they shared more than ambition. They shared trust. One brought financial expertise, the other brought industry connections. In the early days, decisions were made over coffee, expenses were tracked in spreadsheets, and profits were divided with a handshake. The business grew quickly. Clients multiplied. Revenue increased. Yet as the numbers became larger, so did the questions. The partnership had momentum, but it lacked structured Partnership Accounting.
- Why did the capital accounts look uneven?
- How were partner drawings affecting overall cash flow?
- Were profits being distributed fairly?
- What were their individual tax liabilities?
What once felt simple became increasingly complex. The absence of clarity began to create hesitation in decision-making. Their story reflects the experience of many partnerships. Growth introduces financial intricacy. Without a solid accounting structure, uncertainty can quietly undermine even the strongest business relationships.
At Lanop Business and Tax Advisors, we believe that effective Partnership Accounting transforms uncertainty into clarity and shared ambition into measurable profit. It is not merely compliance. It is the economic structure that safeguards collaborations, enhances trust, and promotes sustainable development.
The Foundation of Partnership Accounting
Partnership Accounting refers to the structured process of recording, managing, and reporting the financial activities of a business owned by two or more partners. Unlike sole traders or limited companies, partnerships require special attention to equity distribution, profit sharing, capital accounts, and tax obligations.
Each partner may contribute different levels of capital, expertise, and time. Profit-sharing arrangements may vary. Withdrawals may occur throughout the year. Without a defined accounting system, tracking these elements becomes difficult.
The foundation of strong Partnership Accounting includes:
- Accurate recording of capital contributions
- Clear documentation of profit and loss allocation
- Consistent tracking of partner drawings
- Preparation of reliable financial statements
- Compliance with tax regulations
When these elements operate together, the partnership gains financial visibility and operational confidence.
Building Trust Through Transparency
This is the power of structured Partnership Accounting. Transparent reporting reduces disputes. It aligns expectations. It creates a shared understanding of performance. Professional partnership accounting services ensure that transparency becomes standard practice rather than an afterthought. When partners see the same numbers and understand how they are derived, collaboration strengthens.
Capital Accounts and Partner Equity
One of the distinguishing features of Partnership Accounting is the management of individual capital accounts. Each partner maintains a capital account reflecting their financial stake in the business.
Capital accounts typically include:
- Initial investment
- Additional contributions
- Allocated profits
- Allocated losses
- Withdrawals
Without careful management, discrepancies can arise. For example, if one partner withdraws more frequently than another, equity balances shift. Inaccurate profit allocation may cause misunderstandings to develop.
Professional partnership bookkeeping records these movements precisely and updates them regularly. This clarity becomes essential during expansion, restructuring, or partner transitions. Capital account accuracy protects both the partnership and the individual partners.
Profit Sharing and Fair Allocation
Profit sharing lies at the heart of partnership relationships. Whether profits are distributed equally or based on agreed ratios, accurate allocation is critical.
Structured Partnership Accounting follows the terms set out in the partnership agreement. This may involve:
- Fixed percentage splits
- Interest on capital contributions
- Salary allowances for active partners
- Performance-related distributions
Errors in profit allocation can have tax consequences and strain relationships. Reliable partnership bookkeeping ensures income and expenses are categorized correctly throughout the financial year, making profit calculation accurate and defensible. When allocation processes are clear and consistent, partners focus on growth rather than disputes.
Role of Partnership Bookkeeping
Behind every strong accounting system lies disciplined daily recording. Partnership bookkeeping forms the operational core of effective financial management. Every invoice issued, every supplier payment, every expense claim, and every partner withdrawal must be recorded accurately. Delayed entries or inconsistent categorization create confusion at year’s end.
Professional partnership bookkeeping provides:
- Real-time tracking of income and expenses
- Accurate reconciliation of bank accounts
- Clear classification of partner drawings
- Reliable data for reporting and analysis
- Reduced risk of costly errors
Consistency in bookkeeping ensures that financial statements reflect reality rather than estimates. At Lanop Business and Tax Advisors, we integrate meticulous partnership bookkeeping within our broader partnership accounting services to provide complete financial oversight.
Tax Responsibilities and Compliance
Partnership taxation requires precision. In many jurisdictions, partnerships operate under pass-through taxation. Profits are allocated to partners who report them individually.
Accurate Partnership Accounting ensures:
- Correct preparation of partnership returns
- Accurate reporting of individual profit shares
- Compliance with regulatory requirements
- Identification of legitimate deductions
- Reduced exposure to penalties
Professional partnership accounting services provide structured support to navigate complex tax rules while maintaining full compliance. Clear documentation protects the partnership during audits and ensures each partner meets their obligations confidently.
Managing Growth and Structural Changes
As partnerships evolve, accounting complexity increases. Growth may require additional capital contributions, financing arrangements, or admission of new partners. Each structural change requires adjustments in capital accounts and profit-sharing ratios. Without organized Partnership Accounting, transitions can become contentious.
Strong partnership financial management ensures smooth integration of new partners, accurate valuation of business interests, and fair settlement of exiting partners. Financial clarity simplifies change management and protects long-term stability.
Why Professional Expertise Matters
While some partnerships attempt internal management, complexity often increases with growth. Regulatory requirements evolve. Tax laws change. Financial risks expand. Engaging experienced advisors ensures that Partnership Accounting remains accurate, compliant, and strategically aligned.
At Lanop Business and Tax Advisors, our approach is comprehensive. We deliver tailored partnership accounting services, structured partnership bookkeeping, and forward-looking partnership financial management designed to protect partner interests and maximize profitability. We understand that each partnership is unique. Our solutions reflect individual goals, industry requirements, and long term ambitions.
Conclusion
Partnerships are built on collaboration, shared responsibility, and collective vision. Yet without structured Partnership Accounting, even strong partnerships may struggle with financial uncertainty. Clear capital accounts, disciplined partnership bookkeeping, transparent profit allocation, and strategic partnership financial management create a stable foundation for growth. When accounting systems are simplified and professionally managed, partners gain clarity, strengthen trust, and unlock sustainable profit.
At Lanop Business and Tax Advisors, we are committed to helping partnerships move from confusion to confidence. Through expert partnership accounting services, we ensure that financial clarity becomes a catalyst for lasting success. Because in every thriving partnership, clarity is not optional. It is essential.
-
Business3 years ago
Cybersecurity Consulting Company SequelNet Provides Critical IT Support Services to Medical Billing Firm, Medical Optimum
-
Business3 years ago
Team Communication Software Transforms Operations at Finance Innovate
-
Business3 years ago
Project Management Tool Transforms Long Island Business
-
Business3 years ago
How Alleviate Poverty Utilized IPPBX’s All-in-One Solution to Transform Lives in New York City
-
health3 years ago
Breast Cancer: The Imperative Role of Mammograms in Screening and Early Detection
-
Sports3 years ago
Unstoppable Collaboration: D.C.’s Citi Open and Silicon Valley Classic Unite to Propel Women’s Tennis to New Heights
-
Art /Entertainment3 years ago
Embracing Renewal: Sizdabedar Celebrations Unite Iranians in New York’s Eisenhower Park
-
Finance3 years ago
The Benefits of Starting a Side Hustle for Financial Freedom
































