Technology
Harassment Fueled by Rite Aid’s Facial Recognition, Says FTC

How Rite Aid’s Facial Recognition Harms Customers and Communities
A report exposes how Rite Aid’s facial recognition system violates privacy rights, discriminates against people of color and women, and fuels harassment and violence.
Introduction: Meet the Author

Picture by: https://commons.wikimedia.org/
Hello, my name is Alex Smith, and I’m a freelance writer and blogger who specializes in technology, law, and social justice. I have been following the developments and controversies surrounding facial recognition for the past few years, and I have written several articles and reports on the topic. I have also interviewed experts, activists, and victims of facial recognition abuse, and I have witnessed firsthand how this technology can impact people’s lives.
In this article, I will share with you some of the shocking findings of a recent report that exposes how Rite Aid, a pharmacy chain that operates in the United States, has been using facial recognition systems in hundreds of its stores since 2017. I will explain how Rite Aid’s facial recognition system, called DeepCam, works, and what are the privacy, security, and ethical issues that it raises. I will also provide you with some practical tips and resources on how to protect yourself and your community from facial recognition surveillance and harassment.
What is Facial Recognition and How Does It Work?
Facial recognition is a technology that matches captured images with other facial images held in databases or on government watchlists. It uses artificial intelligence (AI) algorithms to analyze the shape, size, and features of a person’s face, such as the distance between the eyes, the width of the nose, or the shape of the chin. Facial recognition can be used for various purposes, such as unlocking smartphones, verifying identities, tagging photos, or finding missing persons.
However, facial recognition can also be used for more sinister purposes, such as tracking, profiling, spying, or targeting people based on their appearance, behavior, or location. Facial recognition can be deployed in various ways, such as through cameras, smartphones, drones, or wearable devices. Facial recognition can also be integrated with other technologies, such as biometrics, geolocation, or social media, to create a more comprehensive and invasive picture of a person’s identity, activities, and preferences.
One of the most advanced and controversial facial recognition systems in the world is DeepCam, developed by a company called Clarifai. DeepCam uses deep learning algorithms to analyze faces, which means that it can learn from large amounts of data and improve its accuracy and performance over time. DeepCam claims to be able to recognize faces in any lighting, angle, or expression, and to be able to distinguish between identical twins, masks, or makeup. DeepCam also claims to be able to detect emotions, age, gender, ethnicity, and even health conditions from a person’s face.
How Does Rite Aid Use DeepCam and Why?
Rite Aid is a pharmacy chain that operates in the United States, with over 2,000 stores across 19 states. Rite Aid has deployed DeepCam in hundreds of its stores since 2017, without informing or obtaining consent from its customers or employees. Rite Aid claims that it uses DeepCam for security purposes, such as preventing theft, protecting staff and customers from violence, and verifying identities.
According to Rite Aid, DeepCam works by scanning the faces of everyone who enters its stores and comparing them with a database of known or suspected criminals, such as shoplifters, robbers, or violent offenders. If DeepCam detects a match, it alerts the store manager, who can then decide whether to confront, ban, or report the person to the authorities. Rite Aid also claims that DeepCam can help identify customers who are eligible for discounts, rewards, or special offers, based on their loyalty or purchase history.
However, Rite Aid’s use of DeepCam has been criticized by many experts, activists, and customers, who argue that it violates privacy rights, discriminates against people of color and women, and fuels harassment and violence. In the next sections, I will explain some of the main issues and concerns that Rite Aid’s facial recognition system raises, and how it impacts the lives of customers and communities.

Picture by: https://dealmama.com/
What are the Privacy Concerns of Rite Aid’s Facial Recognition System?
One of the most serious concerns of Rite Aid’s facial recognition system is that it violates the privacy rights of customers and employees, who are not informed or given a choice about the collection and use of their biometric data. Biometric data refers to the unique physical characteristics of a person, such as their face, fingerprints, iris, or voice. Biometric data is considered to be sensitive and personal information, as it can reveal a person’s identity, health, emotions, or preferences.
Rite Aid’s facial recognition system collects biometric data of customers and employees without their consent, and stores it in a database that can be accessed by Rite Aid, Clarifai, or third parties, such as law enforcement agencies, advertisers, or hackers. Rite Aid does not disclose how long it keeps the biometric data, or how it protects it from unauthorized access or misuse. Rite Aid also does not provide any way for customers or employees to opt out, delete, or correct their biometric data, or to challenge any decisions or actions that are based on it.
This means that Rite Aid’s facial recognition system can be used to identify, track, profile, or target customers or employees without their knowledge or permission, and potentially expose them to various risks, such as identity theft, fraud, stalking, harassment, or discrimination. For example, Rite Aid’s facial recognition system could be used to:
- Monitor the shopping habits, preferences, or health conditions of customers or employees, and use this information to manipulate their behavior, influence their choices, or sell them products or services that they do not need or want.
- Share the biometric data of customers or employees with third parties, such as law enforcement agencies, advertisers, or hackers, who could use it for their own purposes, such as surveillance, profiling, or targeting.
- Misidentify customers or employees as criminals or suspects, and subject them to false accusations, arrests, or violence.

Picture by: https://www.ftc.gov/policy
What are the Technical Vulnerabilities of Rite Aid’s Facial Recognition System?
Another major concern of Rite Aid’s facial recognition system is that it is vulnerable to technical errors, glitches, or attacks, that could compromise its accuracy, reliability, or security. Rite Aid’s facial recognition system relies on complex and opaque algorithms that are not transparent, accountable, or auditable, and that can be affected by various factors, such as lighting, angle, expression, or quality of the images. Rite Aid’s facial recognition system also depends on the quality and integrity of the data that it uses, such as the database of criminals or suspects, or the loyalty or purchase history of customers.
This means that Rite Aid’s facial recognition system can be spoofed, manipulated, or hacked by malicious actors, who could use fake images, masks, or software to impersonate someone else, or to alter or delete the biometric data of customers or employees. This could lead to various consequences, such as:
- Identity theft, fraud, or impersonation: Someone could use a fake image, mask, or software to trick Rite Aid’s facial recognition system into thinking that they are someone else, and gain access to their personal information, accounts, or benefits.
- Stalking, harassment, or violence: Someone could use a fake image, mask, or software to evade Rite Aid’s facial recognition system, and enter the store without being detected, and harass, threaten, or harm customers or employees.
- False accusations, arrests, or lawsuits: Someone could use a fake image, mask, or software to frame someone else as a criminal or suspect, and cause them to be falsely accused, arrested, or sued by Rite Aid or the authorities.
What are the Bias Issues of Rite Aid’s Facial Recognition System?
The most disturbing concern of Rite Aid’s facial recognition system is that it is biased and discriminatory, especially against people of color, women, children, and the elderly. Rite Aid’s facial recognition system uses DeepCam, which is based on deep learning algorithms that learn from large amounts of data. However, this data can be skewed, incomplete, or inaccurate, and reflect the biases, prejudices, or stereotypes of the people who collect, label, or use it.
This means that Rite Aid’s facial recognition system can be racially biased and inaccurate, and misclassify people of color, women, children, and the elderly more often than white men. Studies have shown that some facial analysis algorithms misclassify Black women nearly 35 percent of the time while nearly always getting it right for white men. This means that people of color are more likely to be misidentified as criminals or suspects than white people when using face surveillance technology like DeepCam.
This also means that Rite Aid’s facial recognition system can be used to target and harass people of color, women, children, and the elderly, who are already marginalized and vulnerable in society. Rite Aid’s facial recognition system can be used to:
- Exclude, isolate, or intimidate people of color, women, children, and the elderly, who may feel unwelcome, unsafe, or uncomfortable in Rite Aid’s stores, and avoid shopping there or working there.
- Profile, monitor, or criminalize people of color, women, children, and the elderly, who may be subjected to more scrutiny, suspicion, or intervention by Rite Aid or the authorities

Picture by: https://www.newsbreak.com/
How to Protect Yourself and Your Community from Rite Aid’s Facial Recognition System?
As you can see, Rite Aid’s facial recognition system poses serious threats to the privacy, security, and dignity of customers and employees, especially people of color, women, children, and the elderly. However, there are some ways that you can protect yourself and your community from Rite Aid’s facial recognition surveillance and harassment. Here are some tips and resources that you can use:
- Avoid or boycott Rite Aid’s stores that use facial recognition. You can find out which stores use facial recognition by using this map created by the investigative journalists who exposed Rite Aid’s facial recognition program. You can also use this app to scan the barcode of any product and see if it is sold by Rite Aid or any other company that uses facial recognition. You can also support alternative pharmacies that respect your privacy and do not use facial recognition, such as CVS or Walgreens.
- Cover or disguise your face when entering Rite Aid’s stores that use facial recognition. You can use masks, sunglasses, hats, scarves, or makeup to hide or alter your facial features and prevent Rite Aid’s facial recognition system from recognizing you. You can also use special accessories, such as these glasses or this hat, that can reflect or block the infrared light that facial recognition cameras use to capture your face. You can also use this app to generate realistic-looking fake faces that you can use as your profile picture or avatar online.
- Educate yourself and others about the dangers and harms of facial recognition. You can read more about the issues and impacts of facial recognition on this website or this blog. You can also watch these videos or listen to these podcasts that explain how facial recognition works and why it is problematic. You can also share this article or any other relevant information with your friends, family, or social media followers, and raise awareness about Rite Aid’s facial recognition system and its consequences.
- Join or support the movements and campaigns that oppose facial recognition. You can sign this petition or this letter that demand Rite Aid to stop using facial recognition in its stores. You can also join or donate to these organizations or these coalitions that are fighting against facial recognition and advocating for privacy and civil rights. You can also contact your local, state, or federal representatives and urge them to pass laws or regulations that ban or limit the use of facial recognition by corporations or governments.
Conclusion: Take Action Now
Rite Aid’s facial recognition system is a clear example of how facial recognition technology can be used to violate privacy rights, discriminate against people of color and women, and fuel harassment and violence. Rite Aid’s facial recognition system is not only unethical, but also illegal, as it violates several state and federal laws that protect biometric data, consumer rights, and human dignity. Rite Aid’s facial recognition system is also unnecessary, as there are other, more effective and less invasive ways to ensure security and customer satisfaction.
Therefore, I urge you to take action now and protect yourself and your community from Rite Aid’s facial recognition system. You can avoid or boycott Rite Aid’s stores that use facial recognition, cover or disguise your face when entering them, educate yourself and others about the dangers and harms of facial recognition, and join or support the movements and campaigns that oppose facial recognition. By doing so, you can help stop Rite Aid’s facial recognition system and make a difference for yourself and your community.
Finance
New IPO Guide: Trends, Risks and Investment Insights India

The Indian primary market continues to be an attractive opportunity for many investors. Many businesses across multiple sectors are seeking to access public markets in order to gain exposure from new capital sources.
For many investors tracking new IPOs has become a key component of participating in capital markets because the overall market’s performance often serves as an indicator of economic confidence, investor sentiment, and anticipated future growth by industry sector.
Additionally, IPO investors today are comprised of more than just large institutions and institutional investors. Retail investors are now tracking subscription trends, listing dates, company fundamentals and industry outlook prior to applying for a public offering. Retail investors also use the information to compare businesses within the same industry as well as investigate long-term trends in equity markets for specific industries when making their own investment decisions regarding IPOs.
This guide discusses trends related to IPOs; key pieces of information that all investors need to watch for; and various factors that influence investor participation in new issues in India at this time.
What is a new IPO?
A new IPO, or Initial Public Offering, refers to a company offering its shares to the public for the first time before becoming listed on recognised stock exchanges.
Once listed, the company’s shares begin trading publicly within the secondary market.
Companies usually launch IPOs to raise funds for purposes such as:
- Business expansion
- Debt reduction
- Infrastructure development
- Operational growth
- Technology investment
- Working capital requirements
For investors, IPO participation provides an opportunity to invest in businesses before regular public market trading begins.

Why investors closely track IPO updates
IPO activity often reflects overall market confidence and business growth expectations.
Investors usually monitor IPO updates because:
- Public issues may indicate sector growth opportunities
- Strong IPO pipelines often reflect healthy market sentiment
- New listings create additional investment choices
- Institutional participation may influence investor confidence
- Listing performance sometimes affects broader market psychology
During active IPO periods, market discussions generally increase across financial platforms, brokerage firms, and investor communities.
Current trends in the indian IPO market
The Indian IPO market continues witnessing strong activity across multiple sectors and business categories.
Several important trends currently influence public market participation.
Increased Retail Participation
Retail investors continue participating actively in IPO subscriptions through online investment platforms and digital applications.
Growth in SME Listings
Small and medium enterprise IPO activity has increased significantly as smaller businesses increasingly access public markets for expansion capital.
Greater Focus on Profitability
Investors now pay closer attention to financial stability, profitability, and realistic business valuations instead of depending only on growth projections.
Technology and Startup Listings
Technology-driven businesses and startup companies continue preparing for public listings across India’s evolving digital economy.
Sector-Based Investor Interest
Sector trends often influence IPO demand, especially during periods of strong economic growth or rising industry-specific optimism.
Key IPO details investors should track
IPO investing involves much more than simply following listing discussions or subscription headlines.
Investors usually benefit from evaluating several important factors before participating in public issues.
Company Financial Performance
Reviewing revenue growth, profitability, debt levels, and cash flow stability may help investors understand business strength more realistically.
Business Model and Industry Position
Understanding how the company generates revenue and competes within its industry helps investors evaluate long-term sustainability.
IPO Valuation
Aggressive pricing may increase investment risk if the valuation appears significantly higher than industry peers or broader market expectations.
Promoter and Management Background
Management quality and promoter credibility often influence investor confidence regarding operational discipline and future business direction.
Purpose of IPO Proceeds
Companies generally explain how they plan to use IPO funds, including expansion projects, debt reduction, or operational investment plans.
Subscription Trends
Strong institutional participation sometimes improves market confidence during the IPO subscription period.
Importance of reading the prospectus
Many first-time investors focus mainly on listing expectations while ignoring the company prospectus.
However, the prospectus contains important operational and financial information including:
- Revenue details
- Business risks
- Industry outlook
- Debt obligations
- Litigation matters
- Promoter information
- Future growth plans
Reading these disclosures carefully may help investors understand whether the business aligns with their financial expectations and risk tolerance.
Role of market sentiment in IPO performance
IPO performance often depends partly on broader market conditions and investor confidence.
Positive market sentiment sometimes improves:
- Subscription demand
- Listing activity
- Institutional participation
- Retail investor confidence
On the other hand, weak market conditions may affect listing performance even when the company demonstrates stable business fundamentals.
This is why investors usually monitor overall market direction before participating actively in public issues.
Connection between sector trends and IPO demand
Sector performance frequently influences investor interest during IPO cycles.
For example, industries experiencing strong growth or favorable economic conditions often attract higher subscription demand.
Similarly, sectors linked with automobile passenger car stocks sometimes receive increased investor attention during periods of rising consumer demand, economic recovery, or manufacturing expansion.
Sector sentiment may influence:
- IPO subscription levels
- Valuation expectations
- Institutional participation
- Long-term investor confidence
Understanding industry cycles may therefore help investors evaluate IPO opportunities more carefully.
Risks associated with IPO investments
Although IPOs attract strong investor interest, they also involve financial and market-related risks.
- Listing Volatility:
Newly listed shares sometimes experience sharp price movement during early trading sessions because of changing investor demand and market sentiment. - Limited Public Trading History:
Unlike established listed companies, IPO-bound businesses may have limited public market history available for long-term performance evaluation. - Valuation Risk:
Certain IPOs may enter markets at aggressive valuations during periods of heightened investor enthusiasm or sector popularity. - Market Condition Risk:
Weak broader market conditions may affect listing performance even if company fundamentals remain stable. - Emotional Investment Decisions:
Fear of missing out often influences first-time investors during highly discussed IPO launches and subscription periods.
Common mistakes investors should avoid
Many investors make avoidable mistakes during active IPO periods.
Applying Without Proper Research
Depending entirely on subscription discussions without reviewing business fundamentals may create unrealistic expectations regarding future performance.
Ignoring Valuation Concerns
Depending Entirely on Grey Market Discussions
Unofficial market speculation does not guarantee actual listing performance or future business stability.
Overlooking Business Risks
Every company faces operational, financial, industry-specific, and competitive risks that investors should understand carefully before applying.
Focusing Only on Short-Term Listing Movement
Many investors concentrate entirely on listing expectations instead of evaluating long-term business quality and operational performance.
Technology has simplified IPO participation
Technology has transformed IPO participation significantly for Indian retail investors.
Today, investors can:
- Apply through mobile applications
- Access IPO calendars online
- Track allotment status digitally
- Read prospectus documents instantly
- Monitor subscription updates in real time
Online investment platforms have simplified access to India’s primary market ecosystem for retail participants.
Importance of long-term perspective in IPO investing
Some investors participate in IPOs mainly for short-term listing activity, while others evaluate businesses from a longer-term perspective.
Strong companies generally sustain growth through:
- Financial discipline
- Operational expansion
- Industry competitiveness
- Business adaptability
- Consistent profitability
This is why evaluating business quality usually matters more than reacting emotionally to short-term market excitement.
How IPO activity reflects economic trends
IPO activity often increases during periods of economic growth, rising market liquidity, and stronger investor participation.
Businesses generally prefer entering public markets when:
- Investor sentiment remains positive
- Capital markets remain active
- Industry conditions appear favorable
- Economic growth expectations improve
Because of this, IPO trends sometimes provide insight into broader economic confidence and business expansion activity within the country.
Conclusion
The Indian IPO market continues attracting strong investor participation as companies across different sectors prepare to enter public markets. Increasing digital accessibility, growing retail participation, and expanding sector opportunities continue supporting IPO activity across India.
However, investors should evaluate financial performance, valuation, business fundamentals, and sector conditions carefully before participating in any new IPO. Whether analyzing technology companies or sectors connected with automobile passenger car stocks, disciplined research and informed decision-making usually remain important for navigating the primary market responsibly.
Management
Secure Software Lifecycle: Shift-Left & Cyber Defense
n today’s digital world, even a minor software vulnerability can expose an entire organization to serious cyber threats. A single insecure line of code can put millions of users and critical data at risk. Because of this growing threat landscape, cybersecurity is no longer just about protecting networks and systems from the outside; it has become a fundamental part of how software itself is built.
The old practice of developing software first and adding Security later is no longer effective. In fact, it often creates more risks than solutions. With major cyber incidents such as the SolarWinds supply chain attack and vulnerabilities like Log4j, organizations have realized that Security must be embedded throughout the entire development process. This is where Secure Software Lifecycle Management (SSLM) plays a crucial role in modern cyber defense.
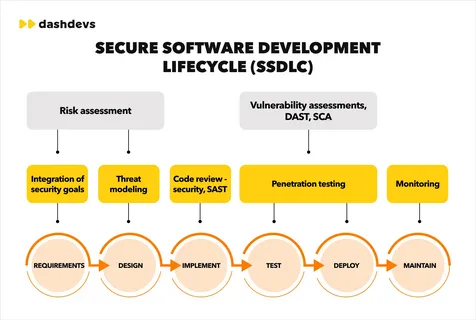
The Shift-Left Approach
Traditionally, security checks were performed only after software development was complete. This resulted in vulnerabilities being identified late in the process, leading to costly and challenging repairs.
Today, organizations are adopting the Shift-Left security approach, integrating security practices into the earliest stages of the Software Development Life Cycle (SDLC). By incorporating security considerations into the planning, design, and coding phases, teams can identify potential weaknesses before they become real problems.
This proactive approach not only reduces costs but also ensures that Security becomes a core part of the software rather than an added feature.
Connecting Development Teams
One of the biggest challenges in modern IT environments is the communication gap between developers and security teams. Developers often prioritize performance, functionality, and speed, while security professionals focus on minimizing risks and vulnerabilities.
Secure Software Lifecycle Management helps bridge this gap by creating a structured framework that enables both teams to collaborate effectively. Certifications such as the Certified Secure Software Lifecycle Professional (CSSLP) equip professionals with the knowledge and methodology to manage Security throughout the software lifecycle—from planning and development to deployment and eventual retirement. Rather than focusing solely on writing secure code, the approach emphasizes managing the entire ecosystem that produces and maintains software.
Securing the Software Supply Chain
Most modern applications are not built entirely from scratch. Developers rely heavily on open-source libraries, third-party frameworks, and external APIs. While these resources accelerate development, they can also introduce hidden security risks.
Secure Software Lifecycle Management ensures that every component used in software development is carefully reviewed, tracked, and monitored for vulnerabilities. Without proper oversight, a single compromised dependency can weaken the Security of the entire application. By implementing structured processes, organizations can maintain greater visibility and control over their software supply chain.
Developing the Next Generation of Security Professionals
As organizations place greater emphasis on secure software development, the demand for skilled cybersecurity professionals continues to grow. Certifications like CSSLP are becoming increasingly valuable for professionals who want to demonstrate expertise in secure software lifecycle practices.
However, mastering the multiple domains covered in the certification requires both theoretical knowledge and practical preparation. Many candidates enhance their preparation through simulation tools that replicate the structure and pressure of the real exam environment. Practice platforms, whether desktop or web-based, allow candidates to test their understanding, identify knowledge gaps, and build confidence before taking the actual certification exam.
Building Skills
As organizations place greater emphasis on secure development practices, the demand for professionals with specialized knowledge continues to grow. Preparing for certifications like CSSLP requires both conceptual understanding and practical exam readiness.
Many candidates improve their preparation by practicing with tools designed to simulate real exam scenarios. For example, using CSSLP Desktop Practice Software allows learners to practice offline in an environment that closely resembles the actual certification exam. This helps them understand the exam structure, manage time effectively, and strengthen their confidence.
At the same time, professionals who prefer flexibility often rely on a CSSLP Web-Based Practice Test, which enables them to practice from any device and continue learning wherever they are. Combining these preparation methods often helps candidates develop a stronger understanding of secure software lifecycle principles.
Security, Compliance, and Business Trust
Secure Software Lifecycle Management is not only important for protecting applications but also for meeting regulatory requirements. Laws and regulations around data protection continue to evolve, and organizations are expected to demonstrate responsible security practices.
Companies that implement secure development processes show customers and partners that they take cybersecurity seriously. In the digital economy, trust plays a major role in long-term business success, and strong security practices help organizations maintain that trust.
Final Thoughts
Cyber defense today starts long before software is deployed. It begins during design discussions, development planning, and coding itself. Organizations that integrate security throughout the entire software lifecycle are better equipped to prevent vulnerabilities and protect their systems from evolving threats.
For developers, security engineers, and project managers, understanding secure software lifecycle management is becoming an essential skill. By prioritizing security from the beginning and continuously improving development practices, organizations can build software that is both innovative and resilient.
Development
Partnership Accounting: Trust, Track Equity, and Maximize Profit

When James and Aamir founded their consultancy firm, they shared more than ambition. They shared trust. One brought financial expertise, the other brought industry connections. In the early days, decisions were made over coffee, expenses were tracked in spreadsheets, and profits were divided with a handshake. The business grew quickly. Clients multiplied. Revenue increased. Yet as the numbers became larger, so did the questions. The partnership had momentum, but it lacked structured Partnership Accounting.
- Why did the capital accounts look uneven?
- How were partner drawings affecting overall cash flow?
- Were profits being distributed fairly?
- What were their individual tax liabilities?
What once felt simple became increasingly complex. The absence of clarity began to create hesitation in decision-making. Their story reflects the experience of many partnerships. Growth introduces financial intricacy. Without a solid accounting structure, uncertainty can quietly undermine even the strongest business relationships.
At Lanop Business and Tax Advisors, we believe that effective Partnership Accounting transforms uncertainty into clarity and shared ambition into measurable profit. It is not merely compliance. It is the economic structure that safeguards collaborations, enhances trust, and promotes sustainable development.
The Foundation of Partnership Accounting
Partnership Accounting refers to the structured process of recording, managing, and reporting the financial activities of a business owned by two or more partners. Unlike sole traders or limited companies, partnerships require special attention to equity distribution, profit sharing, capital accounts, and tax obligations.
Each partner may contribute different levels of capital, expertise, and time. Profit-sharing arrangements may vary. Withdrawals may occur throughout the year. Without a defined accounting system, tracking these elements becomes difficult.
The foundation of strong Partnership Accounting includes:
- Accurate recording of capital contributions
- Clear documentation of profit and loss allocation
- Consistent tracking of partner drawings
- Preparation of reliable financial statements
- Compliance with tax regulations
When these elements operate together, the partnership gains financial visibility and operational confidence.
Building Trust Through Transparency
This is the power of structured Partnership Accounting. Transparent reporting reduces disputes. It aligns expectations. It creates a shared understanding of performance. Professional partnership accounting services ensure that transparency becomes standard practice rather than an afterthought. When partners see the same numbers and understand how they are derived, collaboration strengthens.
Capital Accounts and Partner Equity
One of the distinguishing features of Partnership Accounting is the management of individual capital accounts. Each partner maintains a capital account reflecting their financial stake in the business.
Capital accounts typically include:
- Initial investment
- Additional contributions
- Allocated profits
- Allocated losses
- Withdrawals
Without careful management, discrepancies can arise. For example, if one partner withdraws more frequently than another, equity balances shift. Inaccurate profit allocation may cause misunderstandings to develop.
Professional partnership bookkeeping records these movements precisely and updates them regularly. This clarity becomes essential during expansion, restructuring, or partner transitions. Capital account accuracy protects both the partnership and the individual partners.
Profit Sharing and Fair Allocation
Profit sharing lies at the heart of partnership relationships. Whether profits are distributed equally or based on agreed ratios, accurate allocation is critical.
Structured Partnership Accounting follows the terms set out in the partnership agreement. This may involve:
- Fixed percentage splits
- Interest on capital contributions
- Salary allowances for active partners
- Performance-related distributions
Errors in profit allocation can have tax consequences and strain relationships. Reliable partnership bookkeeping ensures income and expenses are categorized correctly throughout the financial year, making profit calculation accurate and defensible. When allocation processes are clear and consistent, partners focus on growth rather than disputes.
Role of Partnership Bookkeeping
Behind every strong accounting system lies disciplined daily recording. Partnership bookkeeping forms the operational core of effective financial management. Every invoice issued, every supplier payment, every expense claim, and every partner withdrawal must be recorded accurately. Delayed entries or inconsistent categorization create confusion at year’s end.
Professional partnership bookkeeping provides:
- Real-time tracking of income and expenses
- Accurate reconciliation of bank accounts
- Clear classification of partner drawings
- Reliable data for reporting and analysis
- Reduced risk of costly errors
Consistency in bookkeeping ensures that financial statements reflect reality rather than estimates. At Lanop Business and Tax Advisors, we integrate meticulous partnership bookkeeping within our broader partnership accounting services to provide complete financial oversight.
Tax Responsibilities and Compliance
Partnership taxation requires precision. In many jurisdictions, partnerships operate under pass-through taxation. Profits are allocated to partners who report them individually.
Accurate Partnership Accounting ensures:
- Correct preparation of partnership returns
- Accurate reporting of individual profit shares
- Compliance with regulatory requirements
- Identification of legitimate deductions
- Reduced exposure to penalties
Professional partnership accounting services provide structured support to navigate complex tax rules while maintaining full compliance. Clear documentation protects the partnership during audits and ensures each partner meets their obligations confidently.
Managing Growth and Structural Changes
As partnerships evolve, accounting complexity increases. Growth may require additional capital contributions, financing arrangements, or admission of new partners. Each structural change requires adjustments in capital accounts and profit-sharing ratios. Without organized Partnership Accounting, transitions can become contentious.
Strong partnership financial management ensures smooth integration of new partners, accurate valuation of business interests, and fair settlement of exiting partners. Financial clarity simplifies change management and protects long-term stability.
Why Professional Expertise Matters
While some partnerships attempt internal management, complexity often increases with growth. Regulatory requirements evolve. Tax laws change. Financial risks expand. Engaging experienced advisors ensures that Partnership Accounting remains accurate, compliant, and strategically aligned.
At Lanop Business and Tax Advisors, our approach is comprehensive. We deliver tailored partnership accounting services, structured partnership bookkeeping, and forward-looking partnership financial management designed to protect partner interests and maximize profitability. We understand that each partnership is unique. Our solutions reflect individual goals, industry requirements, and long term ambitions.
Conclusion
Partnerships are built on collaboration, shared responsibility, and collective vision. Yet without structured Partnership Accounting, even strong partnerships may struggle with financial uncertainty. Clear capital accounts, disciplined partnership bookkeeping, transparent profit allocation, and strategic partnership financial management create a stable foundation for growth. When accounting systems are simplified and professionally managed, partners gain clarity, strengthen trust, and unlock sustainable profit.
At Lanop Business and Tax Advisors, we are committed to helping partnerships move from confusion to confidence. Through expert partnership accounting services, we ensure that financial clarity becomes a catalyst for lasting success. Because in every thriving partnership, clarity is not optional. It is essential.
-
Business3 years ago
Cybersecurity Consulting Company SequelNet Provides Critical IT Support Services to Medical Billing Firm, Medical Optimum
-
Business3 years ago
Team Communication Software Transforms Operations at Finance Innovate
-
Business3 years ago
Project Management Tool Transforms Long Island Business
-
Business3 years ago
How Alleviate Poverty Utilized IPPBX’s All-in-One Solution to Transform Lives in New York City
-
health3 years ago
Breast Cancer: The Imperative Role of Mammograms in Screening and Early Detection
-
Sports3 years ago
Unstoppable Collaboration: D.C.’s Citi Open and Silicon Valley Classic Unite to Propel Women’s Tennis to New Heights
-
Art /Entertainment3 years ago
Embracing Renewal: Sizdabedar Celebrations Unite Iranians in New York’s Eisenhower Park
-
Finance3 years ago
The Benefits of Starting a Side Hustle for Financial Freedom
































