Technology
The Truth is Out There: How to Navigate the Internet’s Misinformation Maze

The Truth is Out There: How to Navigate the Internet’s Misinformation Maze
The internet is a vast and wonderful source of information, entertainment, and communication. But it is also a place where misinformation, deception, and manipulation can thrive. How can you tell the difference between reliable and unreliable information online? How can you avoid falling prey to false or misleading claims, rumors, or propaganda? How can you protect yourself and others from the harmful effects of misinformation?
In this article, I will share some tips and strategies on how to evaluate online sources and navigate the internet’s misinformation maze. I will also provide some examples of common types of misinformation and how to spot them. By the end of this article, you will have a better understanding of how to use the internet wisely and responsibly, and how to find the truth that is out there.
What is misinformation and why does it matter?
Misinformation is generally defined as information that is false, inaccurate, or misleading, but not necessarily created or shared with the intention to cause harm. Sometimes, misinformation is the result of honest mistakes, poor research, or outdated information. Other times, misinformation is deliberately created or spread by people or groups who have ulterior motives, such as political agendas, financial gains, or personal grudges.
Misinformation can have serious consequences for individuals and society. It can erode trust in institutions, authorities, and experts. It can influence people’s opinions, beliefs, and behaviors. It can affect people’s health, safety, and well-being. It can also fuel conflicts, divisions, and violence.
For example, misinformation about the COVID-19 pandemic has led to confusion, fear, and complacency among the public, undermining the efforts to contain the virus and save lives. Misinformation about the 2020 U.S. presidential election has contributed to political polarization, social unrest, and violence, threatening the stability and legitimacy of democracy. Misinformation about climate change has delayed the action and cooperation needed to address the global environmental crisis.
Therefore, it is important to be aware of the prevalence and impact of misinformation online, and to develop the skills and habits to identify and counter it.
How to evaluate online sources
One of the key skills to combat misinformation online is to evaluate the sources of information you encounter. A source is anything that provides information, such as a website, a book, a video, a podcast, or a person. Not all sources are equally reliable, credible, or trustworthy. Some sources may have more authority, accuracy, objectivity, currency, coverage, and appearance than others.
To evaluate online sources, you can use the following criteria and questions:
- Authority: Who is the author or creator of the information? What are their credentials, qualifications, or expertise on the topic? Are they affiliated with a reputable institution or organization? How can you contact them or verify their identity?
- Accuracy: Is the information factual, correct, and supported by evidence? Are the sources of the information cited or linked? Can you confirm the information from other sources? Are there any errors, inconsistencies, or contradictions in the information?
- Objectivity: What is the purpose or goal of the information? Is the information presented fairly, impartially, and without bias? Is the information based on facts, opinions, or emotions? Are there any hidden agendas, conflicts of interest, or ulterior motives behind the information?
- Currency: When was the information created, updated, or revised? Is the information current, relevant, and timely for your needs? Does the information reflect the latest developments, research, or data on the topic?
- Coverage: How much and how well does the information cover the topic? Is the information comprehensive, detailed, and in-depth, or superficial, vague, and incomplete? Is the information consistent, coherent, and logical, or contradictory, confusing, and flawed?
- Appearance: How does the information look and sound? Is the information well-written, well-organized, and well-designed, or poorly-written, poorly-organized, and poorly-designed? Is the information clear, concise, and readable, or unclear, wordy, and unreadable? Is the information professional, polished, and appealing, or amateur, sloppy, and unappealing?
You can use these criteria and questions as a checklist to evaluate any online source you encounter. The more questions you can answer positively, the more likely the source is reliable and credible. However, keep in mind that these criteria and questions are not absolute or definitive. Sometimes, a source may meet some criteria but not others, or may have some strengths and some weaknesses. Therefore, you should always use your own judgment and critical thinking to assess the quality and value of a source.
How to spot common types of misinformation
Another skill to combat misinformation online is to spot the common types of misinformation that circulate on the internet. Some of the most prevalent and problematic types of misinformation are:
- Fake news: Fake news is information that is deliberately fabricated or distorted to mislead the public, usually for political or financial purposes. Fake news often mimics the style and format of legitimate news outlets, but lacks the standards and ethics of journalism. Fake news can be found on websites, social media platforms, or apps that are designed to look like credible sources, but are actually run by malicious actors or groups. Fake news can also be spread by bots, trolls, or influencers who have large online followings or networks.
- Satire and parody: Satire and parody are forms of humor that use exaggeration, irony, or ridicule to mock or criticize a person, group, or issue. Satire and parody can be found on websites, social media platforms, or apps that are dedicated to producing humorous content, such as The Onion, The Babylon Bee, or The Borowitz Report. Satire and parody can also be found on TV shows, podcasts, or videos that feature comedians, actors, or celebrities who impersonate or imitate real people or events, such as Saturday Night Live, The Daily Show, or The Late Show. Satire and parody are not meant to be taken seriously or literally, but sometimes they can be mistaken for or misused as real news or information.
- Hoaxes and scams: Hoaxes and scams are information that is intentionally false or deceptive to trick or harm the public, usually for personal gain or amusement. Hoaxes and scams can be found on websites, social media platforms, or apps that are created or used by individuals or groups who want to exploit the public’s curiosity, fear, or greed. Hoaxes and scams can also be spread by email, text, or phone calls that are sent or made by individuals or groups who want to obtain the public’s personal or financial information. Hoaxes and scams often involve sensational or sensationalized stories, claims, or offers that are too good or too bad to be true.
- Rumors and gossip: Rumors and gossip are information that is unverified, unsubstantiated, or speculative, usually about a person, group, or issue. Rumors and gossip can be found on websites, social media platforms, or apps that are focused on entertainment, celebrity, or lifestyle topics, such as TMZ, Perez Hilton, or BuzzFeed. Rumors and gossip can also be spread by word-of-mouth, online or offline, by individuals or groups who want to share or comment on the latest news or trends. Rumors and gossip may or may not be true, but they are often based on hearsay, speculation, or opinion, rather than facts, evidence, or verification.
To spot these common types of misinformation, you can use the following tips and strategies:
- Check the source: Look at the website, social media platform, or app where the information is published or shared. What is the name, domain, or URL of the source? Who is the author, creator, or owner of the source? What is the reputation, credibility, or agenda of the source? Is the source known for producing or spreading misinformation, or for being satirical, humorous, or sensational?
- Check the content: Look at the information itself. What is the headline, title, or caption of the information? What is the tone, style, or format of the information? What is the message, claim, or argument of the information? Is the information factual, logical, and consistent, or false, illogical, and contradictory? Is the information supported by evidence, sources, or links, or by emotions, opinions, or anecdotes?
- Check the context: Look at the background and surrounding of the information. When and where was the information created, published, or shared? Why and how was the information created, published, or shared? Who is the intended or actual audience of the information? What is the purpose or goal of the information? Is the information relevant, appropriate, and timely, or irrelevant, inappropriate, and outdated?
- Check the verification: Look at the confirmation or refutation of the information. What do other sources say about the information? What do experts, authorities, or fact-checkers say about the information? What do your own knowledge, experience, or common sense say about the information? Is the information verified, corroborated, or agreed upon, or disputed, debunked, or challenged?
You can use these tips and strategies as a guide to spot the common types of misinformation online. However, keep in mind that these tips and strategies are not foolproof or exhaustive. Sometimes, misinformation can be subtle, sophisticated, or convincing, or can mix some truth with some falsehood. Therefore, you should always be alert, curious, and skeptical when encountering information online.
Image by rawpixel.com on Freepik
Conclusion
The internet is a powerful and valuable tool for learning, communicating, and creating. But it is also a place where misinformation can flourish and harm. Therefore, it is important to be aware of the prevalence and impact of misinformation online, and to develop the skills and habits to identify and counter it.
In this article, I have shared some tips and strategies on how to evaluate online sources and spot common types of misinformation. I hope you have found this article helpful and informative. Here is a summary table of the main points discussed:
| Criteria for evaluating online sources | Tips for spotting common types of misinformation |
|---|---|
| Authority: Who is the author or creator of the information? | Check the source: What is the name, domain, or URL of the source? |
| Accuracy: Is the information factual, correct, and supported by evidence? | Check the content: What is the headline, title, or caption of the information? |
| Objectivity: What is the purpose or goal of the information? | Check the context: When and where was the information created, published, or shared? |
| Currency: When was the information created, updated, or revised? | Check the verification: What do other sources say about the information? |
| Coverage: How much and how well does the information cover the topic? | |
| Appearance: How does the information look and sound? |
Remember, the truth is out there, but you have to look for it carefully and critically. Don’t believe everything you see or hear online. Do your own research, check your facts, and verify your sources. Be a smart and responsible internet user, and help others do the same. Together, we can make the internet a better and safer place for everyone.
Thank you for reading this article. I hope you enjoyed it and learned something new. If you have any questions, comments, or feedback, please feel free to share them with me. I would love to hear from you. Have a great day!
Costumer Services
Fly Airlines Policy: Flight Change, Cancellation & Refund Guide
Traveling by air is now a big part of our lives. But sometimes, things can happen that mess up your plans, even when you get ready well. It is important to know an airline’s rules about changes, so you will not face trouble or lose your money. The Fly Airlines Policy gives clear steps for everything you need to know about changing flights, canceling, and getting money back. If you read this policy, you can handle your booking in a good way and feel safe with the airline’s help and service.
Flight Change Policy
A key part of the Fly Airlines Policy is how you can change your flight. With Fly Airlines, you have the choice to change your booking online, on the mobile app, or by talking to customer support. You need to follow the airline’s set times for making any changes. If you change your flight late, you may have to pay extra fees or face limits.
Passengers may have to pay a fee to change their ticket. This charge may vary depending on the ticket type, the route, and the pricing regulations. Along with this fee, they will need to pay if the new ticket costs more. For example, if someone wants to go from an economy ticket to a business class one, they should pay the extra amount before the change is approved.
Some fares are more flexible than others. Fully refundable or premium tickets may let you change your plans more than once without paying big fees. But standard economy tickets usually have more rules and limits. The Fly Airlines Policy is clear about these rules so you know what to expect when you book. This helps people choose the right option based on what they want and how much flexibility they need.
For people who travel to other countries, the airline gives more ways to change your plans. The Fly Airlines Policy lets you make changes if you have a visa delay, travel limits, or unexpected problems. You should get in touch with customer support right away to talk about your options.
Cancellation Policy
Cancellations can happen for different reasons, like work or things outside of us. The Fly Airlines Policy gives clear steps on what to do when you need to stop your flight. You can stop your tickets by using the official website, the app on your phone, or by calling the help number. The amount you pay to stop your flight changes. It depends on what kind of ticket you have, when you stop, and where you are going.
Fully refundable tickets give you the most ease, because you can cancel right up to the day you leave. You may pay little or nothing to cancel. Non-refundable tickets usually cost less, but you might have to pay a fee if you want to cancel. Fly Airlines often gives back part of your money as a travel credit or voucher. You can use this for another trip in the future. This means you still get some value from your first booking, even if they do not give you a cash refund.
The Fly Airlines Policy also talks about what to do when there are big problems. When there is bad weather, things like earthquakes, or rules from the government, Fly Airlines gives people choices. You can get fees removed, rebook your flight, or take travel credits. By doing this, the airline shows it cares about keeping people safe and making their trips as easy as possible. This also helps cut down stress when travel plans change at the last minute.
Refund Policy
The refund process is a key part of the Fly Airlines Policy. Passengers have the right to get money back based on the type of ticket and why they canceled. The refund usually goes back to the way you paid for the ticket. This helps to keep things clear and simple. If you have a refundable ticket, you will get a full refund, but some fees may be taken out.
For tickets that cannot be refunded, Fly Airlines gives you travel credits or vouchers. These can be used for a specific duration, ensuring you won’t forfeit the money you invested in your ticket. The airline makes sure you can use these credits by going to the online portal or through the mobile app.
The Fly Airlines Policy helps people who fly when the airline cancels a flight. If Fly Airlines stops a flight, the people on it will get all their money back or get help to travel a different way without having to pay more. If the airline changes the flight schedule, travelers can choose the updated time or request a refund.
Conclusion
Understanding the Fly Airlines policy before you book can save you both money and stress. Life is unpredictable. Flights get delayed, meetings shift, or personal emergencies arise. When you know the rules for changes, cancellations, and refunds, you stay in control. You avoid surprise fees and understand exactly what to expect.
Always check your ticket type before confirming your purchase. Fully refundable tickets offer peace of mind, while non-refundable options may still provide travel credits. If your plans change unexpectedly, contact customer support immediately. Early action often reduces penalties.
Remember, Fly Airlines prioritizes passenger safety and flexibility, especially during weather events or government restrictions. By staying informed, you turn a potentially stressful situation into a manageable one. Read the policy carefully, ask questions if unsure, and travel with confidence. A little preparation today ensures smoother journeys tomorrow.
health
P-Shot in Riyadh: Men’s Experiences, Results & Recovery Timeline

With the fast pace of life in the Saudi capital and a growing awareness of the importance of regenerative health, men in Riyadh are seeking advanced solutions to restore their vitality and energy beyond traditional methods. The P-Shot technique in Riyadh has emerged as one of the most positively received procedures in the medical community. This technique utilizes platelet-rich plasma (PRP) to stimulate tissue growth and improve blood circulation in a completely natural way. However, the most frequently asked question in health forums and gatherings remains: What does the patient actually feel after the first session? And how do men in Riyadh describe their experience with this revolutionary procedure?
First impressions
When surveying patients who underwent the P-Shot procedure at advanced Riyadh centers, the prevailing sentiment was “psychological comfort.” Many men felt apprehensive about pain or surgical complications, but the procedure surprised them because it is simple and effective local anesthesia numbs the area completely.
One reviewer said: “I expected to need a long recovery period, but I left the clinic and returned to my office work on the same day. The feeling of security because the substance was extracted from my blood made the experience very comfortable from the first moment . “
Immediate results vs. cumulative results
Scientifically, doctors know that P-Shot technology works by building new tissue, which takes time. However, men in Riyadh report interesting observations in their experiences after the first week following their initial session:
-
Improved blood flow: Many notice a significant improvement in overall blood circulation in the treated area, giving a much-needed sense of vitality.
-
Increased sensitivity and responsiveness: Thanks to growth factors that begin to repair nerve endings, some describe a restoration of “normal feeling” that had been diminished as a result of stress or chronic illness.
-
Psychological confidence: Simply starting a regenerative treatment course boosts morale, and this is a big part of the success of the process.
Why do men in sports prefer P-Shot technology?
In 2026, Riyadh became a regional center of medical excellence, and reviewers preferred the P-Shot technology in Riyadh for several key reasons they mentioned in their reviews:
-
No side effects: Compared to chemical drugs that may cause headaches or blood pressure disturbances, P-Shot is “self-administered” and completely safe.
-
Confidentiality and privacy: Clinics in Riyadh provide private pathways for patients, making the experience confidential and highly professional.
-
Sustainability: Reviewers see it not as just a temporary solution for hours, but as a building process whose results continue to improve for months.
Success stories
A businessman in Riyadh recounts his experience, saying: “After I turned forty, and due to work pressures and diabetes, I began to feel a decline in my physical activity. The doctor advised me to try the P-Shot as a rejuvenating option. A few weeks after the first session, I noticed a difference I hadn’t expected; it was no longer just about strength, but about the overall quality of life and the sense of confidence that was reflected in my family relationships . “
Such stories reflect how this technology has transformed from a mere “medical procedure” into a means of improving the overall lifestyle of the capital’s men.
Based on medical reports and patient experiences, here is the typical timeline for results after a P-Shot procedure in Riyadh :
-
Weeks 1-2: Any minor swelling (if present) disappears and blood flow begins to improve.
-
Weeks 4-6: Peak activity of growth factors; here the building of new blood vessels (angiogenesis) begins, and the patient notices a tangible improvement in function.
-
After 3 months: Results stabilize and reach the maximum state of tissue regeneration.
Advice from Riyadh men
-
Drinking plenty of water improves plasma quality and speeds up the regeneration process.
-
Avoid smoking: Reviewers who smoked noted that their results were slower compared to non-smokers, because nicotine inhibits the growth of new blood vessels.
-
Choosing a reliable center: Quality depends on the equipment used in plasma separation; therefore, choosing a state-of-the-art center is half the battle.
Privacy
It’s impossible to discuss the experiences of men in Riyadh without addressing the issue of privacy. Many people praise the meticulous appointment system and the respectful treatment, which ensures that clinics disclose no medical information. This encourages both prominent figures and young people to undergo the procedure without hesitation.
In conclusion
Based on the opinions of hundreds of men in Riyadh in 2026. The P-Shot technology represents a quantum leap in men’s medicine. Results after the first session may vary from person to person depending on their health condition. But the general consensus points to widespread satisfaction and continuous improvement that redefines the concept of vitality in middle age and beyond.
If you are looking to restore your energy and self-confidence through the latest scientific advancements. In a professional and safe environment. We welcome you to the best cosmetic clinic in Riyadh , where we combine superior medical expertise with the latest technologies to ensure that you receive a professional P-Shot procedure in Riyadh that restores your youth and guarantees tangible results with complete privacy that suits you.
Growth
Plant-based Meat Market: $18.7B to $54.8B

Roots Analysis has just published a new study on the global plant-based meat market. The report focuses on historical trends, current developments, and future growth projections. It provides a data-rich foundation for decision-makers, industry participants, and investors. The study includes both broad and detailed insights. As a result, readers can easily understand key dynamics across different segments, regions, and product categories.
Market Size and Future Expectations
The plant-based meat market is currently valued at $18.7 billion. Looking ahead, it is expected to reach $54.8 billion in the coming years. This represents a compound annual growth rate of 11.35%. These numbers come from observed trends and actual industry performance. The study also considers current developments in product usage and adoption.
The research team took into account the challenges faced by key players. They also examined the general market structure. However, they avoided speculative interpretations throughout the analysis. Their goal was simple: to provide a clear picture of market performance across different regions and segments.
This report supports strategic planning in several ways. It delivers verified data, cross-segment comparisons, and actionable insights. You can receive the findings in both PDF and spreadsheet formats. This makes integration into your existing workflows much easier.
Market Scope and Key Segments
The report covers a wide range of attributes. These include historical trends, forecast periods, and market sizes for both 2025 and 2035. It also includes the CAGR until 2035. Other important elements are the source of protein, the type of meat substituted, and the type of end product.
The study also examines the mode of storage and the type of distribution channel. It provides geographical regions, leading players, and key companies profiled. Complimentary materials include a PowerPoint presentation and Excel data packs. Customization options are available as well.
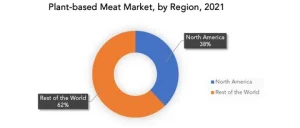
Regional Breakdown
The regional segmentation covers several major areas. North America includes the US, Canada, and the rest of North America. Europe includes the UK, Netherlands, Germany, Italy, Spain, France, and the rest of Europe.
Asia-Pacific covers China, India, Australia, New Zealand, and the rest of the region. The Middle East and North Africa includes Saudi Arabia, UAE, and the rest of MENA. Latin America covers Argentina, Brazil, Colombia, and the rest of Latin America.
This clear framework helps readers understand segment-specific trends. It also helps them identify growth opportunities across different markets.
Technological and Strategic Insights
The Roots Analysis report goes beyond basic numbers. It encompasses an in-depth evaluation of multiple essential aspects.
- First, it looks at technological advancements and research and development activity.
- Second, it explores innovations in formulation and delivery methods.
- Third, the study examines marketing and distribution strategies. Fourth, it analyzes pricing models and cost structures. Finally, it reviews manufacturing capacities and supply chain trends.
All these insights are presented neutrally. The team supports each finding with empirical evidence and primary research validation. Therefore, you can trust the data to make informed decisions.
Major Companies in the Plant-Based Meat Space
The report profiles many prominent companies. These include ADF Foods, Amy’s Kitchen, and Beyond Meat. Century Pacific Food, Conagra, and Continental Coffee are also covered. Other featured firms include Ecotone, Everbest Soya Bean Products, Green Monday, and Hilcona.
The list also includes Impossible Foods, ITC, JBS, Kellogg, and Kikka Sushi. Linda McCartney, ME-AT (Vion Food), Maple Leaf Foods, and Nestle appear as well. Nongshim Taekyung, OMG Meats, Quorn Foods, and Rügenwälder Mühle complete the list. Finally, the report profiles Symingtons, Tata Consumer Products, Tesco, Tyson Foods, and yumeat.
Each company profile highlights four key areas. First, it describes the product portfolio and focus areas. Second, it outlines the operational footprint and regional presence. Third, it reviews financial and strategic performance. Fourth, it covers recent developments such as partnerships, market entries, and acquisitions.
Regional Market Analysis
The study analyzes each region based on several factors. These include historical and current market size. The report also examines revenue performance and contribution to the global share. Finally, it looks at strategic developments and regional trends.
North America currently leads the market. Europe follows closely behind. Asia-Pacific is showing rapid growth due to changing consumer preferences and increasing investments. Insights from different regions facilitate precise strategies for market entry and growth. You can identify where the biggest opportunities exist and where the competition is fiercest.
How the Report Is Structured
The report follows a clear and logical structure.
- provides the market overview.
- details the market size categorized by regions.
- breaks down market revenue by individual countries.
- analyzes market competition among key players.
- concludes with detailed company profiles.
This structure makes it easy to find the information you need. You can start with the big picture and then drill down into specific segments or regions.
Why This Report Matters
The plant-based meat market is evolving quickly. New products are entering retail shelves. Manufacturing processes are becoming more efficient. Consumer acceptance continues to grow. All of these changes create both opportunities and challenges.
This report helps you navigate that complexity. It gives you verified data instead of guesswork and offers cross-segment comparisons instead of isolated facts. It provides actionable insights instead of vague recommendations.
Whether you are an investor evaluating opportunities, a company planning your next move, or a researcher tracking industry trends, this study has something for you. The combination of macro and micro-level insights ensures you do not miss important details.
Final Thoughts
The global plant-based meat market is on a strong growth trajectory. With a current value of $18.7 billion and a projected future value of $54.8 billion, the sector offers significant potential. The 11.35% CAGR reflects steady and sustainable expansion.
Roots Analysis has delivered a report that balances depth with clarity. It avoids speculation and sticks to evidence-based findings. It covers technological advances, company strategies, and regional dynamics. Most importantly, it presents everything in a way that supports real-world decision-making.
If you need reliable market intelligence for the plant-based meat space, this report provides a solid foundation. You can use it to validate your assumptions, identify new opportunities, and stay ahead of the competition.
-
Business3 years ago
Cybersecurity Consulting Company SequelNet Provides Critical IT Support Services to Medical Billing Firm, Medical Optimum
-
Business3 years ago
Team Communication Software Transforms Operations at Finance Innovate
-
Business3 years ago
Project Management Tool Transforms Long Island Business
-
Business3 years ago
How Alleviate Poverty Utilized IPPBX’s All-in-One Solution to Transform Lives in New York City
-
Entertainment3 years ago
Jurassic World Dominion’ Roars to Box Office Triumph – A Jurassic Phenomenon
-
Fashion3 years ago
Why you should approach me if you’re looking for a creative collaborator
-
Fashion3 years ago
Overcoming Social Anxiety Tips for Interacting with Non-Aggressive People
-
Sports3 years ago
Understanding C.T.E. Odds in the NFL: Cracking the Helmet Code