Technology Explained
The 5 Best SSH Clients for Mac

Introduction: Best SSH Clients for Mac
In today’s digital age, remote access and control of other computers through an encrypted connection have become indispensable. Secure Shell (SSH) clients are the key to achieving this, and if you’re a Mac user, you’re in luck. Mac offers a variety of SSH clients, each with its own unique features and advantages. In this article, we’ll explore the top five SSH clients for Mac and help you decide which one is the best fit for your needs.
1. Terminal: The Mac’s Built-In SSH Client
SSH Made Simple and Free
For those with coding experience or those who enjoy the simplicity of a text-based interface, Mac’s built-in SSH client, Terminal, is a reliable choice. This free application allows you to access and control remote computers via SSH connections. It’s pre-installed on your Mac, making it the go-to choice for many users. With Terminal, you can quickly log into remote servers and execute commands to access files and run programs on other computers. If you have some coding background, this tool is a convenient option, and the fact that it’s already on your Mac makes it hard to beat.
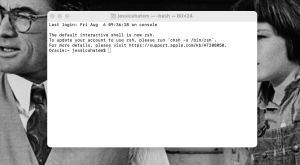
Image by https://www.makeuseof.com/
Table: Terminal – The Mac’s Built-In SSH Client
| Features | Pros | Cons |
|---|---|---|
| Built-in and free | Easy accessibility | Text-based interface |
| Command-line access | Fast and efficient | Steeper learning curve |
| Ideal for coding experts | Limited graphical interface |
2. PuTTY for Mac
A Windows Classic on Mac
PuTTY, a popular SSH client for Windows, is also available for Mac users. While Mac comes with its Terminal, PuTTY for Mac fills the void for those transitioning from Windows. It offers a graphical user interface and the ability to save login and session information, making it a practical choice for SSH connections on Mac. You can manage your SSH login information, saving time and enhancing the user experience.
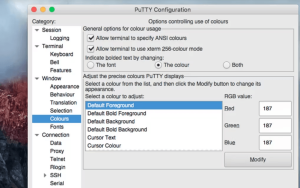
Image by https://www.makeuseof.com/
Table: PuTTY for Mac – The Windows Classic on Mac
| Features | Pros | Cons |
|---|---|---|
| Windows classic on Mac | User-friendly GUI | Redundant with Terminal |
| SSH connections with ease | Time-saving login info | Graphical interface may be preferred |
| Practical for Windows users | Similar basic functions as Terminal |
3. iTerm2
The Advanced Terminal Replacement
iTerm2 is the SSH client for Mac users who seek an advanced alternative to the native Terminal. While iTerm2 facilitates SSH connections, it goes beyond the basics with a plethora of additional features. This client supports split panes, search functionality, and easy copying and pasting. It even boasts an Instant Replay feature, enabling you to recover deleted text. For SSH enthusiasts and power users, iTerm2 offers unmatched capabilities.
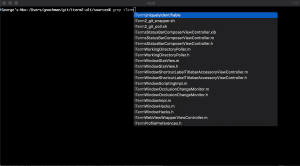
Image by https://www.makeuseof.com/
Table: iTerm2 – The Advanced Terminal Replacement
| Features | Pros | Cons |
|---|---|---|
| Advanced Terminal features | Split panes for multitasking | Learning curve for beginners |
| Search functionality | Instant Replay for text recovery | Extensive features may overwhelm |
| Efficient SSH navigation | Paste history |
4. Termius
Cross-Platform SSH Client
Termius is a versatile SSH client that extends its reach across Mac, Windows, Linux, and even mobile devices. If you need to access SSH servers on various platforms, Termius is an excellent choice. It features autocomplete functionality and the ability to save frequently used commands. Moreover, it offers a graphical user interface for Secure File Transfer Protocol (SFTP), simplifying file sharing between devices via SSH connections.
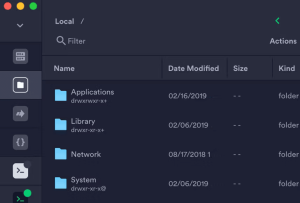
Image by https://www.makeuseof.com/
Table: Termius – The Cross-Platform SSH Client
| Features | Pros | Cons |
|---|---|---|
| Cross-platform compatibility | Autocomplete for quick typing | Premium features come at a cost |
| SFTP GUI for file sharing | Command-saving capabilities | Free version lacks SFTP GUI |
| Versatile and user-friendly | Multi-device support |
5. ZOC Terminal
The Organizational SSH Client
ZOC Terminal stands out as an SSH client that prioritizes organization and customization. It allows users to open multiple Terminal tabs, color-coding each for easy reference. The emulator maintains an “address book” for folders and hosts, making it efficient for managing different servers. ZOC Terminal also permits extensive keyboard remapping, hotkey shortcuts, and customized button bars, catering to those who are well-versed in Terminal and command line operations.
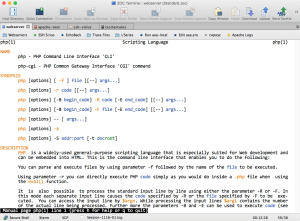
Image by https://www.makeuseof.com/
Table: ZOC Terminal – The Organizational SSH Client
| Features | Pros | Cons |
|---|---|---|
| Organized and customizable | Multiple tabs with color-coding | Requires advanced Terminal knowledge |
| Address book for quick access | Extensive keyboard remapping | Complex for beginners |
| Convenient for repetitive tasks | Quick access to commands |
Conclusion: Choosing the Right SSH Client for Mac
While Mac’s built-in Terminal is a reliable and free option, the other SSH clients mentioned offer enhanced features and user-friendly interfaces. The choice ultimately depends on your preferences and needs. If you’re a coding expert who values simplicity, Terminal is perfect. PuTTY for Mac caters to Windows users familiar with its interface. iTerm2 is ideal for power users who seek advanced functionality. Termius is the cross-platform solution for multi-device access, and ZOC Terminal excels in organization and customization.
Remember, your SSH client should align with your SSH usage and personal preferences. With the right choice, you can streamline your remote access and enjoy secure and efficient connections.
In the world of Mac SSH clients, there’s no shortage of options. Find the one that suits you best and make your remote computing experience more efficient and secure.
Business
Columbus Colleges: Enrollment Through Better Web Design

Columbus’s colleges are losing students to other schools simply because their websites are better structured. I found that when I audited 15 local colleges, poor design was running rampant across the board—most are fixable as well.
Slow Load Times on Mobile Devices
Ohio State’s primary website loads in just 2.3 seconds on a mobile device. Conversely, Columbus State’s website loads in 8.7 seconds. Given that 73% of prospective students use smartphones to browse, that’s not just slow, it’s a death sentence for admissions.
The Solution: Any reputable web design company in Columbus will tell you that mobile-first design is no longer up for discussion. Pages should load in 3 seconds or less, forms should be usable with a thumb, and navigation should be thumb-friendly. CCAD (Columbus College of Art and Design) just redesigned its website using these principles, and its applications have increased by 34% since the redesign.

Invisible in local search results
If you enter “colleges around Columbus” on a search engine (Google), you will see Ohio State as the only college that shows up. However, when searching for community colleges and other specialised institutions, you will find these institutions ranking around page 3 or lower for their named programs.
The problem: No GMB (Google My Business) optimisation. Franklin University even fails to fully claim their GMB listing. Their address is commonly listed as “temporarily closed.”
The Solution: Create and then optimize all campus addresses through both Google and business directory listings. Include photographs, create labels to respond to people reviewing your school, and post recent updates relating to the available enrollment periods. You want colleges to be able to locate you locally first when a prospective student types in “nursing programs Columbus” and you are visible in the map section.
Content That Converts Students
The college sites of most institutions are written in an academic style – high-density paragraphs about “excellence of the institution” and “a transformative learning experience.” When students are looking for information, they are looking for answers to questions such as how long it will take to complete the program, how much it will cost, and will there be any job opportunities upon completion.
For example, Otterbein University’s nursing website includes 847 words of content; however, it does not include the starting salary for a graduate until paragraph six. A competing institution’s website leads with, “96% job placement rate with an average starting salary of $65,000.”
Solution: answer the money questions up front and create program pages that convert:
- Job placement rates (with 3rd party sources).
- Graduate’s average starting salaries.
- Total program cost (not just tuition).
- Time to complete the program.
- Prerequisite information listed in plain English
Technical SEO Disasters
Most of the Columbus, Ohio college websites fail to meet the industry’s minimum criteria for Search Engine Optimization (SEO), which lead to decreased rankings in all search engines. The common issues we found include:
1. Broken internal links.
2. Missing alt tags on images.
3. Duplicate content across program pages (Capital University has 23 pages with the same meta description).
Some additional key technical issues that hamper the rankings on all college websites include:
1. No schema markup for either program or location.
2. Slow server response times.
3. Missing SSL certificate on multiple application forms.
4. Broken mobile navigation for multiple programs.
5. No local business structured data to support citation and rankings.
These common technical issues are far more than technical; they are also killing your rankings. Google cannot recommend college’s websites to its visitors if those sites are not accessible to Google through its crawler or can be understood once crawled.
The Death of Enrollment Forms
67% of potential students who fill out inquiry forms at Columbus colleges are lost at the inquiry stage. Why does this happen? Schools are using inquiry forms that require up to 15 fields when 4 would suffice, not having mobile-optimized inquiries, and having broken “Submit” buttons.
Delaware County Community College cut their inquiry form from 12 fields down to only 3 fields, resulting in an 89% increase in inquiries over 2 months.
Successful Examples of Results
Columbus State Community College worked with an SEO Services Columbus that specializes in local search engine optimisation and experienced the benefits:
- 156% more traffic through organic search
- 43% additional program inquiries
- Increased performance in local search results for targeted programs
Their formula for success: a mobile-first redesign, aggressive optimization of their Google My Business profile across their campuses, and totally answering students’ questions using quality content.
To sum it up
Ohio colleges have to compete against Arizona and Florida Colleges’ web-based programs with better web pages and better collegiate leads search engine optimization, so there’s no longer a local marketplace for columbus schools to get their students from.
It’s really easy to fix the problem. You’ll need to work with a web design company who understands education marketing, and to do that, you need to optimize the site for local search and generate content that gets visitors to apply.
Your competitors are already doing this, and if you wait to make decisions about how many more students you will lose to your competitors.
If you are ready to improve your school’s web presence, do a technical audit, make your mobile experience priority, and claim local search results. In a competitive academic landscape, your website serves not just for promotion, but as your enrollment powerhouse.
Technology
AI-Integrated Zillow Clone App Development
Digital Development
Boldify for Facebook: Quick Bold Text in Seconds
Scroll through Facebook for just five minutes and you’ll notice something: most posts look exactly the same. Plain text blends into the feed, making it easy for users to scroll past without noticing important messages. In a crowded social media environment, visual formatting plays a major role in grabbing attention and increasing engagement. This is where Boldify, a powerful bold text generator, makes a difference. Instead of struggling with plain, unformatted posts, Boldify allows you to create eye-catching Facebook bold text instantly. In this article, you’ll learn why bold text matters, how Boldify works, and how you can use it to stand out on Facebook within seconds.
Why Bold Text Matters on Facebook (User Engagement Psychology)
Facebook is a fast-moving platform. Users scroll quickly, often stopping only when something visually stands out. Bold text works because it creates contrast. When certain words appear heavier or more prominent, the brain processes them faster.
Here’s why bold text improves engagement:
- It grabs attention in crowded feeds.
- It improves readability and scan ability.
- It highlights key messages instantly.
Bold formatting is especially powerful in:
- Facebook posts
- Comments
- Bios
- Facebook groups
If you’re building a brand or growing a personal profile, bold text strengthens your identity. It emphasizes important announcements, promotions, or calls to action, making your message harder to ignore.

The Challenge: Facebook Doesn’t Offer Built-In Bold Formatting
One of the biggest frustrations for users is that Facebook does not provide built-in bold formatting for regular posts. Unlike word processors, you cannot simply select text and click “Bold.”
That’s why many people search for:
- how to bold text on Facebook
- Facebook bold text generator
- bold letters for Facebook
Without a proper tool, users are left copying complicated codes or trying ineffective formatting tricks. This creates a clear need for a reliable and easy-to-use bold font generator.
What Is Boldify?
Boldify is an online bold text generator designed to help users create stylish bold letters instantly. Instead of modifying Facebook’s formatting, Boldify uses Unicode-based bold fonts that are fully compatible with social media platforms.
Here’s what makes Boldify simple and powerful:
- No installation required
- Works directly in your browser
- Free and instant access
- Compatible with Facebook, Instagram, Twitter, and WhatsApp
Because it uses special Unicode characters, the bold text appears naturally once pasted into Facebook posts, comments, bios, or Messenger chats. This makes Boldify a practical and beginner-friendly solution for anyone looking to create bold text online.
How Boldify Helps You Create Bold Facebook Text in Seconds
Using Boldify is straightforward and requires no technical knowledge. Here’s a simple step-by-step guide:
Step 1: Enter Your Text
Open Boldify and type your message into the input box. This could be a status update, promotional message, announcement, or bio line.
Example:
New Blog Post Live
Limited Time Offer
Join Our Community Today
Step 2: Automatic Bold Conversion
As soon as you enter your text, Boldify automatically converts it into multiple bold font styles. Within seconds, you’ll see several variations generated instantly.
Step 3: Copy and Paste to Facebook
Choose the bold style you like, click the copy button, and paste it directly into:
- Facebook posts
- Comments
- Bios
- Messenger chats
That’s it. In just a few seconds, your plain text becomes visually powerful Facebook bold text.
Key Features That Make Boldify Stand Out
There are many tools online, but Boldify offers specific advantages that make it reliable and user-friendly.
1. One-Click Copy Feature
No need to manually select text. Just click and copy instantly.
2. Multiple Bold Style Variations
Get access to different bold styles to match your tone and branding.
3. Mobile-Friendly Interface
Boldify works smoothly on smartphones, tablets, and desktops.
4. No Login Required
You don’t need to create an account. Just open and start using.
5. Fast Performance
Text conversion happens instantly without delays.
6. Clean and Simple Design
The interface is distraction-free, making it easy for beginners to use.
These features make Boldify more than just a basic bold letters generator—it becomes a practical social media enhancement tool.
Practical Ways to Use Bold Text on Facebook
Now that you know how to generate bold text, let’s explore practical ways to use it effectively.
Highlight Important Announcements
SALE TODAY ONLY
Registration Closes Tonight
Bold formatting ensures these messages get noticed quickly.
Strengthen Call-to-Actions
Instead of writing:
Join us now
Write:
JOIN US NOW
It creates urgency and clarity.
Emphasize Keywords in Posts
Highlight important parts of your message to guide the reader’s attention.
Improve Facebook Bios
Use bold text to make your profession, tagline, or brand name stand out.
Stand Out in Facebook Groups
When commenting in large groups, bold text increases visibility and improves response rates.
SEO & Branding Benefits of Using Bold Text
While bold text doesn’t directly change Facebook’s algorithm, it improves how users interact with your content.
Here’s how it benefits branding and visibility:
- Improves readability
- Encourages longer post engagement
- Strengthens personal or business branding
- Creates structured content hierarchy
- Makes posts look professional
When your content looks organized and visually appealing, users are more likely to stop scrolling and engage.
Tips for Using Bold Text Effectively
Bold text is powerful—but only when used strategically.
- Don’t overuse bold formatting.
- Highlight only key phrases or calls-to-action.
- Combine bold text with emojis carefully.
- Maintain readability and spacing.
Too much bold text can reduce its impact. The goal is to enhance clarity, not overwhelm the reader.
Conclusion
Standing out on Facebook is no longer optional—it’s necessary. Since Facebook doesn’t offer built-in bold formatting for posts, tools like Boldify provide a fast and effective solution.
-
Business3 years ago
Cybersecurity Consulting Company SequelNet Provides Critical IT Support Services to Medical Billing Firm, Medical Optimum
-
Business3 years ago
Team Communication Software Transforms Operations at Finance Innovate
-
Business3 years ago
Project Management Tool Transforms Long Island Business
-
Business3 years ago
How Alleviate Poverty Utilized IPPBX’s All-in-One Solution to Transform Lives in New York City
-
health3 years ago
Breast Cancer: The Imperative Role of Mammograms in Screening and Early Detection
-
Sports3 years ago
Unstoppable Collaboration: D.C.’s Citi Open and Silicon Valley Classic Unite to Propel Women’s Tennis to New Heights
-
Art /Entertainment3 years ago
Embracing Renewal: Sizdabedar Celebrations Unite Iranians in New York’s Eisenhower Park
-
Finance3 years ago
The Benefits of Starting a Side Hustle for Financial Freedom

































