Technology
How to Delete Private Browsing History and Protect Your Privacy

Private Browsing History and Protect Your Privacy
In today’s digital age, privacy is a valuable commodity, and many of us turn to incognito or Private Browsing mode to shield our online activities. However, the illusion of complete anonymity that incognito mode provides can be deceptive. In this article, we’ll explore why incognito mode falls short in protecting your privacy and, more importantly, how to delete your private browsing history effectively. We’ll also delve into expert-recommended practices to safeguard your digital footprint. Let’s dive in.
Is Incognito Mode Truly Private?
When you activate incognito mode in your web browser, it’s easy to assume that your online actions become invisible to prying eyes. Regrettably, this isn’t entirely accurate. Your Internet Service Provider (ISP) and third-party entities can still trace your online activity, even while you’re in private browsing mode. If you share your device with others, they can also uncover your incognito browsing history. So, how is this possible?
How Is Your Browsing History Saved in Incognito Mode?
While incognito mode does prevent your browser from saving your web queries and visited websites, it’s not a foolproof method for private browsing. Your ISP continues to collect and store data about your online activities, including the websites you visit, even when using incognito mode.
Moreover, some websites may track your IP address, circumventing your browser’s attempts at anonymity. Even if your history isn’t saved locally, other services and websites may retain records of your visits.
To complicate matters further, your device maintains a DNS cache of your browsing session, whether in normal or incognito mode. This cache includes domain names and their associated IP addresses, making it accessible to anyone using your computer. To fortify your privacy, it’s crucial to eliminate your DNS cache and erase all traces of your browsing session.

Image by https://www.makeuseof.com/
Can Private Browsing History Be Tracked?
In essence, private browsing, such as incognito mode, aims to prevent your browser from storing your browsing history, cookies, and site data. However, it doesn’t offer complete anonymity. Your ISP and certain websites can still monitor your online activities, leaving your browsing history susceptible to tracking.
Deleting Incognito History: Step by Step
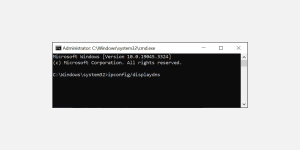
Viewing Private Browsing History on Windows PC
To view your private browsing history on a Windows PC, follow these steps:
- Press Windows + R to open the Run Command Window.
- Type “cmd” and press Ctrl + Shift + Enter to launch the Command Prompt with administrative privileges.
- In the command prompt window, type “ipconfig/displaydns” and press Enter.
Image by https://www.makeuseof.com/
A list of recently accessed websites will appear with their IP addresses. This includes websites visited in both private browsing and normal browsing mode.
Image by https://www.makeuseof.com/
This will display a list of recently accessed websites, encompassing both private and normal browsing history.
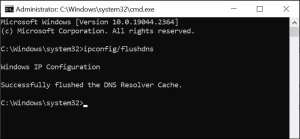
How to Delete Incognito History on a PC
When you’ve finished your private browsing session, it’s important to delete any traces of your incognito history from the DNS cache.
Here is how to do that on a Windows PC:
- Press Windows + R to launch Run Command Window.
- Type “cmd” in the Run dialogue box and press Ctrl + Shift + Enter to open the Command Prompt with administrative rights.
Image by https://www.makeuseof.com/
In the command prompt window, type “ipconfig/flushdns” and press the Enter key.
Image by https://www.makeuseof.com/
This will delete your DNS cache and clear all traces of your recent browsing session.
Viewing Incognito History on Android and iOS
On Android and iOS devices, official methods to view incognito history are limited. However, you can use third-party apps like FamilyTime, KidsGuard, or Hoverwatch to access incognito history. Note that while you can view it, you cannot delete it or access previous incognito records.
How to Delete Incognito History on Android
The steps to delete incognito history on an Android device are quite simple. All you need to do is use the Chrome browser and follow these steps to clear the DNS cache:
- On your Android device, launch the Chrome browser.
- In the address bar, type “chrome://net-internals/#dns” and hit Enter.
- Tap the Clear host cache button to delete the device’s DNS cache.
- Close Chrome
- Image by https://www.makeuseof.com/
- Image by https://www.makeuseof.com/
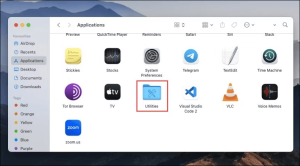
How to Delete Incognito History on Mac
On Mac devices, you can easily flush the DNS cache and delete your incognito browsing history by using the Terminal command.
Here is how to do that:
- On your Mac device, launch Applications, and select Utilities.
Image by https://www.makeuseof.com/
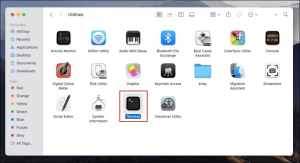
Under Utilities, look for the Terminal and double-click on it to launch it.
Image by https://www.makeuseof.com/
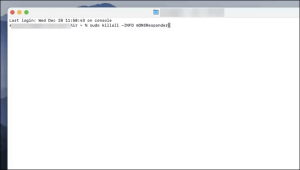
In the Terminal window, type the command, “sudo killall -HUP mDNSResponder“, and hit the enter key. You will be asked to enter your password to continue.
Image by https://www.makeuseof.com/
How to Clear Incognito History on iPhone
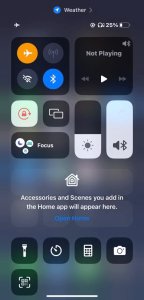
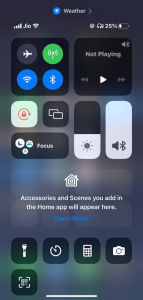
If you use an iPhone, it’s easy to clear the DNS cache, thereby deleting your private browsing history. You just have to toggle the Airplane Mode On and Off. Here is how to do that:
- On your iPhone, swipe down from the top-right corner of the screen to expand Control Center.
- Tap on the Airplane Mode icon to toggle it on.
- Wait for a few seconds and then toggle it off again
- Image by https://www.makeuseof.com/
- Image by https://www.makeuseof.com/
This will delete all the accumulated DNS cache from your device and clear your private browsing history.
Privately Browsing the Internet: Best Practices
If you’re committed to browsing the web privately, consider the following strategies:
- Install a Reliable VPN: A Virtual Private Network (VPN) encrypts your internet traffic and conceals your IP address, enhancing online privacy.
- Use a Secure Web Browser: Opt for secure browsers like Tor to maximize online privacy and security.
- Utilize a Private Search Engine: Switch to private-focused search engines like DuckDuckGo to safeguard your browsing history.
- Regularly Clear Browsing Data: Remove browsing data from your devices periodically to eliminate session traces.
- Delete Your DNS Cache: Routinely clear your DNS cache to erase records of recent website visits, even in incognito mode.
How Often Should You Clear Your DNS Cache?
The frequency of clearing your DNS cache should align with your browsing habits, especially if you frequently use incognito mode or value online privacy. Regularly deleting your DNS cache helps minimize third-party knowledge about your browsing activities.
Protect Your Privacy
While incognito mode offers a layer of privacy, it’s not a silver bullet for complete anonymity. To protect your digital footprint comprehensively, employ a reliable VPN, choose secure browsers, and consistently clear your browsing data and DNS cache. By taking these steps, you’ll empower yourself to navigate the digital realm with greater confidence and privacy.
About the Author
Pranav Bhardwaj is an expert in online privacy and cybersecurity. With over a decade of experience, Pranav has provided valuable insights to individuals and organizations seeking to protect their digital presence. His expertise in the field makes him a trusted authority on online privacy.
In conclusion, while incognito mode provides a degree of privacy, it’s not infallible. To truly safeguard your online activities, follow the expert advice provided in this article. By understanding how to delete private browsing history effectively and implementing best practices, you can take control of your digital privacy. Your online presence is worth protecting, and with the right knowledge, you can do just that.
Development
Unreal vs Unity Engine 2026: Which One Should You Choose?
Technology
Software Development Company: Services for Digital Solutions

Every successful digital product begins with a simple idea—but transforming that idea into a scalable, high-performing solution requires more than just coding. It demands strategy, collaboration, innovation, and continuous improvement. This is where the power of a custom software development company offering full-cycle services truly shines.
In today’s competitive business environment, organizations are no longer looking for fragmented solutions. They want a unified approach that covers everything from concept to completion and beyond. By investing in full-cycle custom software development services, businesses can streamline processes, reduce risks, and build future-ready applications that evolve with their needs.
From Vision to Reality: The Full-Cycle Advantage
Imagine having a single team that understands your idea, designs your product, builds it, tests it, and continues to improve it even after launch. That’s the essence of custom full cycle software development services.
Unlike traditional development models, where different teams handle separate stages, full-cycle development integrates every phase into one cohesive workflow. This ensures consistency, better communication, and faster execution. A reliable custom software development company doesn’t just deliver a product—it becomes your long-term technology partner.
This approach eliminates the common challenges of miscommunication, delays, and quality gaps that often arise when multiple vendors are involved. Instead, it creates a seamless journey from ideation to deployment.
What Makes Full-Cycle Development a Smart Business Choice?
The modern business landscape demands agility and innovation. Companies must adapt quickly to changing market conditions, customer expectations, and technological advancements. Full-cycle development provides the flexibility needed to stay ahead.
With custom software development services, businesses gain access to a team that is aligned with their goals from day one. This alignment ensures that every feature, design element, and functionality contributes to the overall business objective.
Moreover, full-cycle development emphasizes continuous feedback and iteration. This means that improvements can be made at every stage, resulting in a product that is not only functional but also optimized for performance and user experience.

Key Benefits of Hiring a Full-Cycle Custom Software Development Company
1. End-to-End Expertise Under One Roof
One of the biggest advantages of hiring a custom software development company is access to a diverse team of experts. From business analysts and UI/UX designers to developers and QA engineers, every aspect of the project is handled by specialists who collaborate closely.
This integrated approach ensures that all components of the software work together seamlessly. It also reduces the need for external dependencies, making the development process more efficient and reliable.
2. Faster Time-to-Market
Speed is crucial in today’s fast-paced digital world. Full-cycle development uses agile methodologies to accelerate the development process without compromising quality.
By working in iterative cycles, teams can deliver functional versions of the product quickly, allowing businesses to launch sooner and start generating value. This is especially beneficial for startups and enterprises looking to gain a competitive edge.
3. Cost Efficiency and Better ROI
At first glance, full-cycle development may seem like a significant investment. However, it proves to be cost-effective in the long run.
By minimizing errors, reducing rework, and ensuring efficient resource utilization, full-cycle custom software development services help businesses save both time and money. Additionally, the focus on scalability ensures that the software can grow with your business, maximizing return on investment.
4. Continuous Support and Improvement
Software development doesn’t end with deployment. Regular updates, maintenance, and performance optimization are essential for long-term success.
A company offering custom full cycle software development services provides ongoing support, ensuring that your software remains up-to-date and competitive. This continuous improvement approach helps businesses adapt to changing market demands and technological advancements.
How Full-Cycle Development Enhances Product Quality
Quality is a critical factor in the success of any software product. Full-cycle development ensures high standards by integrating quality assurance into every stage of the process.
Instead of waiting until the end to test the product, teams conduct continuous testing throughout development. This proactive approach helps identify and resolve issues early, resulting in a more stable and reliable application.
Furthermore, the close collaboration between teams ensures that design, development, and testing are aligned. This leads to a cohesive product that delivers a seamless user experience.
The Role of Customization in Business Growth
Every business is unique, and its software should reflect that uniqueness. Off-the-shelf solutions often fall short in meeting specific requirements, leading to inefficiencies and limitations.
With custom software development services, businesses can create tailored solutions that align perfectly with their processes and goals. A custom software development company takes the time to understand your needs and builds software that supports your growth strategy.
Customization also allows for greater flexibility. As your business evolves, your software can be updated and expanded to meet new demands. This adaptability is essential for staying competitive in a dynamic market.
Bridging Innovation and Scalability
Innovation is at the heart of full-cycle development. By leveraging the latest technologies and best practices, development teams can create solutions that are both innovative and scalable.
Whether it’s integrating artificial intelligence, cloud computing, or advanced analytics, full-cycle custom software development services ensure that your software is future-ready. This not only enhances functionality but also provides a competitive advantage.
Scalability is another key benefit. As your user base grows, your software must be able to handle increased demand without compromising performance. Full-cycle development focuses on building robust architectures that support growth and expansion.
Why Businesses Are Moving Towards Full-Cycle Development
The shift towards full-cycle development is driven by the need for efficiency, flexibility, and innovation. Businesses are realizing that a fragmented approach to development can lead to delays, increased costs, and subpar results.
By choosing a custom software development company that offers end-to-end services, organizations can simplify their development process and achieve better outcomes. This approach not only improves efficiency but also enhances collaboration and transparency.
Moreover, full-cycle development aligns with modern business practices, such as agile and DevOps methodologies. These practices emphasize continuous improvement, rapid delivery, and customer-centric design, making them ideal for today’s digital landscape.
Choosing the Right Development Partner
Selecting the right partner is crucial for maximizing the benefits of full-cycle development. A reliable custom software development company should have a proven track record, technical expertise, and a client-focused approach.
Look for a company that offers comprehensive custom software development services, including consultation, design, development, testing, and maintenance. Strong communication and transparency are also essential for ensuring a smooth development process.
Additionally, consider the company’s ability to adapt to your specific needs. A good partner will not only deliver a high-quality product but also provide valuable insights and recommendations to help you achieve your business goals.
Conclusion
In a world where technology drives success, the way you build your software can make all the difference. Hiring a custom software development company that offers full-cycle custom software development services provides a strategic advantage that goes beyond technical execution.
From faster time-to-market and cost efficiency to enhanced quality and continuous improvement, the benefits of full-cycle development are undeniable. By embracing this approach, businesses can create powerful, scalable, and user-centric solutions that support long-term growth.
Digital Development
Native App Development Trends: AI, IoT, Cloud & Future Insights

The mobile app development landscape keeps changing because businesses need better methods to create their applications. React Native remains the most popular framework for cross-platform app development because it offers multiple development options. New trends will emerge for business mobile app strategies, which will use this powerful framework as we approach 2026.
React Native brings innovation to multiple industries through its ability to create faster development cycles and better user experiences. A business can maintain its competitive edge through a dependable react native app development partnership while using the most recent mobile technology developments.
The blog will examine the main React Native app development trends that businesses should monitor during 2026.
Why React Native Continues to Dominate Mobile App Development
Meta developed React Native as a framework that enables developers to create mobile applications through a shared codebase that supports both Android and iOS platforms. The approach leads to shorter development time while delivering stable performance across different devices.
Startups and enterprises choose the framework because its expanding ecosystem and strong community backing, and ongoing updates provide them with reliable support. Companies that partner with a react native app development firm can achieve three main advantages from their services, which include budget-friendly development, quick product launch, and easy system upkeep.

1. Rise of AI-Powered Mobile Applications
Mobile applications now include Artificial Intelligence (AI) as a fundamental element, which React Native developers use in their applications. The year 2026 will bring a major increase in AI-powered features, which include chatbots, recommendation engines, and predictive analytics tools.
Key Benefits
- Personalized user experiences
- Improved decision-making through data insights
- Enhanced automation in mobile apps
The super-flexibility of React Native gives developers the convenience of using AI-driven features on the spot, turning applications more intuitive and responsive to user activity.
2. Increased Adoption of Cross-Platform Development
The development of cross-platform applications has reached the point where it functions as an established industry standard. Companies select React Native because it helps them decrease expenses while accelerating their product launch process.
Through using one codebase, businesses achieve the ability to develop applications for various platforms while maintaining their product quality. A professional react native app development company ensures that applications deliver a native-like experience across devices.
3. Growth of IoT-Enabled Applications
The Internet of Things (IoT) transforms device interactions through its ecosystem, which depends on mobile applications. React Native enables developers to create applications that establish connections with IoT devices while managing their operations.
Use Cases
- Smart home applications
- Healthcare monitoring systems
- Industrial automation solutions
React Native will be there to support the process of creating scalable and efficient IoT-enabled mobile applications in the growth of IoT adoption.
4. Enhanced Performance with New Architecture
The new architecture of React Native, which includes Fabric and TurboModules, optimizes application performance through its improved features. The new advancements provide faster rendering capabilities, together with improved system responsiveness and enhanced user interaction experiences.
Key Improvements
- Reduced app load time
- Better memory management
- Improved UI responsiveness
Enterprises can use the services of a React Native app development partner to harness the same innovations to create powerful apps that can adequately fulfill the user’s expectations.
5. Integration of Augmented Reality (AR) and Virtual Reality (VR)
AR and VR technologies are becoming more popular in various sectors, including retail, healthcare, and education. The usage of React Native has grown to create mobile applications that include virtual reality and augmented reality experiences.
Examples
- Virtual product try-ons in eCommerce
- AR-based learning applications
- Virtual tours in real estate
The technologies extend user engagement while delivering distinct experiences, which have become the major trend for 2026.
6. Focus on App Security and Data Privacy
Cyber threats have increased to the point that companies now consider security as their main focus during mobile app development work. Companies now develop secure software products that protect their customers’ personal information while meeting all legal requirements.
Security Measures
- Data encryption
- Secure authentication methods
- Regular security updates
A trusted react native app development company implements robust security practices to safeguard applications against potential threats.
7. Growing Popularity of Cloud Integration
Cloud technology has become essential for developing modern applications. Developers use cloud platforms to improve the scalability and performance of their React Native applications.
Benefits of Cloud Integration
- Real-time data synchronization
- Improved storage capabilities
- Enhanced app scalability
This trend enables companies to create adaptable software solutions that can effectively manage increasing user demand.
8. Adoption of Microservices Architecture
Developers use microservices architecture because it provides an optimal way to create software that can handle increasing demand while maintaining easy maintenance. The approach lets developers create applications through the development of separate, self-sufficient parts.
Advantages
- Easier updates and maintenance
- Improved scalability
- Faster development cycles
The combination of React Native and microservices allows companies to create applications that use modular design and operational efficiency.
9. Expansion of Wearable App Development
People are increasingly adopting smartwatches and fitness tracking devices as their preferred wearable technology. Developers use React Native to create applications that work perfectly with these devices.
Use Cases
- Fitness tracking apps
- Health monitoring solutions
- Smart notifications and alerts
The ongoing growth of wearable technology will see React Native develop its systems to support new technological advancements.
10. Increased Use of Third-Party Plugins and Libraries
The ecosystem of React Native provides developers with various third-party plugins and libraries that help them build applications more efficiently while delivering advanced functionalities.
Benefits
- Reduced development time
- Access to pre-built components
- Improved app features
Businesses need to confirm that their plugins maintain security through regular updates to protect against potential vulnerabilities.
11. Focus on UI/UX Innovation
User experience remains a key factor in the success of any mobile application. In 2026, businesses are placing greater emphasis on creating intuitive and visually appealing interfaces.
Trends in UI/UX
- Minimalist design
- Dark mode support
- Smooth animations and transitions
The customizable components of React Native enable developers to build interactive user interfaces that provide a good user experience.
12. Growing Demand for On-Demand Applications
On-demand applications experience rising demand throughout multiple sectors, including food delivery, healthcare, and transportation. Developers prefer React Native for application development because it provides them with both fast performance and flexible development capabilities.
Key Features
- Real-time tracking
- Seamless payment integration
- Instant notifications
The development of scalable on-demand solutions needs a professional react native application development company that will create custom solutions that meet business requirements.
How Businesses Can Leverage These Trends
Businesses need to implement current mobile application development trends to maintain their competitive edge through 2026. The process demands both a strategic plan and an appropriate technological partnership.
Key Steps
- Identify business goals and user needs
- Choose the right technology stack
- Focus on scalability and security
- Collaborate with experienced developers
The use of a professional react native app development company allows businesses to build high-quality applications while effectively implementing current industry trends.
Future Outlook of React Native
The future of React Native demonstrates positive development prospects because its features continue to improve while more users adopt it across different sectors. React Native will continue to function as an essential component of mobile application development because businesses require solutions that deliver faster performance with greater efficiency at lower costs.
Developers will be able to build advanced applications through the enhanced capabilities that emerging technologies like AI, IoT, and AR/VR will bring to the system.
Conclusion
Your training includes information from December 2023. The framework demonstrates its capacity to adapt through 2026 because various technological trends and user requirements continue to evolve.
React Native leads multiple industries forward through its ability to integrate artificial intelligence and cloud computing and provide immersive user experiences. The digital market remains competitive, but businesses that monitor current trends and partner with dependable react native app development firms will achieve greater success.
Organizations can create high-performance applications that provide outstanding user experiences and sustainable value through their adoption of these new technologies.
FAQs
1. Why is React Native popular for mobile app development in 2026?
Businesses choose React Native because it enables them to develop applications for multiple platforms while reducing development time and operational costs. The framework allows businesses to create high-performance mobile applications through the development of their applications using one codebase, which makes it the top choice for contemporary mobile application development.
2. How can a react native app development company help businesses stay competitive?
A react native app development company helps businesses adopt the latest technologies, build scalable applications, and ensure faster time-to-market. Their expertise enables companies to create feature-rich apps aligned with current industry trends and user expectations.
3. Is React Native suitable for building high-performance applications?
Yes, React Native supports high-performance app development through its advanced architectural system, native system components, and its rendering system, which has been specifically optimized. The system delivers uninterrupted user experiences, which make it appropriate for developing extensive mobile applications that require advanced functionality in multiple business sectors.
4. What are the key trends shaping React Native app development in 2026?
The main trends of the current period demonstrate AI integration, IoT-enabled applications, cloud-based solutions, AR/VR experiences, and improved application security. The current trends enable businesses to develop advanced mobile applications that use React Native to create intelligent, and interactive, and expandable systems.
-
Business3 years ago
Cybersecurity Consulting Company SequelNet Provides Critical IT Support Services to Medical Billing Firm, Medical Optimum
-
Business3 years ago
Team Communication Software Transforms Operations at Finance Innovate
-
Business3 years ago
Project Management Tool Transforms Long Island Business
-
Business3 years ago
How Alleviate Poverty Utilized IPPBX’s All-in-One Solution to Transform Lives in New York City
-
health3 years ago
Breast Cancer: The Imperative Role of Mammograms in Screening and Early Detection
-
Sports3 years ago
Unstoppable Collaboration: D.C.’s Citi Open and Silicon Valley Classic Unite to Propel Women’s Tennis to New Heights
-
Art /Entertainment3 years ago
Embracing Renewal: Sizdabedar Celebrations Unite Iranians in New York’s Eisenhower Park
-
Finance3 years ago
The Benefits of Starting a Side Hustle for Financial Freedom