Technology
Cybersecurity in a Hyper-Connected World: Protecting Your Digital Life in 2025

Introduction
Imagine a world where almost everything is connected through the internet. In 2025, our lives depend on computers, smartphones, and the internet more than ever before. Cybersecurity is the shield that Protects our Digital Life. It helps keep our personal information safe from cyber threats and online dangers. This guide will show you how to protect yourself in a hyper-connected world using simple language. Even kids can learn about online safety and why cybersecurity is important.
What is Cybersecurity?

Image by: Yandex.com
Cybersecurity is the practice of protecting computers, networks, and data from unauthorized access and harm. It acts like a digital lock that stops bad people from stealing information or causing damage. When we talk about cybersecurity, we mean keeping our digital life safe. This includes protecting passwords, personal details, and even the devices we use every day. With so many gadgets connected to the internet, practicing good cybersecurity is essential in today’s world.
What is a Hyper-Connected World?
A hyper-connected world is a term used to describe how everything is linked through the internet. From smart homes and cars to mobile devices and computers, almost every part of our life is connected. In this world, we can talk to friends instantly, share pictures, and learn new things with just a click. However, being hyper-connected also means we need to be careful. Without proper cybersecurity, our personal information can be at risk. It is important to protect ourselves in a world where data travels fast.
The Importance of Protecting Your Digital Life

Image by: Yandex.com
In our modern world, our digital life holds a lot of valuable information. This includes your photos, messages, school work, and even your game scores. Keeping these safe is very important. Cybersecurity helps protect this information from cyber threats like viruses, hackers, and phishing scams. By using strong passwords, updating software, and being careful online, you can keep your digital life secure. Remember, protecting your online identity is like locking your house to keep it safe.
How to Stay Safe with Cybersecurity
Staying safe online can be simple with a few good habits. First, always use strong and unique passwords for your accounts. A strong password is hard to guess and uses letters, numbers, and symbols. Second, never share your personal details with strangers online. Third, keep your software and apps updated. Updates often include fixes that protect you from new threats. Fourth, be cautious when clicking on links in emails or messages. These simple steps make your cybersecurity stronger and help protect your digital life.
What are Common Cyber Threats?

Image by: Yandex.com
Understanding common cyber threats can help you avoid them. Some of the most common threats include viruses, malware, and phishing scams. Viruses can damage your computer or steal information. Malware is software that is designed to harm your device or spy on you. Phishing scams try to trick you into giving away your personal details by pretending to be a trustworthy source. Being aware of these threats is the first step in protecting yourself in a hyper-connected world.
Building Strong Cybersecurity Habits
Developing good cybersecurity habits can protect you every day. Start by creating a habit of changing your passwords regularly. Use different passwords for different accounts to reduce the risk of a breach. Be cautious when using public Wi-Fi networks. Public networks can be less secure, so avoid logging into important accounts when you are not on a trusted connection. Educate yourself and your family about safe internet practices. By building these habits, you create a strong defense for your digital life.
The Future of Cybersecurity in 2025

Image by: Yandex.com
As technology advances, cybersecurity becomes even more important. In 2025, new gadgets and smart devices will make our lives easier, but they also bring new risks. Experts are working on advanced security measures like artificial intelligence and improved encryption to protect our digital life. The future promises even smarter ways to keep data safe. This means that while technology will become more complex, so will the tools we use to protect it. Staying informed and updating our habits will be key to thriving in a hyper-connected world.
Table: Cybersecurity Practices vs. Cyber Threats
| Aspect | Cybersecurity Practices | Cyber Threats |
|---|---|---|
| Password Management | Use strong, unique passwords, change regularly | Weak passwords that are easy to guess |
| Software Updates | Regularly update apps and operating systems | Outdated software vulnerable to attacks |
| Personal Data Protection | Avoid sharing personal information online | Identity theft and phishing scams |
| Safe Browsing | Be cautious of suspicious links and emails | Malware and viruses through unsafe links |
| Network Security | Use secure, trusted networks; avoid public Wi-Fi | Unsecured networks leading to data breaches |
This table compares simple cybersecurity practices with common cyber threats. Following these practices can help keep your digital life safe in a hyper-connected world.
Tips for Enhancing Your Digital Safety

Image by: Yandex.com
To further enhance your digital safety, consider these tips:
- Use Two-Factor Authentication: This adds an extra layer of security to your accounts.
- Educate Yourself: Learn about new threats and safety measures through trusted sources.
- Regular Backups: Keep copies of your important files in a secure place.
- Parental Controls: Use these tools to keep children safe online.
- Stay Updated: Follow cybersecurity news to stay informed about the latest trends and threats.
These tips are simple and effective ways to boost your cybersecurity and protect your digital life.
How Cybersecurity Affects Our Daily Lives
Cybersecurity is not just a buzzword; it affects our daily lives in many ways. It protects our online banking, our social media accounts, and even our school work. By keeping our devices secure, we can enjoy technology without worry. Whether it is sending an email or playing an online game, good cybersecurity practices make a big difference. They ensure that our digital interactions remain safe and that our personal data stays private. This way, we can focus on learning, playing, and connecting with friends.
The Role of Digital Literacy in Cyber Protection

Image by: Yandex.com
Digital literacy is the ability to use technology safely and effectively. Learning about cybersecurity is an important part of being digitally literate. It means understanding how to protect your digital life and knowing what to do when you encounter a threat. Schools and parents can help by teaching kids about online safety and responsible internet use. Being digitally literate means you are better prepared to handle the challenges of a hyper-connected world. It empowers you to use technology wisely and safely.
How to Educate Others About Cybersecurity
One of the best ways to promote cybersecurity is by sharing what you know with others. Talk to your friends and family about safe online habits. Explain why it is important to use strong passwords and avoid suspicious links. You can even organize fun workshops or activities that teach digital safety in an engaging way. By spreading the word, you help create a safer digital community. Education is key to ensuring that everyone, from kids to adults, is protected in our increasingly connected world.
The Impact of Cybersecurity on Business and Society

Image by: Yandex.com
Businesses and organizations also rely heavily on cybersecurity to protect their data and operations. When companies invest in strong cybersecurity measures, they not only protect their own information but also the data of their customers. This builds trust and improves overall safety in the digital marketplace. In society, effective cybersecurity helps prevent large-scale data breaches and cyber attacks that can disrupt our lives. By understanding and supporting good cybersecurity practices, we all contribute to a safer and more secure digital world.
FAQs
Q1: What is cybersecurity?
A: Cybersecurity is the practice of protecting computers, networks, and data from unauthorized access, ensuring that your digital life remains safe in a hyper-connected world.
Q2: How can I protect my digital life?
A: You can protect your digital life by using strong passwords, updating software regularly, and being cautious with personal information online.
Q3: What does it mean to live in a hyper-connected world?
A: A hyper-connected world is one where many devices are linked through the internet, making our daily lives more convenient but also requiring strong cybersecurity.
Q4: Why is digital literacy important for cybersecurity?
A: Digital literacy helps you understand and use technology safely, enabling you to protect your digital life and avoid cyber threats.
Q5: What are some common cyber threats?
A: Common cyber threats include viruses, malware, phishing scams, and identity theft, which cybersecurity measures work to prevent.
Conclusion
Cybersecurity in 2025 is essential for protecting your digital life in a Hyper-Connected World. By adopting strong safety habits, learning about digital literacy, and staying updated on threats, you secure your personal information and enjoy online activities with peace of mind. Responsible online behavior not only safeguards individuals but also contributes to a safer community, enabling a secure digital future for everyone.
Business
Best Low Code Development Platforms 2026

A few years ago, choosing software was simple.
You picked a CRM.
>You added an ERP.
>You connected a few tools.
And that was enough.
But in 2026, that approach no longer works.
Systems have become more complex.
Data moves faster.
Workflows demand real-time execution.
And the biggest challenge is no longer building software.
It’s making everything work together.
That’s why low code platforms are no longer just a trend; they’ve become part of how modern enterprises think about software.
Why Low Code Is Gaining Momentum in 2026
The shift toward low code is not just about speed.
It’s about reducing complexity.
Enterprises today are dealing with:
- Fragmented systems
- Multiple integrations
- Increasing maintenance overhead
- Delays caused by disconnected workflows
A low code application development platform addresses these challenges by allowing systems to be built within a unified environment.
This changes how software behaves.
Instead of connecting tools, businesses start building systems that are already connected.

What Defines the Best Low Code Development Platforms
Not every platform labeled as one of the best low code development platforms is designed for enterprise use.
In 2026, the criteria have evolved.
It’s no longer about drag-and-drop interfaces alone.
Key Capabilities to Look For
1. Platform Architecture
- Unified data models
- Integrated workflows
- Minimal dependency on external integrations
2. Scalability
- Ability to handle high concurrency
- Support for large datasets
- Stable performance under heavy workloads
3. Automation and Workflow Design
- Built-in automation capabilities
- Real-time process execution
- Flexible workflow configuration
4. Deployment Flexibility
- Cloud, private cloud, or on-premise options
- No forced SaaS lock-in
5. Governance and Security
- Centralized control
- Role-based access
- Data governance within the platform
A strong low code application development platform should meet all of these requirements.
The Shift from Integration to Unification
Traditional enterprise systems rely on integration.
But integration comes with trade-offs:
- Increased complexity
- Higher maintenance costs
- Risk of data inconsistencies
The best platforms in 2026 focus on unification instead.
That means:
- Systems operate within one environment
- Data is consistent across applications
- Workflows don’t depend on multiple tools
This shift is subtle but critical.
It reduces friction across operations.
Use Cases Driving Low Code Adoption
Enterprises are not adopting low code for experimentation.
They are using it to build core systems.
Common Use Cases
- ERP systems
- CRM platforms
- HR and workforce management
- Warehouse and logistics systems
- Analytics and reporting dashboards
- Custom operational applications
The key advantage is that all these applications can run on the same platform.
Evaluating Low Code Platforms for Long-Term Use
Choosing a platform is not just a technical decision.
It’s a strategic one.
Here’s what enterprises should consider:
System Longevity
- Will the platform remain stable as the business grows?
- Can it adapt to new requirements without rebuilding?
Data Consistency
- Is there a single source of truth?
- Are updates reflected in real time?
Operational Efficiency
- Does the platform reduce manual work?
- Are workflows reliable without constant fixes?
Complexity Management
- Does it simplify architecture or add another layer?
The best platforms reduce complexity instead of managing it.
Airtool and the Platform Approach
As enterprises move toward unified systems, platforms like Airtool represent a different direction.
Instead of focusing only on development speed, the emphasis is on simplifying architecture.
If you explore how a
low code application development platform
fits into this model, it becomes clear that the goal is not just faster applications.
It’s better systems.
With this approach:
- Applications are built within a shared environment
- Data remains consistent across operations
- Workflows operate without heavy integration dependencies
- Systems scale without increasing complexity
This aligns with how enterprise software is evolving in 2026.
Automation as a Native Capability
Automation is no longer optional.
But how it is implemented matters.
In fragmented systems:
- Automation relies on multiple tools
- Workflows depend on integrations
- Delays are common
In a unified platform:
- Automation is built into the system
- Processes run in real time
- Workflows are more reliable
A low code application development platform should treat automation as a core capability not an add-on.
The Future of Enterprise Software
The direction is clear.
Enterprises are moving away from:
- Disconnected SaaS tools
- Heavy integration layers
- Complex system architectures
And toward:
- Unified platforms
- Real-time operations
- Simplified system design
Low code is playing a central role in this transition.
Not because it replaces development.
But because it changes how systems are built.
Final Thoughts
The best low code development platforms in 2026 are not defined by how quickly you can build applications.
They are defined by how well they support long-term system stability.
Enterprises need platforms that:
- Reduce complexity
- Maintain data consistency
- Support scalability
- Enable efficient workflows
A low code application development platform that delivers on these areas becomes more than a tool.
It becomes the foundation of enterprise systems.
If you’re evaluating low code platforms for your enterprise, it’s worth exploring how a unified approach can simplify your systems.
Book a demo to see how Airtool helps you build scalable, connected, and efficient enterprise applications without fragmentation.
Digital Development
Best Payment Reconciliation Software for Enterprises 2026

As digital transactions grow in volume and complexity, enterprises face increasing pressure to maintain accurate financial records. Payments flow through multiple channels—gateways, banks, wallets, and billing systems—making manual tracking nearly impossible. This is where payment reconciliation software becomes a critical part of modern finance operations.
It enables businesses to automate transaction matching, reduce errors, and gain real-time visibility into their financial data.
Why Enterprises Need Payment Reconciliation Software
Large organizations handle thousands or even millions of transactions daily. Without automation, reconciliation becomes slow, error-prone, and difficult to scale.
Here’s why enterprises are adopting advanced solutions:
- Manual reconciliation cannot handle high transaction volumes
- Multiple payment sources create data fragmentation
- Delays in reconciliation affect financial reporting
- Errors increase operational risk and compliance issues
Modern tools solve these challenges by bringing speed, accuracy, and control into the reconciliation process.

What Makes Enterprise Reconciliation Complex
Enterprise-level reconciliation is not just about matching transactions. It involves:
- Multi-channel payments (cards, UPI, wallets, bank transfers)
- Cross-border transactions and currency conversions
- High volumes of refunds and chargebacks
- Integration with ERP and billing systems
This complexity is why businesses are actively searching for the top payment reconciliation platforms for enterprises that can handle large-scale operations efficiently.
Key Features of Enterprise Payment Reconciliation Software
The best solutions are designed to handle scale and complexity with ease. Here are the features that define the best enterprise payment reconciliation software:
1. Automated Matching
Advanced rule-based and AI-driven matching ensures faster and more accurate reconciliation.
2. Real-Time Data Processing
Enterprises need instant visibility into transactions to make timely decisions.
3. Multi-System Integration
Seamless integration with payment gateways, banks, and internal systems is essential.
4. Exception Handling
Unmatched transactions are flagged automatically for quick resolution.
5. Audit Trails and Compliance
Detailed logs help maintain transparency and simplify audits.
How Enterprises Handle Reconciliation at Scale
A common question many finance leaders ask is: how do enterprise platforms handle payout reconciliation at scale?
The answer lies in automation and intelligent workflows.
Modern systems:
- Process bulk transactions in seconds
- Use AI to improve matching accuracy over time
- Apply dynamic rules for complex scenarios
- Provide centralized dashboards for monitoring
This allows finance teams to focus on analysis rather than manual data entry.
Comparing the Best Enterprise Payment Reconciliation Software
When evaluating tools, businesses often look for a clear best enterprise payment reconciliation software comparison.
Here are some key factors to consider:
Scalability
Can the system handle increasing transaction volumes without performance issues?
Flexibility
Does it support custom workflows and reconciliation rules?
Integration
Can it connect with existing financial and operational systems?
Reporting
Does it offer actionable insights and detailed reports?
Security
Is sensitive financial data protected with robust security measures?
Solutions that excel in these areas are often recognized as the best payment reconciliation platforms for businesses.
Benefits of Using Payment Reconciliation Software
Adopting enterprise-grade tools delivers measurable benefits:
Faster Financial Close
Automation reduces reconciliation time from days to hours.
Improved Accuracy
Minimizes human errors and ensures consistent data.
Better Cash Flow Visibility
Real-time insights help track incoming and outgoing funds.
Reduced Operational Costs
Less manual work means lower labor costs.
Enhanced Decision-Making
Data-driven insights support strategic planning.
Role of Billing Systems in Reducing Errors
Reconciliation doesn’t work in isolation. It is closely linked with billing systems.
Modern billing systems that reduce reconciliation errors and delays ensure that:
- Transaction data is accurate from the source
- Invoices align with payments
- Discrepancies are minimized early
When billing and reconciliation systems work together, businesses achieve greater efficiency and accuracy.
Top Payment Reconciliation Tools for Large Businesses
Enterprises often evaluate multiple vendors before choosing a solution. The top payment reconciliation tools for large businesses typically offer:
- Cloud-based architecture for scalability
- AI-powered matching engines
- Real-time dashboards and analytics
- Customizable workflows
- Strong compliance and security features
Reading enterprise payment reconciliation software reviews can also provide insights into real-world performance and user experience.
Trends Shaping Payment Reconciliation in 2026
As we move forward, technology continues to transform financial operations. The best enterprise payment reconciliation software 2026 will be defined by:
AI and Machine Learning
Systems will become smarter and more predictive.
Real-Time Reconciliation
Instant transaction matching will become the standard.
Cloud-Native Platforms
Flexible and scalable solutions will dominate the market.
End-to-End Automation
Minimal human intervention with maximum efficiency.
Businesses that adopt these innovations early will gain a competitive advantage.
Choosing the Right Solution for Your Business
- Assess current pain points and requirements
- Evaluate multiple vendors and solutions
- Consider long-term scalability
- Prioritize ease of integration
- Ensure strong support and training
A well-chosen solution not only improves efficiency but also strengthens overall financial management.
Conclusion
In an increasingly complex payment landscape, enterprises cannot rely on manual processes or outdated systems. Payment reconciliation software has become essential for ensuring accuracy, efficiency, and scalability.
From automating transaction matching to providing real-time insights, these tools empower businesses to take control of their financial operations. As technology continues to evolve, adopting the right solution will be key to staying competitive.
To streamline your reconciliation workflows and improve financial accuracy, explore advanced solutions from Optimus Fintech. Their platform is designed to handle enterprise-scale reconciliation with automation, intelligence, and precision.
Development
KAT6B, MAFB, MAT2A: Precision Trio Transforming Cancer
In the high-speed world of modern molecular biology, we are moving past the simple era of just identifying genetic mutations. Scientists are no longer satisfied with knowing a gene is “broken.” Instead, the focus has shifted toward the complex interplay between epigenetics—the system that turns genes on or off—and metabolic reprogramming, which is how cancer cells fuel their relentless growth. At the center of this scientific revolution are three specific genes: KAT6B, MAFB, and MAT2A. These three players are rapidly becoming known as the “Precision Trio” of oncology and developmental biology.
By understanding how these genes interact, researchers are finding new ways to dismantle tumors from the inside out. They are moving away from broad, toxic treatments and toward therapies that target the very logic of a cancer cell.
KAT6B: The Master Architect of Chromatin
Think of KAT6B (Lysine Acetyltransferase 6B) as the master architect of your cellular blueprint. It doesn’t just hold information; it actively manages it. KAT6B functions as a histone acetyltransferase. This means it adds chemical “tags” to the proteins (histones) around which our DNA is tightly wrapped.
When KAT6B adds these tags, it causes the DNA to relax, making certain genes accessible for the cell to read. If KAT6B is working correctly, your body develops and functions normally. However, if this architect makes a mistake, the results are often catastrophic.
The Link to Cancer and Development
Historically, doctors associated KAT6B mostly with rare developmental disorders that affect the skeleton and brain. However, in 2026, it has become a major target in cancer research. Disruptions in KAT6B are frequently found in Acute Myeloid Leukemia (AML) and several types of solid tumors. When the architect fails, the cell loses its structural and genetic identity. This failure leads to the chaotic, uncontrolled cell division that we define as cancer. By targeting KAT6B, scientists hope to “re-structure” the cell and restore its original, healthy blueprints.
MAFB: The Foreman of Cellular Identity
If KAT6B is the architect, MAFB (MAF BZIP Transcription Factor B) is the foreman on the construction site. While the architect draws the plans, the foreman ensures the workers become what they are supposed to be. MAFB is a transcription factor, a protein that tells a cell its specific identity. It is particularly vital in the development of blood cells and the creation of macrophages, which are the “vacuum cleaners” of the immune system.
A Double-Edged Sword in Oncology
In the medical world, MAFB is a complex character. On one hand, we need it for a healthy immune system. On the other hand, when MAFB is overexpressed—meaning there is too much of it—it becomes a hallmark of multiple myeloma and other blood cancers.
Researchers are now exploring “differentiation therapy” using MAFB. Instead of trying to kill the cancer cells with poison, they are trying to use MAFB to “order” the cancer cells to grow up. If a cancer cell can be forced to mature into a functional, harmless white blood cell, it stops dividing. This approach represents a shift from destroying cells to re-programming them back into a state of health.
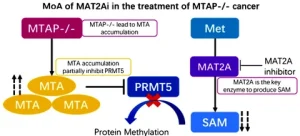
MAT2A: The Powerhouse Supplier of Methylation
The third member of the trio is MAT2A (Methionine Adenosyltransferase 2A). This gene is the critical bridge between what a cell “eats” and how its genes “behave.” MAT2A is responsible for producing S-adenosylmethionine (SAM). SAM is the universal donor for a process called methylation.
Methylation is essentially a “silencing” mechanism. When a methyl group is added to DNA, it usually turns a gene off. For a cancer cell to stay aggressive and immortal, it needs a constant, high-volume supply of SAM. Because of this, many cancer cells become “addicted” to MAT2A.
The Strategy of Synthetic Lethality
One of the biggest breakthroughs in 2026 involves a concept called synthetic lethality. Scientists have discovered that certain tumors (specifically those lacking the MTAP gene) are extremely vulnerable if MAT2A is blocked. By inhibiting MAT2A, we can effectively starve the cancer of the chemical tools it needs to keep its “off-switches” working. Without MAT2A, the cancer cell’s epigenetic logic collapses, leading to cell death while leaving healthy cells relatively unharmed.
The Synergetic Future: A Three-Pronged Attack
The real power of the Precision Trio lies in their synergy. We are no longer looking at acetylation (KAT6B), transcription control (MAFB), and methylation metabolism (MAT2A) as isolated events. Instead, we see them as a single, integrated machinery that drives malignancy.
Why This Matters for Precision Medicine
In the past, doctors treated cancer based on where it was found in the body—lung cancer, breast cancer, or bone cancer. Today, we treat cancer based on its genetic logic.
-
The Architect (KAT6B): Controlling access to the DNA.
-
The Foreman (MAFB): Controlling the cell’s identity.
-
The Supplier (MAT2A): Providing the raw materials for gene silencing.
Pharmaceutical companies are currently developing small-molecule inhibitors that target these three proteins. By attacking the architect, the foreman, and the supplier at the same time, we can dismantle the tumor’s infrastructure. This multi-pronged attack makes it much harder for cancer to develop resistance to treatment.
Improving Readability and Research Access
For scientists in the lab, time is the most valuable resource. To push these discoveries from the bench to the clinic, researchers need high-affinity antibodies and highly specific inhibitors. Fortunately, advanced digital tools now allow scientists to search for these specific gene symbols and immediately access the reagents they need. This digital integration is accelerating the pace of discovery, ensuring that the “Precision Trio” moves into human clinical trials faster than any previous generation of cancer drugs.
Conclusion: A New Era of Hope
The study of KAT6B, MAFB, and MAT2A is a testament to the incredible progress we have made in decoding the human genome. We are finally moving away from the “carpet bombing” approach of traditional chemotherapy. Instead, we are using “surgical strikes” against the proteins that define the cancer’s existence.
As we continue to refine these targeted therapies, the dream of a less toxic, more effective cancer treatment is becoming a reality. By leveraging the combined power of epigenetics and metabolism, we are not just fighting cancer; we are outsmarting it. The Precision Trio is leading the way toward a future where a cancer diagnosis is no longer a sentence, but a solvable genetic puzzle.
-
Business3 years ago
Cybersecurity Consulting Company SequelNet Provides Critical IT Support Services to Medical Billing Firm, Medical Optimum
-
Business3 years ago
Team Communication Software Transforms Operations at Finance Innovate
-
Business3 years ago
Project Management Tool Transforms Long Island Business
-
Business3 years ago
How Alleviate Poverty Utilized IPPBX’s All-in-One Solution to Transform Lives in New York City
-
health3 years ago
Breast Cancer: The Imperative Role of Mammograms in Screening and Early Detection
-
Sports3 years ago
Unstoppable Collaboration: D.C.’s Citi Open and Silicon Valley Classic Unite to Propel Women’s Tennis to New Heights
-
Art /Entertainment3 years ago
Embracing Renewal: Sizdabedar Celebrations Unite Iranians in New York’s Eisenhower Park
-
Finance3 years ago
The Benefits of Starting a Side Hustle for Financial Freedom