Technology
The Truth is Out There: How to Navigate the Internet’s Misinformation Maze

The Truth is Out There: How to Navigate the Internet’s Misinformation Maze
The internet is a vast and wonderful source of information, entertainment, and communication. But it is also a place where misinformation, deception, and manipulation can thrive. How can you tell the difference between reliable and unreliable information online? How can you avoid falling prey to false or misleading claims, rumors, or propaganda? How can you protect yourself and others from the harmful effects of misinformation?
In this article, I will share some tips and strategies on how to evaluate online sources and navigate the internet’s misinformation maze. I will also provide some examples of common types of misinformation and how to spot them. By the end of this article, you will have a better understanding of how to use the internet wisely and responsibly, and how to find the truth that is out there.
What is misinformation and why does it matter?
Misinformation is generally defined as information that is false, inaccurate, or misleading, but not necessarily created or shared with the intention to cause harm. Sometimes, misinformation is the result of honest mistakes, poor research, or outdated information. Other times, misinformation is deliberately created or spread by people or groups who have ulterior motives, such as political agendas, financial gains, or personal grudges.
Misinformation can have serious consequences for individuals and society. It can erode trust in institutions, authorities, and experts. It can influence people’s opinions, beliefs, and behaviors. It can affect people’s health, safety, and well-being. It can also fuel conflicts, divisions, and violence.
For example, misinformation about the COVID-19 pandemic has led to confusion, fear, and complacency among the public, undermining the efforts to contain the virus and save lives. Misinformation about the 2020 U.S. presidential election has contributed to political polarization, social unrest, and violence, threatening the stability and legitimacy of democracy. Misinformation about climate change has delayed the action and cooperation needed to address the global environmental crisis.
Therefore, it is important to be aware of the prevalence and impact of misinformation online, and to develop the skills and habits to identify and counter it.
How to evaluate online sources
One of the key skills to combat misinformation online is to evaluate the sources of information you encounter. A source is anything that provides information, such as a website, a book, a video, a podcast, or a person. Not all sources are equally reliable, credible, or trustworthy. Some sources may have more authority, accuracy, objectivity, currency, coverage, and appearance than others.
To evaluate online sources, you can use the following criteria and questions:
- Authority: Who is the author or creator of the information? What are their credentials, qualifications, or expertise on the topic? Are they affiliated with a reputable institution or organization? How can you contact them or verify their identity?
- Accuracy: Is the information factual, correct, and supported by evidence? Are the sources of the information cited or linked? Can you confirm the information from other sources? Are there any errors, inconsistencies, or contradictions in the information?
- Objectivity: What is the purpose or goal of the information? Is the information presented fairly, impartially, and without bias? Is the information based on facts, opinions, or emotions? Are there any hidden agendas, conflicts of interest, or ulterior motives behind the information?
- Currency: When was the information created, updated, or revised? Is the information current, relevant, and timely for your needs? Does the information reflect the latest developments, research, or data on the topic?
- Coverage: How much and how well does the information cover the topic? Is the information comprehensive, detailed, and in-depth, or superficial, vague, and incomplete? Is the information consistent, coherent, and logical, or contradictory, confusing, and flawed?
- Appearance: How does the information look and sound? Is the information well-written, well-organized, and well-designed, or poorly-written, poorly-organized, and poorly-designed? Is the information clear, concise, and readable, or unclear, wordy, and unreadable? Is the information professional, polished, and appealing, or amateur, sloppy, and unappealing?
You can use these criteria and questions as a checklist to evaluate any online source you encounter. The more questions you can answer positively, the more likely the source is reliable and credible. However, keep in mind that these criteria and questions are not absolute or definitive. Sometimes, a source may meet some criteria but not others, or may have some strengths and some weaknesses. Therefore, you should always use your own judgment and critical thinking to assess the quality and value of a source.
How to spot common types of misinformation
Another skill to combat misinformation online is to spot the common types of misinformation that circulate on the internet. Some of the most prevalent and problematic types of misinformation are:
- Fake news: Fake news is information that is deliberately fabricated or distorted to mislead the public, usually for political or financial purposes. Fake news often mimics the style and format of legitimate news outlets, but lacks the standards and ethics of journalism. Fake news can be found on websites, social media platforms, or apps that are designed to look like credible sources, but are actually run by malicious actors or groups. Fake news can also be spread by bots, trolls, or influencers who have large online followings or networks.
- Satire and parody: Satire and parody are forms of humor that use exaggeration, irony, or ridicule to mock or criticize a person, group, or issue. Satire and parody can be found on websites, social media platforms, or apps that are dedicated to producing humorous content, such as The Onion, The Babylon Bee, or The Borowitz Report. Satire and parody can also be found on TV shows, podcasts, or videos that feature comedians, actors, or celebrities who impersonate or imitate real people or events, such as Saturday Night Live, The Daily Show, or The Late Show. Satire and parody are not meant to be taken seriously or literally, but sometimes they can be mistaken for or misused as real news or information.
- Hoaxes and scams: Hoaxes and scams are information that is intentionally false or deceptive to trick or harm the public, usually for personal gain or amusement. Hoaxes and scams can be found on websites, social media platforms, or apps that are created or used by individuals or groups who want to exploit the public’s curiosity, fear, or greed. Hoaxes and scams can also be spread by email, text, or phone calls that are sent or made by individuals or groups who want to obtain the public’s personal or financial information. Hoaxes and scams often involve sensational or sensationalized stories, claims, or offers that are too good or too bad to be true.
- Rumors and gossip: Rumors and gossip are information that is unverified, unsubstantiated, or speculative, usually about a person, group, or issue. Rumors and gossip can be found on websites, social media platforms, or apps that are focused on entertainment, celebrity, or lifestyle topics, such as TMZ, Perez Hilton, or BuzzFeed. Rumors and gossip can also be spread by word-of-mouth, online or offline, by individuals or groups who want to share or comment on the latest news or trends. Rumors and gossip may or may not be true, but they are often based on hearsay, speculation, or opinion, rather than facts, evidence, or verification.
To spot these common types of misinformation, you can use the following tips and strategies:
- Check the source: Look at the website, social media platform, or app where the information is published or shared. What is the name, domain, or URL of the source? Who is the author, creator, or owner of the source? What is the reputation, credibility, or agenda of the source? Is the source known for producing or spreading misinformation, or for being satirical, humorous, or sensational?
- Check the content: Look at the information itself. What is the headline, title, or caption of the information? What is the tone, style, or format of the information? What is the message, claim, or argument of the information? Is the information factual, logical, and consistent, or false, illogical, and contradictory? Is the information supported by evidence, sources, or links, or by emotions, opinions, or anecdotes?
- Check the context: Look at the background and surrounding of the information. When and where was the information created, published, or shared? Why and how was the information created, published, or shared? Who is the intended or actual audience of the information? What is the purpose or goal of the information? Is the information relevant, appropriate, and timely, or irrelevant, inappropriate, and outdated?
- Check the verification: Look at the confirmation or refutation of the information. What do other sources say about the information? What do experts, authorities, or fact-checkers say about the information? What do your own knowledge, experience, or common sense say about the information? Is the information verified, corroborated, or agreed upon, or disputed, debunked, or challenged?
You can use these tips and strategies as a guide to spot the common types of misinformation online. However, keep in mind that these tips and strategies are not foolproof or exhaustive. Sometimes, misinformation can be subtle, sophisticated, or convincing, or can mix some truth with some falsehood. Therefore, you should always be alert, curious, and skeptical when encountering information online.
Image by rawpixel.com on Freepik
Conclusion
The internet is a powerful and valuable tool for learning, communicating, and creating. But it is also a place where misinformation can flourish and harm. Therefore, it is important to be aware of the prevalence and impact of misinformation online, and to develop the skills and habits to identify and counter it.
In this article, I have shared some tips and strategies on how to evaluate online sources and spot common types of misinformation. I hope you have found this article helpful and informative. Here is a summary table of the main points discussed:
| Criteria for evaluating online sources | Tips for spotting common types of misinformation |
|---|---|
| Authority: Who is the author or creator of the information? | Check the source: What is the name, domain, or URL of the source? |
| Accuracy: Is the information factual, correct, and supported by evidence? | Check the content: What is the headline, title, or caption of the information? |
| Objectivity: What is the purpose or goal of the information? | Check the context: When and where was the information created, published, or shared? |
| Currency: When was the information created, updated, or revised? | Check the verification: What do other sources say about the information? |
| Coverage: How much and how well does the information cover the topic? | |
| Appearance: How does the information look and sound? |
Remember, the truth is out there, but you have to look for it carefully and critically. Don’t believe everything you see or hear online. Do your own research, check your facts, and verify your sources. Be a smart and responsible internet user, and help others do the same. Together, we can make the internet a better and safer place for everyone.
Thank you for reading this article. I hope you enjoyed it and learned something new. If you have any questions, comments, or feedback, please feel free to share them with me. I would love to hear from you. Have a great day!
Digital Development
AI in Medical Imaging Market Growth, Trends & Forecast 2030

Artificial Intelligence is rapidly shifting the paradigm of modern healthcare operations. Today, medical institutions frequently leverage sophisticated machine learning tools to overcome diagnostic bottlenecks and enhance patient outcomes. Healthcare teams use these systems to process complex image patterns with incredible accuracy and speed. This ongoing technological integration creates a dynamic corporate environment for global investors.
Furthermore, clinical settings face an increasing demand for precision medicine. Medical professionals must continually find innovative ways to capture subtle cellular anomalies. Traditional manual scanning routines can introduce human error or result in delayed interventions. To mitigate this risk, the global medical community is turning directly to computerized deep learning software. These modern algorithms excel at identifying spatial and temporal variations that are often invisible to the human eye. Consequently, early disease detection is transforming from a challenging clinical objective into a manageable daily routine.
Market Projections and Financial Milestones
The financial trajectory of this industry highlights an era of massive technological expansion. Comprehensive data verified by industry experts shows that the sector is growing at a rapid pace. For instance, the global AI in medical imaging market achieved a notable valuation of USD 1.75 billion in 2024. Backed by rapid clinical automation and active product launches, the current market size has quickly scaled to USD 8.56 billion as the sector moves steadily toward its 2030 targets.
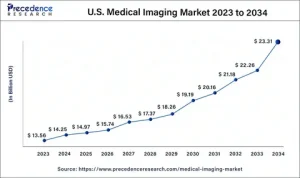
This upward trajectory reflects a remarkable compound annual growth rate (CAGR) of 30% during the observed forecast window. This steady financial performance relies entirely on documented usage trends and actual product adoption rates. It purposefully avoids speculative interpretations or unverified industry claims. Furthermore, experts predict that this rapid integration will speed up radiology data interpretation by up to 20%. This efficiency gain concurrently reduces false positive rates by approximately 10%. As a result, hospitals can optimize their workflow efficiency while cutting down on long-term administrative costs.
Strategic Driving Forces and Industry Innovations
Several core technical factors are currently accelerating this global marketplace. First, research and development teams are actively introducing context-aware neural networks. These advanced tools analyze scans at a highly granular sentence and pixel level. Second, innovative formulation and delivery methods are making software deployment seamless for busy hospital networks. Cloud-based applications allow clinicians to access cloud diagnostics from remote locations instantly.
Third, strategic marketing and distribution networks are expanding product accessibility worldwide. Top-tier medical providers frequently team up with artificial intelligence developers to build comprehensive software suites. These collaborative agreements ensure that advanced medical processing remains financially viable for smaller local diagnostic clinics.
Finally, manufacturers are carefully evaluating their internal pricing models and cost structures. Subscription-based software models are replacing traditional, high-cost upfront licensing agreements. This deliberate commercial pivot allows medium-sized healthcare facilities to manage their capital expenditures smoothly. By minimizing upfront technology costs, software providers can scale their installations across underserved international medical markets.
Comprehensive Market Scope and Segmentation
The overall structural framework of this industry relies on a clear, multi-layered segmentation model. Evaluating the industry through distinct sub-segments allows stakeholders to identify unique commercial opportunities.
By Application Area
The market is divided into several clinical specialties that require specialized pattern recognition. Neurology and oncology represent two of the largest application areas due to the high complexity of brain and tumor scans. Cardiology operations also deploy automated software to monitor blood flow characteristics and identify early cardiac blockages. Additionally, pulmonology and musculoskeletal departments are integrating automated triage tools to manage high patient volumes in emergency care environments.
By Type of Image Processed
Modern deep learning systems are versatile enough to handle a diverse array of medical formats. Standard X-rays and computed tomography (CT) scans dominate the processed volume share because of their widespread use in initial triage. Magnetic resonance imaging (MRI) analysis is expanding fast as algorithms become better at reading complex soft-tissue contrasts. Furthermore, ultrasound and mammography imaging are experiencing high adoption rates among specialized women’s health networks.
By End User and Distribution Channels
Hospitals and large diagnostic imaging centers remain the primary consumers of these diagnostic software packages. However, independent research laboratories and ambulatory surgical centers are emerging as valuable niche buyers. These facilities utilize automated software to expedite clinical trials and lower active patient wait times.
Regional Performance and Market Variations
The operational demand and structural adoption of automated medical diagnostics vary widely across different geographic boundaries. Each territory exhibits distinct regulatory landscapes and healthcare investment patterns.
North America currently maintains the dominant global share in terms of revenue and infrastructure readiness. Strong consumer awareness of advanced diagnostics combines with substantial venture capital funding to accelerate local software installation. Widespread integration of electronic health records simplifies the initial training phase for deep learning algorithms.
Meanwhile, Europe is experiencing steady, structured growth across its regional healthcare markets. This stable expansion stems primarily from progressive government-led healthcare campaigns. These state initiatives actively promote digital transformation and subsidize advanced technological integration in public hospitals. European researchers focus intensely on developing highly transparent systems to comply with strict regional data protection laws.
The Asia-Pacific region represents the fastest-growing geographical market in the world. Rapidly expanding middle-class populations are becoming highly health-conscious. Consequently, regional hospital networks are demanding efficient diagnostic tools to handle massive daily patient volumes. Domestic technology firms in Japan, China, and India are scaling up production to supply local clinics while also pursuing international export opportunities.
Finally, South America and the Middle East are developing into lucrative niche markets. These regions focus heavily on integrating artificial intelligence into mobile telemedicine platforms to bridge accessibility gaps in remote communities.
Competitive Landscape and Industry Leaders
The global marketplace features a highly competitive blend of established medical conglomerates and agile technology startups. These organizations rely on constant product optimization and strategic intellectual property accumulation to secure a definitive market edge.
Prominent organizations driving structural innovation include:
-
Artelus
-
Arterys
-
Butterfly Network
-
ContextVision
-
Enlitic
-
Echonous
-
GE Healthcare
-
InferVision
-
VUNO
These companies continually invest in high-level research and development to expand their product portfolios. They pursue strategic corporate acquisitions to enter fresh regional territories quickly. They also enter multi-year partnerships with leading universities to secure access to diverse, high-quality medical datasets. These comprehensive data networks allow engineers to eliminate algorithmic biases, ensuring that software outputs remain reliable across varied patient demographics.
Strategic Consulting and Data Resources
Navigating this fast-paced digital marketplace requires access to reliable, data-driven intelligence. Roots Analysis provides senior executives and institutional investors with comprehensive market studies. For over a decade, this global research and consulting powerhouse has supported more than 750 international clients. Their diverse client base spans Fortune 500 corporations, innovative healthcare startups, and strategic venture capital funds.
The firm offers bespoke consulting services that are carefully tailored to unique client objectives. Their experienced research team specializes in structured market assessments, competitive benchmarking, and regulatory intelligence tracking. These verified insights enable corporate leaders to fine-tune their product launch strategies and identify profitable investment hotspots.
Furthermore, the firm provides flexible subscription services that grant organizations seamless access to a vast library of healthcare market reports. Subscribers enjoy on-demand analyst support and customized data packs available in both PDF and spreadsheet formats. This empirical foundation ensures that modern decision-makers can confidently navigate complex regulatory landscapes and make stress-free, highly informed commercial decisions.
Digital Development
AI Viết Tiểu Luận: Humanizing AI Essays for Academic Success

Artificial Intelligence tools are rapidly shifting the paradigm of modern education. Today, students frequently leverage AI to overcome writer’s block, brainstorm complex topics, map out detailed outlines, and construct full AI essay writing drafts. While these platforms drastically reduce the hours spent on early drafting, reliance on raw machine outputs introduces a distinct operational flaw: AI-generated text often sounds highly mechanical, relies on predictable vocabulary, and fundamentally lacks the nuanced, authoritative tone required in scholarly spaces.
To mitigate this, the process of ai viết tiểu luận (AI essay writing) must be intentionally paired with human refinement. Humanizing AI content ensures that academic submissions are not merely structured, but read naturally, exhibit critical analysis, and strictly align with institutional standards. Recognizing this shift, advanced platforms like CudekAI provide sophisticated, dual-purpose tools—specifically, an AI humanizer and an AI detector—engineered to simplify digital workflows and elevate machine drafts into professional, human-grade scholarship.
What Is AI Essay Writing?
AI essay writing involves utilizing algorithmic generative text models to produce academic outputs like research papers, standard essays, and lab reports. While these tools excel at compiling disparate facts and spitting out clean structures at a glance, they struggle to replicate an authentic human voice or inject original interpretive thought.
When implemented with proper guardrails, executing an ai viết tiểu luận strategy allows users to:
-
Save significant time during the initial literature review and rough drafting stages.
-
Automatically generate logically organized, well-structured outlines.
-
Boost overall writing productivity and clear formatting hurdles quickly.
-
Refine unorganized thoughts into cohesive, highly polished arguments.
-
Maintain a consistently formal and clear academic voice across long-form text.
Ultimately, the humanization phase acts as the essential bridge, transforming raw algorithmic data into an essay that is both engaging for readers and appropriate for academic submission.
How CudekAI Optimizes Academic Content Creation
CudekAI serves as an end-to-end linguistic hub that converts rigid, machine-generated drafts into fluid, natural writing. Rather than forcing students to manually rephrase repetitive passive sentences or look up discipline-specific synonyms, the platform automates the initial structural overhaul. By analyzing contextual flow, sentence length variation, and phrasing, CudekAI polishes text until it mimics the distinct rhythm of human authorship.
The ecosystem balances two critical academic needs:
-
Refinement: It offers an advanced Humanize AI engine that rewrites robotic phrasing while strictly preserving the author’s original data, citations, and core thesis.
-
Integrity: It features a highly precise AI Detector that scans text for structural uniformities common to models like ChatGPT, Claude, or Gemini. This allows students and educators to verify original expression and safeguard academic integrity prior to final submission.
Key Technical Features of the Platform
CudekAI stands out through a robust suite of tools explicitly tailored to academic and professional writing environments:
-
Context-Aware AI Humanization: Instead of executing simple word-for-word synonym swapping, the platform restructures sentences, varies syntax patterns, and introduces natural transitions that flow logically from paragraph to paragraph.
-
Deep Pattern AI Detection: Utilizes Natural Language Processing (NLP) to break down text at a sentence level, providing an AI-vs-human score so users can see exactly which passages require human styling.
-
Integrated Plagiarism Prevention: Cross-references content against extensive digital databases and academic repositories to guarantee that the final generated paper is 100% unique.
-
Advanced Rewriting & Paraphrasing: Helps users reword dense, highly technical jargon into simple, concise, and highly readable explanations without diluting the core message.
-
Comprehensive Multilingual Support: Features robust native processing for over 100 languages, seamlessly handling nuances, regional idioms, and stylistic traditions in both Vietnamese (ai viết tiểu luận) and English academic contexts.
Diverse Target Users
The platform’s versatility makes it highly valuable to a broad range of individuals across the educational landscape:
| User Category | Core Application |
| Students | Transforming fast AI drafts into natural, polished essays and homework assignments that bypass rigid institutional detection software. |
| Educators & Teachers | Evaluating student submissions for AI plagiarism while quickly refining lesson plans, grading notes, and clear personal feedback. |
| Academic Researchers | Polishing multi-page empirical reports, formatting documentation, and simplifying complex, technical arguments for international publication. |
| Educational Content Writers | Drafting localized, high-volume educational materials, blogs, and curriculum guides that read authentically and rank effectively on search engines. |
Balancing Technical Efficiency and Ethical Integrity
The rise of generative AI has forced educational institutions to enforce much stricter detection criteria. Submitting unedited, raw machine writing can severely compromise a student’s academic standing. Humanizing your digital workflow with CudekAI offers a clear advantage: it reduces the structural signals that trigger algorithmic flags while simultaneously elevating the overall readability and persuasive tone of the paper. This allows students to responsibly use AI as an intellectual assistant—speeding up deep research and structural organization—while maintaining the unique voice, critical perspective, and ethical transparency necessary for true academic success.
Summary
While AI essay writing tools offer unparalleled speed and structural utility, the human element remains completely non-negotiable for high-tier academic achievements. CudekAI equips modern scholars with the exact toolkit required to balance these two worlds. By pairing smart humanization algorithms with precise detection systems, the platform empowers users to turn rigid, machine-coded prose into fluid, natural, and highly credible writing. Adopting these advanced workflows ensures your essays remain academically sound, secure, and compelling from introduction to conclusion.
Autos & Vehicles
Swaraj Tractor Price Guide: Top 5 Mid-Range Models for Farmers

Indian agriculture demands reliable machinery that can withstand unpredictable weather, varying soil textures, and intense, continuous operational hours. Swaraj tractors have carved out an enduring reputation among farmers nationwide due to their robust mechanical efficiency, structural durability, and high performance. The manufacturer provides tailored mid-range options designed to blend modern technology with cost-effective upkeep.
For farmers seeking a multi-use vehicle that balances high torque output with optimized fuel economy, selecting a mid-range tractor is a highly critical decision. Navigating the diverse options in the market requires a clear look at true technical capabilities. Below is an updated, comprehensive guide breaking down the technical specifications, performance attributes, and realistic price expectations for the top five mid-range Swaraj tractors.
Technical Analysis of the Top 5 Mid-Range Swaraj Tractors
1. Swaraj 744 XT
The Swaraj 744 XT functions as a versatile, multi-application workhorse designed for medium-scale operations. It handles intensive implement attachments easily, making it highly effective for plowing, rotary tilling, multi-crop sowing, and heavy-duty transport hauling across variable soil matrices.
-
Engine Output: 50 HP Category
-
Cylinder Configuration: 3 Cylinders
-
Hydraulic Lift Capacity: 1,700 kg
-
Braking System: Oil-Immersed Brakes
-
Steering Mechanism: Power Steering
-
Transmission Layout: 8 Forward + 2 Reverse Gears
-
Estimated Price Range: ₹6.95 Lakh – ₹7.47 Lakh (Ex-Showroom)
Core Advantage: This model features high displacement and optimized backup torque, allowing the machine to work continuously under sudden load variations without stalling or excessive fuel waste.
2. Swaraj 735 FE
As one of the longest-standing and most widely trusted models in the Indian agricultural sector, the Swaraj 735 FE balances simplicity with absolute reliability. It is engineered primarily for small to medium holdings where low operation costs and straightforward mechanical maintenance are top priorities.
-
Engine Output: 40 HP Category
-
Cylinder Configuration: 3 Cylinders
-
Hydraulic Lift Capacity: 1,000 kg
-
Braking System: Dry Disc Brakes
-
Steering Mechanism: Mechanical (Optional Power Steering available)
-
Transmission Layout: 8 Forward + 2 Reverse Gears
-
Estimated Price Range: ₹5.83 Lakh – ₹6.18 Lakh (Ex-Showroom)
Core Advantage: The 735 FE requires significantly less maintenance downtime and features highly economical fuel consumption profiles during routine tilling, threshing, and water-pumping operations.

3. Swaraj 742 XT
The Swaraj 742 XT introduces an advanced balance of operator ergonomics and technical performance. This modern mid-range model is specifically tuned for precision multi-crop farming, where smooth handling reduces operator fatigue over extended working periods.
-
Engine Output: 45 HP Category
-
Cylinder Configuration: 3 Cylinders (3307 CC Displacement)
-
Hydraulic Lift Capacity: 1,700 kg
-
Braking System: Oil-Immersed Brakes
-
Steering Mechanism: Power Steering
-
Fuel Tank Volume: 56 Liters
-
Estimated Price Range: ₹6.38 Lakh – ₹6.73 Lakh (Ex-Showroom)
Core Advantage: Built with a partial constant mesh transmission, dual-clutch options, and a multi-speed forward and reverse PTO system, it provides exceptional compatibility with modern rotavators and harvesters.
4. Swaraj 744 FE
A staple in the mid-range category, the Swaraj 744 FE is globally recognized for its incredible versatility and adaptability across different climatic conditions. It handles heavy soil implements without breaking a sweat, presenting an outstanding value-for-money investment.
-
Engine Output: 45 to 48 HP Range
-
Cylinder Configuration: 3 Cylinders (3136 CC Displacement)
-
Hydraulic Lift Capacity: 1,700 kg
-
Braking System: Oil-Immersed Brakes
-
Transmission Layout: Constant Mesh
-
Steering Mechanism: Manual / Power Steering Options
-
Estimated Price Range: ₹6.88 Lakh – ₹7.37 Lakh (Ex-Showroom)
Core Advantage: The structural design utilizes an adjustable front axle and automatic depth and draft control (ADDC) hydraulics, which significantly simplifies complex field maneuvers and row crop farming.
5. Swaraj 855 FE
Sitting at the upper limit of the mid-range classification, the Swaraj 855 FE provides the heavy-duty muscle required for intense commercial farming, deep plowing, and long-distance commercial haulage over rough, unpaved terrains.
-
Engine Output: 49.3 to 52 HP Category
-
Cylinder Configuration: 3 Cylinders (3308 CC Displacement)
-
Hydraulic Lift Capacity: 1,700 kg
-
Braking System: Oil-Immersed Brakes
-
Steering Mechanism: Power Steering
-
PTO Configuration: Multi-Speed PTO System
-
Estimated Price Range: ₹7.87 Lakh – ₹8.37 Lakh (Ex-Showroom)
Core Advantage: The high ground clearance combined with superior engine torque parameters ensures that this model can pull heavy, loaded trolleys and run large agricultural implements with minimal operational downtime.
Strategic Advantages of Mid-Range Swaraj Tractors
When assessing the long-term viability of an agricultural machinery investment, looking beyond the initial sticker price is critical. Mid-range Swaraj models deliver distinct operational benefits:
| Strategic Pillar | Direct Operational Benefit for the Farmer |
| Rugged Architectural Design | Heavy cast-iron components withstand abrasive soils, extreme heat, and rugged field terrains without structural warping. |
| Local Serviceability | Simple mechanical systems ensure that repairs can be conducted by local mechanics, keeping spare part costs exceptionally low. |
| Calibrated Fuel Dynamics | High-displacement engines are designed to reach peak torque at lower RPMs, directly reducing overall diesel consumption. |
| Ergonomic Enhancements | Features like power steering, digital instrument displays, and comfortable deluxe seating reduce physical fatigue during long harvest shifts. |
| Resilient Market Valuation | Due to consistent demand in the secondary market, these models retain high resale values even after several seasons of intense use. |
Conclusion
Swaraj’s mid-range portfolio—consisting of the 744 XT, 735 FE, 742 XT, 744 FE, and 855 FE—presents practical options for expanding agricultural operations. Every tractor in this lineup serves a distinct operational purpose, ranging from the highly economical 735 FE intended for smaller utility tasks to the robust 855 FE designed for intensive field applications.
By prioritizing verified engine capacities, precise lifting limits, and localized pricing structures, you can confidently select a reliable asset that will support your farm across multiple planting and harvesting seasons. Which specific implements or primary farm applications are you planning to pair with your new tractor?
-
Business3 years ago
Cybersecurity Consulting Company SequelNet Provides Critical IT Support Services to Medical Billing Firm, Medical Optimum
-
Entertainment3 years ago
Meet the Megalodon: The Shark Star of ‘Meg 2’
-
Entertainment3 years ago
Reduce Video Game Lag: Level Up Your Gaming Performance
-
Sports3 years ago
Balancing India’s Entertainment: Cricket vs. Bollywood
-
Entertainment3 years ago
Jetsetter’s Secrets: Unveiling Our Favorite Travel Hacks for a Seamless Adventure
-
Productivity3 years ago
The 5 Best Live Sports Streaming Sites: Legal and Exciting!
-
Art /Entertainment3 years ago
Hollywood Labor Unrest: The Impact of ‘What About Us?’ Strikes
-
Sports3 years ago
Unveiling the Magic of Dream Fulfillment at the Late NBA Draft





























