Technology
How to Delete Private Browsing History and Protect Your Privacy

Private Browsing History and Protect Your Privacy
In today’s digital age, privacy is a valuable commodity, and many of us turn to incognito or Private Browsing mode to shield our online activities. However, the illusion of complete anonymity that incognito mode provides can be deceptive. In this article, we’ll explore why incognito mode falls short in protecting your privacy and, more importantly, how to delete your private browsing history effectively. We’ll also delve into expert-recommended practices to safeguard your digital footprint. Let’s dive in.
Is Incognito Mode Truly Private?
When you activate incognito mode in your web browser, it’s easy to assume that your online actions become invisible to prying eyes. Regrettably, this isn’t entirely accurate. Your Internet Service Provider (ISP) and third-party entities can still trace your online activity, even while you’re in private browsing mode. If you share your device with others, they can also uncover your incognito browsing history. So, how is this possible?
How Is Your Browsing History Saved in Incognito Mode?
While incognito mode does prevent your browser from saving your web queries and visited websites, it’s not a foolproof method for private browsing. Your ISP continues to collect and store data about your online activities, including the websites you visit, even when using incognito mode.
Moreover, some websites may track your IP address, circumventing your browser’s attempts at anonymity. Even if your history isn’t saved locally, other services and websites may retain records of your visits.
To complicate matters further, your device maintains a DNS cache of your browsing session, whether in normal or incognito mode. This cache includes domain names and their associated IP addresses, making it accessible to anyone using your computer. To fortify your privacy, it’s crucial to eliminate your DNS cache and erase all traces of your browsing session.

Image by https://www.makeuseof.com/
Can Private Browsing History Be Tracked?
In essence, private browsing, such as incognito mode, aims to prevent your browser from storing your browsing history, cookies, and site data. However, it doesn’t offer complete anonymity. Your ISP and certain websites can still monitor your online activities, leaving your browsing history susceptible to tracking.
Deleting Incognito History: Step by Step
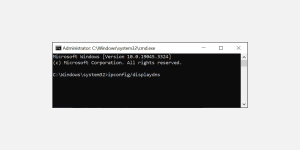
Viewing Private Browsing History on Windows PC
To view your private browsing history on a Windows PC, follow these steps:
- Press Windows + R to open the Run Command Window.
- Type “cmd” and press Ctrl + Shift + Enter to launch the Command Prompt with administrative privileges.
- In the command prompt window, type “ipconfig/displaydns” and press Enter.
Image by https://www.makeuseof.com/
A list of recently accessed websites will appear with their IP addresses. This includes websites visited in both private browsing and normal browsing mode.
Image by https://www.makeuseof.com/
This will display a list of recently accessed websites, encompassing both private and normal browsing history.
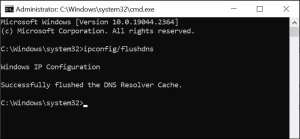
How to Delete Incognito History on a PC
When you’ve finished your private browsing session, it’s important to delete any traces of your incognito history from the DNS cache.
Here is how to do that on a Windows PC:
- Press Windows + R to launch Run Command Window.
- Type “cmd” in the Run dialogue box and press Ctrl + Shift + Enter to open the Command Prompt with administrative rights.
Image by https://www.makeuseof.com/
In the command prompt window, type “ipconfig/flushdns” and press the Enter key.
Image by https://www.makeuseof.com/
This will delete your DNS cache and clear all traces of your recent browsing session.
Viewing Incognito History on Android and iOS
On Android and iOS devices, official methods to view incognito history are limited. However, you can use third-party apps like FamilyTime, KidsGuard, or Hoverwatch to access incognito history. Note that while you can view it, you cannot delete it or access previous incognito records.
How to Delete Incognito History on Android
The steps to delete incognito history on an Android device are quite simple. All you need to do is use the Chrome browser and follow these steps to clear the DNS cache:
- On your Android device, launch the Chrome browser.
- In the address bar, type “chrome://net-internals/#dns” and hit Enter.
- Tap the Clear host cache button to delete the device’s DNS cache.
- Close Chrome
- Image by https://www.makeuseof.com/
- Image by https://www.makeuseof.com/
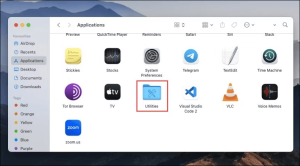
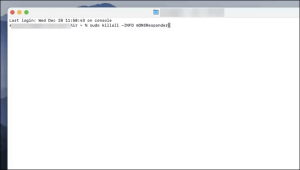
How to Delete Incognito History on Mac
On Mac devices, you can easily flush the DNS cache and delete your incognito browsing history by using the Terminal command.
Here is how to do that:
- On your Mac device, launch Applications, and select Utilities.
Image by https://www.makeuseof.com/
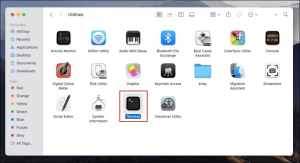
Under Utilities, look for the Terminal and double-click on it to launch it.
Image by https://www.makeuseof.com/
In the Terminal window, type the command, “sudo killall -HUP mDNSResponder“, and hit the enter key. You will be asked to enter your password to continue.
Image by https://www.makeuseof.com/
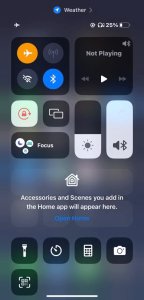
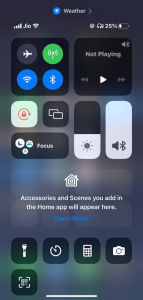
How to Clear Incognito History on iPhone
If you use an iPhone, it’s easy to clear the DNS cache, thereby deleting your private browsing history. You just have to toggle the Airplane Mode On and Off. Here is how to do that:
- On your iPhone, swipe down from the top-right corner of the screen to expand Control Center.
- Tap on the Airplane Mode icon to toggle it on.
- Wait for a few seconds and then toggle it off again
- Image by https://www.makeuseof.com/
- Image by https://www.makeuseof.com/
This will delete all the accumulated DNS cache from your device and clear your private browsing history.
Privately Browsing the Internet: Best Practices
If you’re committed to browsing the web privately, consider the following strategies:
- Install a Reliable VPN: A Virtual Private Network (VPN) encrypts your internet traffic and conceals your IP address, enhancing online privacy.
- Use a Secure Web Browser: Opt for secure browsers like Tor to maximize online privacy and security.
- Utilize a Private Search Engine: Switch to private-focused search engines like DuckDuckGo to safeguard your browsing history.
- Regularly Clear Browsing Data: Remove browsing data from your devices periodically to eliminate session traces.
- Delete Your DNS Cache: Routinely clear your DNS cache to erase records of recent website visits, even in incognito mode.
How Often Should You Clear Your DNS Cache?
The frequency of clearing your DNS cache should align with your browsing habits, especially if you frequently use incognito mode or value online privacy. Regularly deleting your DNS cache helps minimize third-party knowledge about your browsing activities.
Protect Your Privacy
While incognito mode offers a layer of privacy, it’s not a silver bullet for complete anonymity. To protect your digital footprint comprehensively, employ a reliable VPN, choose secure browsers, and consistently clear your browsing data and DNS cache. By taking these steps, you’ll empower yourself to navigate the digital realm with greater confidence and privacy.
About the Author
Pranav Bhardwaj is an expert in online privacy and cybersecurity. With over a decade of experience, Pranav has provided valuable insights to individuals and organizations seeking to protect their digital presence. His expertise in the field makes him a trusted authority on online privacy.
In conclusion, while incognito mode provides a degree of privacy, it’s not infallible. To truly safeguard your online activities, follow the expert advice provided in this article. By understanding how to delete private browsing history effectively and implementing best practices, you can take control of your digital privacy. Your online presence is worth protecting, and with the right knowledge, you can do just that.
Digital Development
Columbus Digital Marketing: Help Moving Companies Grow Online

The moving industry has become increasingly competitive, making it harder for businesses to stand out and attract new customers. Most people searching for movers begin their journey online, comparing companies, reading reviews, and requesting quotes before making a decision. For moving businesses that want to capture these potential customers, investing in professional digital marketing is no longer optional. This is where Columbus Digital Marketing Services can make a significant difference.
By combining search engine optimization, local marketing, content creation, and paid advertising, moving companies can increase their online visibility and generate a steady stream of qualified leads.
Online Visibility Matters
When homeowners or businesses need moving services, they usually search Google using phrases such as “moving company near me” or “local movers in Columbus.” If your company does not appear on the first page of search results, potential customers may never discover your business.
A professional Columbus Digital Marketing Company helps moving businesses improve their online presence by targeting the keywords and search terms customers use most often. The goal is to place your company in front of people actively looking for moving services, increasing the likelihood of inquiries and bookings.
Importance of Moving Company SEO
One of the most effective digital marketing strategies for movers is Moving Company SEO. Search engine optimization focuses on improving a website’s visibility in organic search results, helping businesses attract traffic without relying solely on paid advertisements.
SEO strategies for moving companies typically include:
- Optimizing service pages with location-specific keywords
- Improving website speed and mobile usability
- Creating valuable blog content related to moving tips
- Building high-quality backlinks
- Optimizing Google Business Profile listings
- Managing online reviews and local citations
These efforts help search engines understand your website and improve its rankings for relevant searches. Over time, a strong SEO strategy can generate consistent leads while reducing customer acquisition costs.
Local SEO Helps Reach Customers
Most moving companies serve specific cities or regions, making local SEO a crucial part of any marketing strategy. Columbus Digital Marketing Services often focus heavily on local optimization because it connects businesses with customers in their target service areas.
Local SEO involves optimizing location-based keywords, maintaining accurate business listings, and encouraging customer reviews. When executed properly, these efforts increase visibility in Google Maps and local search results, making it easier for nearby customers to find your business.
For moving companies, appearing in local search results often leads to higher-quality inquiries because users are actively searching for services in their area.
Content Marketing Builds Trust
Customers want confidence before hiring movers to handle their belongings. Educational content helps establish credibility and demonstrates expertise.
A trusted Columbus Digital Marketing Company can create blog posts, guides, and resources covering topics such as packing tips, moving checklists, relocation planning, and storage solutions. This content not only helps potential customers but also supports SEO efforts by targeting additional search terms.
When visitors find useful information on your website, they are more likely to trust your company and request a quote.
Paid Advertising Delivers Faster Results
While SEO provides long-term growth, paid advertising can generate immediate visibility. Google Ads and social media advertising allow moving companies to target customers actively searching for relocation services.
By combining PPC campaigns with Moving Company SEO, businesses create a balanced marketing strategy that delivers both short-term leads and sustainable long-term growth. Paid advertising can be especially valuable during peak moving seasons when competition for customers is highest.
Strengthening Brand Awareness Online
Digital marketing is about more than rankings and clicks. Consistent branding across websites, social media platforms, and online directories helps moving companies establish a professional image.
Through customized campaigns, Columbus Digital Marketing Services help businesses showcase their experience, customer satisfaction, and service quality. Strong brand recognition often leads to more referrals, repeat customers, and positive reviews.
Success of Your Digital Marketing Efforts
One of the biggest advantages of working with a Columbus Digital Marketing Company is the ability to track and measure marketing performance. Unlike traditional advertising, digital marketing provides detailed insights into how customers find and interact with your business online.
Key performance indicators such as website traffic, keyword rankings, lead submissions, phone calls, and conversion rates help moving companies understand which strategies are delivering results. Regular reporting allows business owners to identify opportunities for improvement and make data-driven decisions.
Professional Columbus Digital Marketing Services also use analytics tools to monitor customer behavior on a website. By understanding which pages attract the most visitors and generate the highest number of inquiries, marketing campaigns can be refined for better performance.
When combined with effective Moving Company SEO, continuous performance tracking helps moving businesses maximize their return on investment while maintaining steady growth in an increasingly competitive online marketplace.
Conclusion
Growing a moving business in today’s digital landscape requires more than traditional advertising methods. Customers expect to find trustworthy movers online, compare options, and make informed decisions quickly. By investing in Columbus Digital Marketing Services, moving companies can improve visibility, attract qualified leads, and build a stronger reputation.
Whether through local search optimization, content marketing, paid advertising, or Moving Company SEO, partnering with an experienced Columbus Digital Marketing Company can provide the tools and strategies needed to achieve long-term online growth and stay ahead of the competition.
Technology
Video & Audio Converters: Formats, Quality, and Best Practices
Whether you’re editing a home movie, preparing a podcast, or sharing media across different devices, video & audio converters have become essential tools for everyday digital life. These utilities let you transform media files from one format to another without losing quality making them indispensable for creators, students, and professionals alike. If you’ve ever wondered how to choose the right converter or what formats to use, this guide answers your most important questions.
Format Compatibility and File Types
What is the difference between a video container and a codec?
A container (like MP4 or MKV) is essentially a wrapper that holds the video, audio, and subtitle tracks together in one file. The codec (like H.264 or AAC) is the technology that actually compresses and encodes the data inside that container. Recognizing this difference when utilizing video and audio converters aids you in selecting the appropriate output configurations for your requirements.
Which video formats are the most universally supported?
MP4 with H.264 encoding is the gold standard for compatibility, playing smoothly on virtually every device, browser, and platform. AVI and MOV are also widely recognized, though they tend to produce larger file sizes. For web streaming or sharing on social media, MP4 is almost always the safest choice.
What audio formats should I use for the best quality?
FLAC and WAV are lossless formats that preserve every detail of the original recording, making them ideal for music production and archiving. MP3 and AAC are lossy but deliver excellent quality at much smaller file sizes, which suits streaming, podcasting, and casual listening. Most online video & audio converters support all of these formats.
Can I convert audio extracted directly from a video file?
Yes most modern converters allow you to strip the audio track from a video and save it as a standalone MP3, AAC, or FLAC file. This is especially useful when you want just the soundtrack from a tutorial, a lecture recording, or a music video. The process is fast and does not require any advanced technical knowledge.
Performance, Quality, and Best Practices
Does converting a file multiple times reduce quality?
With lossy formats like MP3 or H.264, each conversion introduces a small amount of quality degradation a process sometimes called “generation loss.” To avoid this, always work from the original high-quality source file and convert only once to your final target format. Lossless formats like FLAC and WAV do not suffer from generation loss.
How do I reduce file size without sacrificing too much quality?
Lowering the bitrate is the most effective way to shrink a file — just be mindful that going too low will cause noticeable blurring or audio distortion. For video, adjusting the resolution (for example, from 4K to 1080p) also dramatically reduces file size. An effective video and audio converter will allow you to preview or gauge the output file size prior to finalizing the conversion.
How long does a typical file conversion take?
Conversion speed depends on the file size, output format, and the processing power of the device or server handling the task. Short clips under five minutes typically convert in seconds, while longer videos may video & audio converters take several minutes. Online powered by cloud servers are often faster than running software locally on older hardware.
Is it safe to use free online converters?
Reputable online converter platforms process your file and deliver the output without storing your data permanently. Always choose a trusted website look for HTTPS, a clear privacy policy, and positive user reviews. Avoid uploading sensitive or personal files to any converter service you haven’t verified.
Use Cases and Practical Applications
How do video & audio converters help content creators?
Video & audio converters allow creators to export projects in the exact format required by each platform whether that’s YouTube, Instagram, TikTok, or a podcast directory. Different platforms have different codec, resolution, and bitrate requirements, and a reliable converter bridges those gaps instantly. This saves hours of re-exporting from editing software.
Can I use converters to make media accessible on older devices?
Absolutely. Older televisions, car stereo systems, and legacy media players often only support specific formats like AVI, MP3, or WMV. Converting modern files into these older formats ensures your media plays back without errors on any device. This is one of the most practical everyday uses of a video & audio converter.
Are there converters designed specifically for batch processing?
Yes many professional-grade tools and some online platforms allow you to queue multiple files and convert them all at once. Batch conversion is a major time-saver when you need to standardize a library of media files or prepare assets for a project. Look for this feature if you regularly handle large volumes of video or audio content.
What is the best way to convert video for use in a presentation?
For presentations, WMV or MP4 are the most reliable formats since they embed cleanly into PowerPoint and Google Slides. Keep the resolution at 1080p or lower to prevent lag during playback, and use a moderate bitrate to keep the file size manageable. A high-quality video and audio converter will provide you with accurate control over all these configurations.
Conclusion
Video & audio converters are powerful, practical tools that remove the barriers between different media formats and the devices or platforms you use every day. Whether you’re a casual user converting a single clip or a creator managing hundreds of files, the right converter makes the process seamless and efficient. Visit multiconverters.net to access a full suite of fast, reliable video & audio converters no downloads required.
Technology
MB to GB Converter: Guide to Understanding Digital Storage Units
Whether you’re checking your phone’s storage, downloading a large file, or comparing cloud plans, understanding how to convert megabytes to gigabytes is a skill that comes up more often than you’d think. An MB to GB converter takes the guesswork out of this process, giving you instant, accurate results without doing the math yourself. Let’s break down everything you need to know.
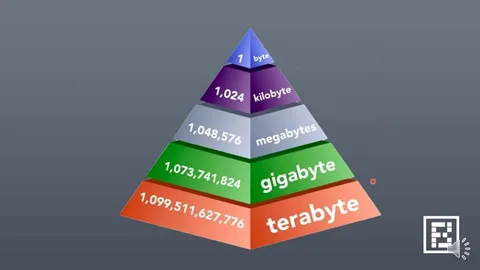
Understanding the Basics of Digital Storage
What is a megabyte (MB)?
A megabyte is a unit of digital information equal to 1,024 kilobytes in the binary system used by computers. In everyday terms, a single MP3 song typically takes up around 3 to 5 MB, making it a commonly referenced unit for small-to-medium file sizes.
What is a gigabyte (GB)?
A gigabyte is significantly larger than a megabyte it equals 1,024 megabytes in the binary system. Most modern smartphones, laptops, and storage devices are now measured in gigabytes or even terabytes, reflecting how much digital data we consume daily.
What is the difference between MB and GB?
The key difference is scale. One gigabyte contains 1,024 megabytes, which means GB describes much larger quantities of data. Knowing this distinction helps you make smarter decisions when buying storage, choosing a data plan, or downloading files.
Why do computers use 1,024 instead of 1,000?
Computers operate in binary (base-2), so storage units are calculated in powers of 2. Since 2 to the power of 10 equals 1,024, each step up in storage measurement from KB to MB to GB multiplies by 1,024 rather than a round 1,000.
How to Convert MB to GB
How do you convert megabytes to gigabytes manually?
To convert MB to GB, simply divide the number of megabytes by 1,024. For example, 2,048 MB divided by 1,024 gives you exactly 2 GB. This formula works reliably whether you’re dealing with file sizes, RAM, or storage capacity.
How does an MB to GB converter work?
An online MB to GB converter automates this division instantly. You enter the value in megabytes, click convert, and the tool returns the equivalent in gigabytes no calculator needed. Tools like the one on multiconverters.net handle this in real time, saving you time and eliminating human error.
Can you convert GB back to MB?
Yes converting GB to MB is just as simple. Multiply the number of gigabytes by 1,024 to get the megabyte equivalent. So 5 GB equals 5,120 MB, which is useful when comparing storage specs or data caps that use different units.
What is 1,000 MB in GB?
Strictly speaking in binary terms, 1,000 MB equals approximately 0.976 GB. However, in decimal (SI) terms used by many hard drive manufacturers 1,000 MB equals exactly 1 GB. This slight discrepancy is why your device sometimes shows less storage than advertised.
Real-World Applications of MB and GB
How many MB is a typical movie file?
A standard-definition movie typically ranges from 700 MB to 1.5 GB, while a high definition film can easily reach 4 to 8 GB. Knowing these figures helps you plan storage space or estimate how long a download will take on your internet connection.
What is the data consumption of streaming services each hour?
Streaming in standard definition uses roughly 1 GB per hour, while HD streaming can consume 3 GB or more per hour. If your mobile data plan is measured in GB, using an MB to GB converter helps you track usage more intuitively.
A typical smartphone photo taken at 12 megapixels is around 3 to 5 MB. That means 1 GB of storage can hold roughly 200 to 330 photos. Knowing this helps you decide when to back up your gallery or invest in extra cloud storage.
Why does my phone show less storage than it advertises?
Manufacturers often use the decimal definition of a gigabyte (1 GB = 1,000 MB), while your phone’s operating system uses the binary definition (1 GB = 1,024 MB). This gap explains why a “128 GB” device may display only around 119 GB of usable space.
Choosing the Right Tools for Unit Conversion
When should you use an online converter instead of manual math?
An online MB to GB converter is the smarter choice when dealing with large or irregular numbers that are tedious to divide manually. It’s also ideal when you need to convert multiple values quickly or when precision matters, such as in technical or professional settings.
Are all MB to GB converters equally accurate?
Not all converters clearly specify whether they use binary (1,024) or decimal (1,000) as the base. A trustworthy tool will clearly disclose the system it employs and deliver results that align with how your operating system assesses storage. Consistently verify the approach of the tool if precision is essential.
Conclusion
Understanding digital storage doesn’t have to be complicated. A good MB to GB converter removes the friction from everyday data decisions whether you’re managing files, comparing devices, or keeping tabs on your data plan. Bookmark a trusted tool like multiconverters.net so you always have fast, accurate conversions at your fingertips.
-
Business3 years ago
Cybersecurity Consulting Company SequelNet Provides Critical IT Support Services to Medical Billing Firm, Medical Optimum
-
Business3 years ago
Team Communication Software Transforms Operations at Finance Innovate
-
Business3 years ago
Project Management Tool Transforms Long Island Business
-
Business3 years ago
How Alleviate Poverty Utilized IPPBX’s All-in-One Solution to Transform Lives in New York City
-
health3 years ago
Breast Cancer: The Imperative Role of Mammograms in Screening and Early Detection
-
Sports3 years ago
Unstoppable Collaboration: D.C.’s Citi Open and Silicon Valley Classic Unite to Propel Women’s Tennis to New Heights
-
Art /Entertainment3 years ago
Embracing Renewal: Sizdabedar Celebrations Unite Iranians in New York’s Eisenhower Park
-
Finance3 years ago
The Benefits of Starting a Side Hustle for Financial Freedom